Network, Information and Computer Security Lab
NICS Lab is an international leading Security research group led by Javier Lopez, Full Professor of the Computer Science Department at University of Malaga. NICS is composed of 20 persons, including faculty members, post-doc researchers, top PhD students, and technical and management staff, all belonging to a Research institute ITIS Software, being distributed on two different locations, the Ada Byron Research Building at the extension of Campus Teatinos and the Computer Science Department at Campus Teatinos.
The research activities of the group started back in 1994, when Prof. Lopez published his first research work on electronic mail security in Local Area Networks, followed by others on probabilistic primality tests for public keys, and public-key directories security based on Neural Networks. Since then, NICS members have published over 300 publications, among them more than 60 journal publications with impact factor (ISI-ranked).
Additionally, NICS members have participated in more than 50 security research projects at international and national level, funded by V, VI and VII European Frameworks Programmes as well as by different Ministries in Spain, Japan, Norway and Singapore.
NICS Lab actively participates in international committees and Working Groups in the Security area, as well as in the organization of multiple international conferences and workshops. Moreover, NICS is particularly dynamic in the exchange of researchers with other research institutions, having signed official scientific and technical cooperation agreements in US with NIST (Information Technology Laboratory, Computer Security Division), and in Singapore with I2R (Cryptography & Security Department).
Over the years, NICS members have been especially active in technology transfer to companies like ATOS Origin, HP Labs, Telefonica, France Telecom, Siemens, Indra, Banesto, Orange, Endesa, Sermepa and Telvent, as well as to public entities like the Spanish Ministry of Defense, the Andalusian Government, and RedIRIS (Spanish advanced communications network for academic and R+D Centres).
last news
last publications
Qinyang Miao, Wen Sun, Dan Zhu, Jinku Li, Yajin Zhou, Cristina Alcaraz
Moderation is the Best Policy: Dynamic Defense Against Gradient-Based Data Reconstruction Attacks in Federated Learning Forthcoming
In: EEE Transactions on Dependable and Secure Computing, pp. 1-17, Forthcoming, ISSN: 1941-0018.
@article{Alcaraz2:2026c,
title = {Moderation is the Best Policy: Dynamic Defense Against Gradient-Based Data Reconstruction Attacks in Federated Learning},
author = {Qinyang Miao and Wen Sun and Dan Zhu and Jinku Li and Yajin Zhou and Cristina Alcaraz },
url = {https://ieeexplore.ieee.org/document/11387021},
doi = {https://doi.org/10.1109/TDSC.2026.3656886},
issn = {1941-0018},
year = {2026},
date = {2026-12-31},
urldate = {2026-12-31},
journal = {EEE Transactions on Dependable and Secure Computing},
pages = {1-17},
abstract = {Federated learning (FL) is a privacy-preserving distributed machine learning framework. However, recent studies have shown that implementing gradient-based data reconstruction attacks (DRA) can still lead to the leakage of user privacy through frequently uploaded model parameters in FL. Existing works leverage differential privacy (DP) to prevent privacy leakage, but the lack of effective scheduling of the privacy budget results in significant accuracy loss in the trained models. In this paper, we propose a novel dynamic privacy preserving federated learning framework, named NDPP-FL, capable of delivering robust defenses against DRA while significantly mitigating performance loss. Our key insight is to regard the privacy budget as a non-replenishable resource and dynamically schedule it based on privacy leakage risks to provide self-adaptive privacy protection for clients across varying communication rounds. Specifically, based on the amount of information between the local dataset and the transmitted parameters, we first design a parameter channel information leakage model. Then, during each update iteration, we introduce saliency perturbations based on the Hessian matrix to enhance defensive capabilities. Meanwhile, to improve the performance of NDPP-FL, sample-adaptive clipping and decaying noise perturbations are adopted in the construction. Furthermore, extensive experiments demonstrate that our framework performs excellently in terms of model accuracy and resilience against DRA.},
keywords = {},
pubstate = {forthcoming},
tppubtype = {article}
}
Cristina Alcaraz, Javier Lopez, Alberto Garcia
Situational awareness for trustworthy charging scenarios Forthcoming
In: International Journal of Critical Infrastructure Protection, vol. 53, pp. 100846, Forthcoming, ISSN: 1874-5482.
@article{Alcaraz2026b,
title = {Situational awareness for trustworthy charging scenarios},
author = {Cristina Alcaraz and Javier Lopez and Alberto Garcia},
url = {/wp-content/papers/Alcaraz2026b.pdf
https://www.sciencedirect.com/science/article/pii/S1874548226000181},
doi = {10.1016/j.ijcip.2026.100846},
issn = {1874-5482},
year = {2026},
date = {2026-07-31},
urldate = {2026-07-31},
journal = {International Journal of Critical Infrastructure Protection},
volume = {53},
pages = {100846},
abstract = {Growing acceptance of Electric Vehicles (EVs) by society is reshaping the transportation sector, which requires the development of robust charging infrastructures. Unfortunately, at present these infrastructures face multiple security challenges due to the complexities involved in integrating information systems with operational systems, which also leads to numerous security vulnerabilities and expands the attack surface. In response to this issue, this paper proposes a distributed Multi-Agent System (MAS) leveraging (i) smart consensus algorithms backed by Opinion Dynamics and (ii) blockchain technology to ensure trustworthy tracking of anomalies in EV charging networks based on the well-known Open Charge Point Protocol. The combined use of techniques and technologies streamlines diagnostic processes at charging stations, but also intensifies the vision (both local and global) necessary for greater protection. The monitoring method goes beyond the usual approaches, which typically focus on network traffic with a local context approach. It is capable of examining local health status related to anomalies found in individual devices, (i) analyzing each operational component and communication link, and (ii) contrasting actual perceptions with those perceived by the neighborhood. This way of broadening the security vision inherently contributes to situational awareness, explaining: where, what, or which components, devices, or charging zones are actually affected. This level of detail can even help ensure a more effective, efficient, and rapid responses depending on the situation.},
keywords = {},
pubstate = {forthcoming},
tppubtype = {article}
}
Cristina Alcaraz, Hector Guzman, Javier Lopez
Adaptive Digital Twin: Protection, deception, and testing
In: Future Generation Computer Systems, vol. 179, pp. 108357, 2026, ISSN: 0167-739X.
@article{Alcaraz2026a,
title = {Adaptive Digital Twin: Protection, deception, and testing},
author = {Cristina Alcaraz and Hector Guzman and Javier Lopez},
url = {/wp-content/papers/Alcaraz2026a.pdf
https://www.sciencedirect.com/science/article/pii/S0167739X2500651X?via%3Dihub},
doi = {10.1016/j.future.2025.108357},
issn = {0167-739X},
year = {2026},
date = {2026-06-30},
urldate = {2026-06-30},
journal = {Future Generation Computer Systems},
volume = {179},
pages = {108357},
abstract = {A Digital Twin (DT) is a cutting-edge technology that has gained relevance in recent years, demonstrating huge potential for the simulation of processes and the provision of valuable insights to improve and optimise systems. Leveraging a high degree of fidelity in replicating real-world processes, DTs are being explored for advanced applications such as deception and proactive protection of critical infrastructures. However, this same advantage also raises concerns with respect to a system’s exposure, as the detailed digital representation may introduce new cybersecurity risks. With the aim of assisting the growth of this technology, this paper presents an adaptive DT solution that facilitates the configuration of particular components of the digital system, tailoring different application scenarios specifically for protection, deception, and testing purposes. Finally, the proposed architecture is tested under a specific IoT-oriented use case to validate, experiment, and extract conclusions of the proposed solution.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Pablo Gutierrez-Felix, Marc Manzano, Javier Lopez
Quantum-Resistant Pairing Evaluation for Resource-Constrained Bluetooth Classic
In: Internet of Things, vol. 37, pp. 101947, 2026, ISSN: 2542-6605.
@article{pablogf2026,
title = {Quantum-Resistant Pairing Evaluation for Resource-Constrained Bluetooth Classic},
author = {Pablo Gutierrez-Felix and Marc Manzano and Javier Lopez},
url = {/wp-content/papers/pablogf2026.pdf
https://www.sciencedirect.com/science/article/pii/S2542660526000776},
doi = {10.1016/j.iot.2026.101947},
issn = {2542-6605},
year = {2026},
date = {2026-05-01},
urldate = {2026-05-01},
journal = {Internet of Things},
volume = {37},
pages = {101947},
publisher = {Elsevier},
abstract = {The security of state-of-the-art Bluetooth pairing relies on Elliptic Curve Diffie-Hellman (ECDH), which is vulnerable to quantum attacks. However, the feasibility of integrating standardized Post-Quantum Cryptographic (PQC) primitives into the controller-level Bluetooth Classic (BC) protocol stack remains an open question. This paper presents the first comprehensive evaluation of integrating a post-quantum secure key exchange for BC pairing. We analyze the impact of replacing the existing ECDH-based key establishment with NIST-standardized PQC Key Encapsulation Mechanisms (KEMs), focusing on protocol-level packetization, over-the-air transmission overhead, and execution performance in constrained hardware. Using BC’s Link Manager Protocol (LMP) and DM1 packet structure, we quantify Public Parameter Transmission (PPT) latency for classical and post-quantum schemes. We further benchmark ECDH and ML-KEM implementations on an ARM Cortex-M4 microcontroller with characteristics comparable to those of constrained Bluetooth controllers. Our results show that ML-KEM is computationally feasible on such hardware, often matching or outperforming classical ECDH in execution time. However, PQC significantly increases over-the-air overhead. Under ML-KEM, PPT accounts for 60-75% of total key exchange latency, compared to less than 10% for ECDH. Code-based schemes such as HQC are shown to be impractical due to excessive memory and transmission requirements under provided hardware constraints. These findings indicate that the primary obstacle to post-quantum Bluetooth pairing is not computation but wireless packetization, reliability, and energy consumption; facilitating a safe and efficient quantum-secure migration of resource-constrained wireless communication settings.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Iman Hasnaouia Meskini, Cristina Alcaraz, Rodrigo Roman, Javier Lopez
Analysis of Transferable Adversarial Evasion Attack Detection in IoT and Industrial ADS
In: IEEE Open Journal of the Computer Society, vol. 7, pp. 142-153, 2025.
BibTeX | Links:
@article{iman2025,
title = {Analysis of Transferable Adversarial Evasion Attack Detection in IoT and Industrial ADS},
author = {Iman Hasnaouia Meskini and Cristina Alcaraz and Rodrigo Roman and Javier Lopez},
url = {/wp-content/papers/iman2025.pdf},
doi = {10.1109/OJCS.2025.3649157},
year = {2025},
date = {2025-12-26},
urldate = {2025-12-26},
journal = {IEEE Open Journal of the Computer Society},
volume = {7},
pages = {142-153},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Javier Parada, Cristina Alcaraz, Javier Lopez, Juan Caubet, Rodrigo Roman
Digital Twin for Adaptive Adversary Emulation in IIoT Control Networks
In: 30th European Symposium on Research in Computer Security (ESORICS 2025), Toulouse, France , Springer, 2025, ISBN: 978-3-032-07893-3.
BibTeX | Links:
@inproceedings{parada2025digital,
title = {Digital Twin for Adaptive Adversary Emulation in IIoT Control Networks},
author = {Javier Parada and Cristina Alcaraz and Javier Lopez and Juan Caubet and Rodrigo Roman},
url = {https://doi.org/10.1007/978-3-032-07894-0_22},
doi = {10.1007/978-3-032-07894-0_22},
isbn = {978-3-032-07893-3},
year = {2025},
date = {2025-10-18},
urldate = {2025-10-18},
booktitle = {30th European Symposium on Research in Computer Security (ESORICS 2025), Toulouse, France },
volume = {16055},
publisher = {Springer},
series = {LNCS},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Zero-Knowledge Bitcoin Mixer with Reversible Unlinkability
In: Blockchain: Research and Applications, 2025.
@article{morales2025mixer,
title = {Zero-Knowledge Bitcoin Mixer with Reversible Unlinkability},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2025mixer.pdf},
doi = {10.1016/j.bcra.2025.100323},
year = {2025},
date = {2025-07-01},
urldate = {2025-07-01},
journal = {Blockchain: Research and Applications},
abstract = {Cryptocurrencies, particularly Bitcoin, continue to be the most prevalent use case within the blockchain ecosystem. One of the inherent limitations of blockchain is that it can create a false sense of privacy. All transaction history and the amount of cryptocurrency held are publicly available, and this information can be easily associated with specific individuals. Many works have proposed fully-private solutions, which are ideal but not realistic in many scenarios. This paper proposes a technical solution that enables private Bitcoin payments by default, but with the option to conditionally disclose payment data. To do so, this solution relies on unlinkability by a decentralized mixer, which can be reversed by a conditional discloser using a trapdoor unlinkability function. The conditional discloser, which also provides accountability of requests, obeys the payer’s policies regarding who can access payment data. To ensure compliance, we propose a mixer that does not learn anything about the payment link, but is guaranteed by Zero-Knowledge Proofs that the payment can be relinked by a specific conditional discloser. Furthermore, we provide a proof-of-concept implementation of the proofs, using Circom and SnarkJS. We also present a benchmark that demonstrates the feasibility of this solution. It incurs only one additional parameter per on-chain transaction, while the remainder of the verification data is managed off-chain.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Antonio Muñoz, Javier Lopez, Cristina Alcaraz, Fabio Martinelli
Trusted Platform and Privacy Management in Cyber Physical Systems: The DUCA Framework
In: IFIP Annual Conference on Data and Applications Security and Privacy, Springer, 2025.
@inproceedings{munoz2025trusted,
title = {Trusted Platform and Privacy Management in Cyber Physical Systems: The DUCA Framework},
author = {Antonio Mu\~{n}oz and Javier Lopez and Cristina Alcaraz and Fabio Martinelli},
url = {/wp-content/papers/munoz2025trusted.pdf},
doi = {10.1007/978-3-031-96590-6_12},
year = {2025},
date = {2025-06-23},
urldate = {2025-06-23},
booktitle = {IFIP Annual Conference on Data and Applications Security and Privacy},
volume = { 15722},
publisher = {Springer},
series = {LNCS},
abstract = {his paper explores the application of the DUCA (Data Usage Control and Compliance Architecture) framework for privacy management in Cyber-Physical Systems (CPS). DUCA integrates Privacy-by-Design (PbD) principles, Privacy-Enhancing Technologies (PETs), and context-aware policy enforcement to support regulatory compliance and protect data throughout its lifecycle. A key focus of this work is the integration of Secure Elements (SEs)\textemdashincluding Trusted Execution Environments
(TEE), Trusted Platform Modules (TPM), and Intel SGX\textemdashto enable privacy protection during data processing, complementing traditional safeguards for data at rest and in transit. The framework also supports emerging standards such as DICE and MARS to facilitate scalable trust management in heterogeneous CPS environments. We present DUCA’s modular architecture and evaluate its applicability across representative use cases, including smart grids, eHealth, and AI-enabled infrastructures,
demonstrating its effectiveness in enforcing privacy without compromising functionality.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
(TEE), Trusted Platform Modules (TPM), and Intel SGX—to enable privacy protection during data processing, complementing traditional safeguards for data at rest and in transit. The framework also supports emerging standards such as DICE and MARS to facilitate scalable trust management in heterogeneous CPS environments. We present DUCA’s modular architecture and evaluate its applicability across representative use cases, including smart grids, eHealth, and AI-enabled infrastructures,
demonstrating its effectiveness in enforcing privacy without compromising functionality.
Cristina Alcaraz, Davide Ferraris, Héctor Guzmán, Javier Lopez
Blockchain-based Multi-Signature System for Critical Scenarios
In: 22nd International Conference on Security and Cryptography (SECRYPT 2025), pp. 221-232, 2025, ISBN: 978-989-758-760-3.
BibTeX | Links:
@inproceedings{alcarazBlock25,
title = {Blockchain-based Multi-Signature System for Critical Scenarios},
author = {Cristina Alcaraz and Davide Ferraris and H\'{e}ctor Guzm\'{a}n and Javier Lopez},
url = {/wp-content/papers/alcarazBlock25.pdf},
doi = {10.5220/0013559000003979},
isbn = {978-989-758-760-3},
year = {2025},
date = {2025-06-13},
urldate = {2025-06-13},
booktitle = {22nd International Conference on Security and Cryptography (SECRYPT 2025)},
pages = {221-232},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Pablo Sanchez-Serrano, Ruben Rios, Isaac Agudo
A decision framework for privacy-preserving synthetic data generation
In: Computers and Electrical Engineering, vol. 126, pp. 110468, 2025, ISSN: 0045-7906.
@article{Sanchez-Serrano2025,
title = {A decision framework for privacy-preserving synthetic data generation},
author = {Pablo Sanchez-Serrano and Ruben Rios and Isaac Agudo},
url = {/wp-content/papers/Sanchez-Serrano2025.pdf
https://www.sciencedirect.com/science/article/pii/S0045790625004112},
doi = {10.1016/j.compeleceng.2025.110468},
issn = {0045-7906},
year = {2025},
date = {2025-06-13},
urldate = {2025-06-13},
journal = {Computers and Electrical Engineering},
volume = {126},
pages = {110468},
abstract = {Access to realistic data is essential for various purposes, including training machine learning models, conducting simulations, and supporting data-driven decision making across diverse domains. However, the use of real data often raises significant privacy concerns, as it may contain sensitive or personal information. Generative models have emerged as a promising solution to this problem by generating synthetic datasets that closely resemble real data. Nevertheless, these models are typically trained on original datasets, which carries the risk of leaking sensitive information. To mitigate this issue, privacy-preserving generative models have been developed to balance data utility and privacy guarantees. This paper examines existing generative models for synthetic tabular data generation, proposing a taxonomy of solutions based on the privacy guarantees they provide. Additionally, we present a decision framework to aid in selecting the most suitable privacy-preserving generative model for specific scenarios, using privacy and utility metrics as key selection criteria.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
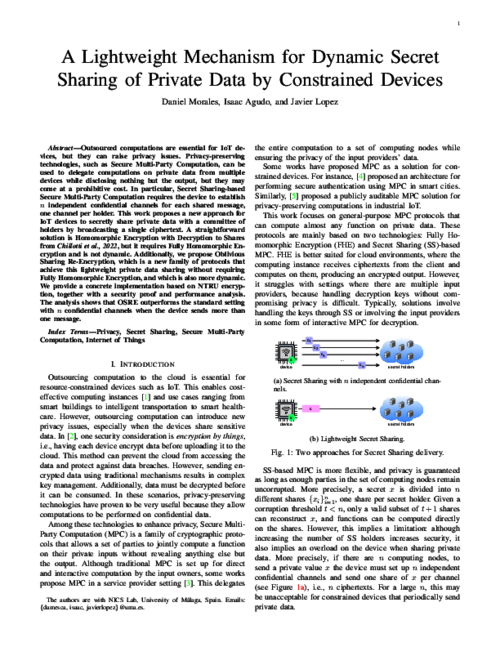
Daniel Morales, Isaac Agudo, Javier Lopez
A Lightweight Mechanism for Dynamic Secret Sharing of Private Data by Constrained Devices
In: IEEE Internet of Things Journal, 2025, ISSN: 2327-4662.
@article{morales2025iot,
title = {A Lightweight Mechanism for Dynamic Secret Sharing of Private Data by Constrained Devices},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2025iot.pdf},
doi = {10.1109/JIOT.2025.3555026},
issn = {2327-4662},
year = {2025},
date = {2025-03-26},
urldate = {2025-03-26},
journal = {IEEE Internet of Things Journal},
abstract = {Outsourced computations are essential for IoT devices, but they can raise privacy issues. Privacy-preserving technologies, such as Secure Multi-Party Computation, can be used to delegate computations on private data from multiple devices while disclosing nothing but the output, but they may come at a prohibitive cost. In particular, Secret Sharing-based Secure Multi-Party Computation requires the device to establish n independent confidential channels for each shared message, one channel per holder. This work proposes a new approach for IoT devices to secretly share private data with a committee of holders by broadcasting a single ciphertext. A straightforward solution is Homomorphic Encryption with Decryption to Shares from Chillotti et al., 2022, but it requires Fully Homomorphic Encryption and is not dynamic. Additionally, we propose Oblivious Sharing Re-Encryption, which is a new family of protocols that achieve this lightweight private data sharing without requiring Fully Homomorphic Encryption, and which is also more dynamic. We provide a concrete implementation based on NTRU encryption, together with a security proof and performance analysis. The analysis shows that OSRE outperforms the standard setting with n confidential channels when the device sends more than one message.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Javier Lopez
Digital Twin Security: A Perspective on Efforts From Standardization Bodies
In: IEEE Security & Privacy, vol. 23, iss. 1, pp. 83-90, 2025, ISSN: 1558-4046.
@article{Alcaraz2025a,
title = {Digital Twin Security: A Perspective on Efforts From Standardization Bodies},
author = {Cristina Alcaraz and Javier Lopez},
url = {/wp-content/papers/Alcaraz2025a.pdf
https://www.computer.org/csdl/magazine/sp/2025/01/10871233/2448764c2l2},
doi = {10.1109/MSEC.2024.3504193},
issn = {1558-4046},
year = {2025},
date = {2025-01-01},
urldate = {2025-01-01},
journal = {IEEE Security \& Privacy},
volume = {23},
issue = {1},
pages = {83-90},
abstract = {This article assesses the contributions of standardization bodies to digital twin (DT) protection and analyzes whether and how the organizations prioritize security. It identifies standardization work that better covers different security requirements, hence offering higher guarantees of DT protection.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Javier Lopez
Digital Twin-assisted anomaly detection for industrial scenarios
In: International Journal of Critical Infrastructure Protection, vol. 47, pp. 100721, 2024, ISSN: 1874-5482.
@article{Alcaraz2024c,
title = {Digital Twin-assisted anomaly detection for industrial scenarios},
author = {Cristina Alcaraz and Javier Lopez},
url = {https://www.sciencedirect.com/science/article/pii/S1874548224000623},
doi = {https://doi.org/10.1016/j.ijcip.2024.100721},
issn = {1874-5482},
year = {2024},
date = {2024-12-01},
urldate = {2024-12-01},
journal = {International Journal of Critical Infrastructure Protection},
volume = {47},
pages = {100721},
abstract = {Industry 5.0 is the current industrial paradigm that inherits the technological diversity of its predecessor, Industry 4.0, but includes three priority goals: (i) resilience, (ii) sustainability and (iii) human-centeredness. Through these three goals, Industry 5.0 pursues a more far-reaching digital transformation in industrial ecosystems with high protection guarantees. However, the deployment of innovative information technologies for this new digital transformation also requires considering their implicit vulnerabilities and threats in order to avoid any negative impacts on the three Industry 5.0 goals, and to prioritize cybersecurity aspects so as to ensure acceptable protection levels. This paper, therefore, proposes a detection framework composed of a Digital Twin (DT) and machine learning algorithms for online protection, supporting the resilience that Industry 5.0 seeks. To validate the approach, this work includes several practical studies on a real industrial control testbed to demonstrate the feasibility and accuracy of the framework, taking into account a set of malicious perturbations in several critical sections of the system. The results highlight the effectiveness of the DT in complementing the anomaly detection processes, especially for advanced and stealthy threats.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Iman Hasnaouia Meskini, Javier Lopez
Digital twin communities: an approach for secure DT data sharing
In: International Journal of Information Security, vol. 24, no. 17, 2024, ISSN: 1615-5270.
@article{AlcarazMeskiniLopez2024,
title = {Digital twin communities: an approach for secure DT data sharing},
author = {Cristina Alcaraz and Iman Hasnaouia Meskini and Javier Lopez},
url = {https://link.springer.com/article/10.1007/s10207-024-00912-1#citeas},
doi = {https://doi.org/10.1007/s10207-024-00912-1},
issn = {1615-5270},
year = {2024},
date = {2024-11-07},
urldate = {2024-11-07},
journal = {International Journal of Information Security},
volume = {24},
number = {17},
abstract = {Digital Twin (DT) technology empowers organizations to create virtual counterparts of their physical assets, thereby magnifying their analytical, optimization and decision-making capabilities. More specifically, the simulation capabilities of a DT generate high-quality data that not only benefit the DT owner organization, but also increase the potential of similar organizations by leveraging the DT’s capabilities when sharing its simulation results This collaborative sharing boosts the capabilities of each participating organization, fostering a collective intelligence that amplifies their competitive advantage. Nonetheless, data exchange must rigorously safeguard each organization’s data confidentiality, and access to this data must be thoroughly controlled. Thus, this paper introduces the novel concept of DT communities and proposes a hybrid access control architecture. This architecture seamlessly integrates the strengths of both Role Based Access Control (RBAC) and Organizational Based Access Control (OrBAC), facilitating secure, authorized intra- and inter-organizational information sharing in the context of Industry 5.0, combining the strengths of local DT communication and other organization’s DTs as well. Moreover, in order to show the feasibility of the approach for critical corporate organizations and their systems, in this paper we provide a proof-of-concept implementation of this architecture. To validate its functionality and efficiency, we perform a number of experimental studies showing how various entities can benefit from securely sharing DT models based on the concept of “community".},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Toward a Framework for Cost-Effective and Publicly Verifiable Confidential Computations in Blockchain
In: IEEE Communications Magazine, 2024, ISSN: 1558-1896.
@article{morales2024commag,
title = {Toward a Framework for Cost-Effective and Publicly Verifiable Confidential Computations in Blockchain},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2024commag.pdf},
doi = {10.1109/MCOM.001.2300839},
issn = {1558-1896},
year = {2024},
date = {2024-09-03},
urldate = {2024-09-03},
journal = {IEEE Communications Magazine},
abstract = {Blockchain technologies have introduced a compelling paradigm for a new understanding of security through decentralized networks and consensus mechanisms. However, they need all data to be public, which may be unacceptable for use cases such as biometric data processing or sensitive monetary transactions. Therefore, confidentiality is identified as a need in blockchain. Additionally, blockchain can contribute to confidential applications by providing publicly verifiable mechanisms, therefore enhancing security. This work presents a framework for cost-effective and publicly verifiable confidential computations in blockchain, by relying on secure multi-party computation committees and zero-knowledge proofs. Our framework supports arbitrary computations on confidential data enforced by smart contracts. Additionally, staking, incentives, and cheat identification are provided as solutions to enhance trust. We also provide a technical solution to embed secure multi-party computations within smart contracts by using the Promise programming pattern. Finally, a cost analysis is provided to justify the feasibility of the framework compared to other solutions.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Carmen Fernandez-Gago, Davide Ferraris, Rodrigo Roman, Javier Lopez
Trust interoperability in the Internet of Things
In: Internet of Things, vol. 26, 2024.
@article{FerIoT24,
title = {Trust interoperability in the Internet of Things},
author = {Carmen Fernandez-Gago and Davide Ferraris and Rodrigo Roman and Javier Lopez},
url = {/wp-content/papers/FerIoT24.pdf},
doi = {https://doi.org/10.1016/j.iot.2024.101226},
year = {2024},
date = {2024-07-31},
urldate = {2024-07-31},
journal = {Internet of Things},
volume = {26},
abstract = {The Internet of Things (IoT) is a paradigm where entities or things are interconnected, often in heterogeneous contexts. As the interconnection happens, things establish collaborations with others, sometimes under uncertainty. Although trust can help us overcome this uncertainty, things might not be able to process the information about trust coming from other things: each thing could have its own trust model, which means its own way to understand and measure trust. If new trust relationships are to be established, it would be desirable to have a mechanism of interoperability that allows the things to process the information about the other things in terms of trust. In this paper, we describe an interoperability framework for tackling the trust interoperability issues in IoT, depending on the different types of trust models that might co-exist in the same IoT scenario.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Panagiotis Bountakas, Konstantinos Fysarakis, Thomas Kyriakakis, Panagiotis Karafotis, Sotiropoulos Aristeidis, Maria Tasouli, Cristina Alcaraz, George Alexandris, Vassiliki Andronikou, Tzortzia Koutsouri, Romarick Yatagha, George Spanoudakis, Sotiris Ioannidis, Fabio Martinelli, Oleg Illiashenko
SYNAPSE - An Integrated Cyber Security Risk & Resilience Management Platform, With Holistic Situational Awareness, Incident Response & Preparedness Capabilities Forthcoming
In: 4th International Workshop on Advances on Privacy Preserving Technologies and Solutions(IWAPS) , Forthcoming.
@inproceedings{Alcaraz2024a,
title = {SYNAPSE - An Integrated Cyber Security Risk \& Resilience Management Platform, With Holistic Situational Awareness, Incident Response \& Preparedness Capabilities},
author = {Panagiotis Bountakas, Konstantinos Fysarakis, Thomas Kyriakakis, Panagiotis Karafotis, Sotiropoulos Aristeidis, Maria Tasouli, Cristina Alcaraz, George Alexandris, Vassiliki Andronikou, Tzortzia Koutsouri, Romarick Yatagha, George Spanoudakis, Sotiris Ioannidis, Fabio Martinelli, Oleg Illiashenko},
url = {https://www.ares-conference.eu/iwaps},
year = {2024},
date = {2024-07-31},
urldate = {2024-07-31},
booktitle = {4th International Workshop on Advances on Privacy Preserving Technologies and Solutions(IWAPS) },
abstract = {In an era of escalating cyber threats, the imperative for robust and comprehensive cybersecurity measures has never been more pressing. To address this challenge, SYNAPSE presents a pioneering approach by conceptualising, designing, and delivering an Integrated Cyber Security Risk \& Resilience Management Platform. This platform embodies a holistic framework, synthesising key elements of situational awareness, incident response, and preparedness (i.e., cyber range), augmented by advanced AI capabilities. Through its holistic approach, SYNAPSE aims to elevate cyber resilience by not only mitigating threats but also fostering a culture of proactive defence, informed decision-making, and collaborative response within organisations and across industries.},
keywords = {},
pubstate = {forthcoming},
tppubtype = {inproceedings}
}
Andrew D. Syrmakesis, Cristina Alcaraz, Nikos D. Hatziargyriou
DAR-LFC: A data-driven attack recovery mechanism for Load Frequency Control
In: International Journal of Critical Infrastructure Protection, vol. 45, iss. 100678, pp. 100678, 2024, ISSN: 1874-5482.
@article{SYRMAKESIS2024100678,
title = {DAR-LFC: A data-driven attack recovery mechanism for Load Frequency Control},
author = {Andrew D. Syrmakesis and Cristina Alcaraz and Nikos D. Hatziargyriou},
url = {https://www.sciencedirect.com/science/article/pii/S1874548224000192?dgcid=rss_sd_all},
doi = {https://doi.org/10.1016/j.ijcip.2024.100678},
issn = {1874-5482},
year = {2024},
date = {2024-07-01},
urldate = {2024-07-01},
journal = {International Journal of Critical Infrastructure Protection},
volume = {45},
issue = {100678},
pages = {100678},
abstract = {In power systems, generation must be maintained in constant equilibrium with consumption. A key indicator for this balance is the frequency of the power grid. The load frequency control (LFC) system is responsible for maintaining the frequency close to its nominal value and the power deviation of tie-lines at their scheduled levels. However, the remote communication system of LFC exposes it to several cyber threats. A successful cyberattack against LFC attempts to affect the field measurements that are transferred though its remote control loop. In this work, a data-driven, attack recovery method is proposed against denial of service and false data injection attacks, called DAR-LFC. For this purpose, a deep neural network is developed that generates estimations of the area control error (ACE) signal. When a cyberattack against the LFC occurs, the proposed estimator can temporarily compute and replace the affected ACE, mitigating the effects of the cyberattacks. The effectiveness and the scalability of the DAR-LFC is verified on a single and a two area LFC simulations in MATLAB/Simulink.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Javier Lopez
Protecting Digital Twin Networks for 6G-enabled Industry 5.0 Ecosystems
In: IEEE Network Magazine, vol. 37, no. 2, pp. 302-308, 2023, ISSN: 0890-8044.
@article{Alcaraz2023a,
title = {Protecting Digital Twin Networks for 6G-enabled Industry 5.0 Ecosystems},
author = {Cristina Alcaraz and Javier Lopez},
url = {/wp-content/papers/Alcaraz2023a.pdf
https://ieeexplore.ieee.org/abstract/document/10239369},
doi = {10.1109/MNET.004.2200529},
issn = {0890-8044},
year = {2023},
date = {2023-12-31},
urldate = {2023-12-31},
journal = {IEEE Network Magazine},
volume = {37},
number = {2},
pages = {302-308},
publisher = {IEEE},
abstract = {New industrial paradigms, such as the Industrial Internet of Things (IIoT) and Industry 5.0, are emerging in industrial contexts with the aim of fostering quality in operational processes. With the expected launch of 6G in the coming years, IIoT networks in Industry 5.0 ecosystems can leverage 6G technology and its support for training machine learning models using Digital Twins (DTs), embedded in DT Networks (DTNs), to transparently and continuously optimize their communications. Unfortunately, the use of these technologies, in turn, intensifies the attack surface and poses a serious threat to the new goals of Industry 5.0, such as improving the user experience, sustainability and resilience. This article therefore proposes a layered protection framework for 6G-enabled IIoT environments, where not only DTs and DTNs are fully protected, but also the whole 6G ecosystem, complying with the expected goals of Industry 5.0. To achieve this, the framework identifies for each protection layer a set of security and privacy services to subsequently relate them to existing computing infrastructures (cloud, edge, edge-cloud) and provide the best approach for future IIoT deployments.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Integration of MPC into Besu through an extended private transaction model
In: IEEE International Conference on Metaverse Computing, Networking and Applications, pp. 266-273, IEEE Computer Society IEEE, Kyoto, Japan, 2023.
@inproceedings{morales2023metacom,
title = {Integration of MPC into Besu through an extended private transaction model},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2023metacom.pdf},
doi = {10.1109/MetaCom57706.2023.00056},
year = {2023},
date = {2023-06-01},
urldate = {2023-06-01},
booktitle = {IEEE International Conference on Metaverse Computing, Networking and Applications},
pages = {266-273},
publisher = {IEEE},
address = {Kyoto, Japan},
organization = {IEEE Computer Society},
abstract = {In the last few years we have seen many different approaches to incorporate privacy features to blockchains. In the area of cryptocurrencies that would normally mean protecting the identity of the owner of some funds, but there are other applications where privacy is even more important, especially in permissioned blockchains.
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu’s design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu’s design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.
Cristina Alcaraz, Jesus Cumplido, Alicia Triviño
OCPP in the spotlight: threats and countermeasures for electric vehicle charging infrastructures 4.0
In: International Journal of Information Security, 2023, ISSN: 1615-5262.
@article{Alcaraz2023b,
title = {OCPP in the spotlight: threats and countermeasures for electric vehicle charging infrastructures 4.0},
author = {Cristina Alcaraz and Jesus Cumplido and Alicia Trivi\~{n}o},
url = {/wp-content/papers/Alcaraz2023b.pdf
https://link.springer.com/article/10.1007/s10207-023-00698-8},
doi = {10.1007/s10207-023-00698-8},
issn = {1615-5262},
year = {2023},
date = {2023-05-05},
urldate = {2023-05-05},
journal = {International Journal of Information Security},
publisher = {Springer},
address = {Springer Verlag},
abstract = {Undoubtedly, Industry 4.0 in the energy sector improves the conditions for automation, generation and distribution of energy, increasing the rate of electric vehicle manufacturing in recent years. As a result, more grid-connected charging infrastructures are being installed, whose charging stations (CSs) can follow standardized architectures, such as the one proposed by the open charge point protocol (OCPP). The most recent version of this protocol is v.2.0.1, which includes new security measures at device and communication level to cover those security issues identified in previous versions. Therefore, this paper analyzes OCPP-v2.0.1 to determine whether the new functions may still be susceptible to specific cyber and physical threats, and especially when CSs may be connected to microgrids. To formalize the study, we first adapted the well-known threat analysis methodology, STRIDE, to identify and classify threats in terms of control and energy, and subsequently we combine it with DREAD for risk assessment. The analyses indicate that, although OCPP-v2.0.1 has evolved, potential security risks still remain, requiring greater protection in the future.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Private set intersection: A systematic literature review
In: Computer Science Review, vol. 49, no. 100567, 2023, ISSN: 1574-0137.
@article{morales2023psi,
title = {Private set intersection: A systematic literature review},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2023psi.pdf
https://www.sciencedirect.com/science/article/pii/S1574013723000345},
doi = {10.1016/j.cosrev.2023.100567},
issn = {1574-0137},
year = {2023},
date = {2023-05-01},
urldate = {2023-05-01},
journal = {Computer Science Review},
volume = {49},
number = {100567},
publisher = {Elsevier},
address = {ScienceDirect},
abstract = {Secure Multi-party Computation (SMPC) is a family of protocols which allow some parties to compute a function on their private inputs, obtaining the output at the end and nothing more. In this work, we focus on a particular SMPC problem named Private Set Intersection (PSI). The challenge in PSI is how two or more parties can compute the intersection of their private input sets, while the elements that are not in the intersection remain private. This problem has attracted the attention of many researchers because of its wide variety of applications, contributing to the proliferation of many different approaches. Despite that, current PSI protocols still require heavy cryptographic assumptions that may be unrealistic in some scenarios. In this paper, we perform a Systematic Literature Review of PSI solutions, with the objective of analyzing the main scenarios where PSI has been studied and giving the reader a general taxonomy of the problem together with a general understanding of the most common tools used to solve it. We also analyze the performance using different metrics, trying to determine if PSI is mature enough to be used in realistic scenarios, identifying the pros and cons of each protocol and the remaining open problems.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Rodrigo Roman, Cristina Alcaraz, Javier Lopez, Kouichi Sakurai
Current Perspectives on Securing Critical Infrastructures’ Supply Chains
In: IEEE Security & Privacy, vol. 21, no. 4, pp. 29-38, 2023, ISSN: 1540-7993.
BibTeX | Links:
@article{Roman2023a,
title = {Current Perspectives on Securing Critical Infrastructures’ Supply Chains},
author = {Rodrigo Roman and Cristina Alcaraz and Javier Lopez and Kouichi Sakurai},
url = {/wp-content/papers/Roman2023a.pdf},
doi = {10.1109/MSEC.2023.3247946},
issn = {1540-7993},
year = {2023},
date = {2023-03-08},
urldate = {2023-03-08},
journal = {IEEE Security \& Privacy},
volume = {21},
number = {4},
pages = {29-38},
publisher = {IEEE},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Antonio Muñoz, Ruben Rios, Rodrigo Roman, Javier Lopez
A survey on the (in)security of Trusted Execution Environments
In: Computers & Security, pp. 103-180, 2023, ISSN: 0167-4048.
@article{MUNOZ2023103180,
title = {A survey on the (in)security of Trusted Execution Environments},
author = {Antonio Mu\~{n}oz and Ruben Rios and Rodrigo Roman and Javier Lopez},
url = {/wp-content/papers/MUNOZ2023103180.pdf
https://www.sciencedirect.com/science/article/pii/S0167404823000901},
doi = {10.1016/j.cose.2023.103180},
issn = {0167-4048},
year = {2023},
date = {2023-01-01},
urldate = {2023-01-01},
journal = {Computers \& Security},
pages = {103-180},
publisher = {Elsevier},
address = {In Press},
abstract = {As the number of security and privacy attacks continue to grow around the world, there is an ever increasing need to protect our personal devices. As a matter of fact, more and more manufactures are relying on Trusted Execution Environments (TEEs) to shield their devices. In particular, ARM TrustZone (TZ) is being widely used in numerous embedded devices, especially smartphones, and this technology is the basis for secure solutions both in industry and academia. However, as shown in this paper, TEE is not bullet-proof and it has been successfully attacked numerous times and in very different ways. To raise awareness among potential stakeholders interested in this technology, this paper provides an extensive analysis and categorization of existing vulnerabilities in TEEs and highlights the design flaws that led to them. The presented vulnerabilities, which are not only extracted from existing literature but also from publicly available exploits and databases, are accompanied by some effective countermeasures to reduce the likelihood of new attacks. The paper ends with some appealing challenges and open issues.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Antonio Muñoz, Carmen Fernandez-Gago, Roberto Lopez-Villa
A Test Environment for Wireless Hacking in Domestic IoT Scenarios
In: Mobile Networks and Applications, 2022, ISSN: 1383-469X.
BibTeX | Links:
@article{munoz2022,
title = {A Test Environment for Wireless Hacking in Domestic IoT Scenarios},
author = {Antonio Mu\~{n}oz and Carmen Fernandez-Gago and Roberto Lopez-Villa},
url = {/wp-content/papers/munoz2022.pdf},
doi = {10.1007/s11036-022-02046-x},
issn = {1383-469X},
year = {2022},
date = {2022-10-01},
urldate = {2022-10-01},
journal = {Mobile Networks and Applications},
publisher = {Springer},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Jesus Cumplido, Cristina Alcaraz, Javier Lopez
Collaborative anomaly detection system for charging stations
In: The 27th European Symposium on Research in Computer Security (ESORICS 2022), pp. 716–736, Springer, Cham Springer, Cham, 2022.
@inproceedings{Alcaraz2022c,
title = {Collaborative anomaly detection system for charging stations},
author = {Jesus Cumplido and Cristina Alcaraz and Javier Lopez},
url = {/wp-content/papers/Alcaraz2022c.pdf},
doi = {10.1007/978-3-031-17146-8_35},
year = {2022},
date = {2022-09-01},
urldate = {2022-09-01},
booktitle = {The 27th European Symposium on Research in Computer Security (ESORICS 2022)},
volume = {13555},
pages = {716\textendash736},
publisher = {Springer, Cham},
organization = {Springer, Cham},
abstract = {In recent years, the deployment of charging infrastructures has been increasing exponentially due to the high energy demand of electric vehicles, forming complex charging networks. These networks pave the way for the emergence of new unknown threats in both the energy and transportation sectors. Economic damages and energy theft are the most frequent risks in these environments. Thus, this paper aims to present a solution capable of accurately detecting unforeseen events and possible fraud threats that arise during charging sessions at charging stations through the current capabilities of the Machine Learning (ML) algorithms. However, these algorithms have the drawback of not fitting well in large networks and generating a high number of false positives and negatives, mainly due to the mismatch with the distribution of data over time. For that reason, a Collaborative Anomaly Detection System for Charging Stations (here referred to as CADS4CS) is proposed as an optimization measure. CADS4CS has a central analysis unit that coordinates a group of independent anomaly detection systems to provide greater accuracy using a voting algorithm. In addition, CADS4CS has the feature of continuously retraining ML models in a collaborative manner to ensure that they are adjusted to the distribution of the data. To validate the approach, different use cases and practical studies are addressed to demonstrate the effectiveness and efficiency of the solution.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
George Suciu, Aristeidis Farao, Giorgio Bernardinetti, Ivan Palamá, Mari-Anais Sachian, Alexandru Vulpe, Marius-Constantin Vochin, Pavel Muresan, Michail Bampatsikos, Antonio Muñoz, Christos Xenakis
SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform
In: SENSORS, vol. 22, iss. 6527, no. 17, 2022, ISSN: 1424-8220.
@article{suciu2022samgrid,
title = {SAMGRID: Security Authorization and Monitoring Module Based on SealedGRID Platform},
author = {George Suciu and Aristeidis Farao and Giorgio Bernardinetti and Ivan Palam\'{a} and Mari-Anais Sachian and Alexandru Vulpe and Marius-Constantin Vochin and Pavel Muresan and Michail Bampatsikos and Antonio Mu\~{n}oz and Christos Xenakis},
url = {/wp-content/papers/suciu2022samgrid.pdf
https://www.mdpi.com/1424-8220/22/17/6527},
doi = {10.3390/s22176527},
issn = {1424-8220},
year = {2022},
date = {2022-08-30},
urldate = {2022-08-30},
journal = {SENSORS},
volume = {22},
number = {17},
issue = {6527},
abstract = {IoT devices present an ever-growing domain with multiple applicability. This technology has favored and still favors many areas by creating critical infrastructures that are as profitable as possible. This paper presents a hierarchical architecture composed of different licensing entities that manage access to different resources within a network infrastructure. They are conducted on the basis of well-drawn policy rules. At the same time, the security side of these resources is also placed through a context awareness module. Together with this technology, IoT is used and Blockchain is enabled (for network consolidation, as well as the transparency with which to monitor the platform). The ultimate goal is to implement a secure and scalable security platform for the Smart Grid. The paper presents the work undertaken in the SealedGRID project and the steps taken for implementing security policies specifically tailored to the Smart Grid, based on advanced concepts such as Opinion Dynamics and Smart Grid-related Attribute-based Access Control.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Luca Faramondi, Marta Grassi, Simone Guarino, Roberto Setola, Cristina Alcaraz
Configuration vulnerability in SNORT for Windows operating systems
In: 2022 IEEE International Conference on Cyber Security and Resilience (IEEE CSR), pp. 82-89, IEEE IEEE, https://www.ieee-csr.org, 2022, ISBN: 978-1-6654-9952-1.
@inproceedings{1990,
title = {Configuration vulnerability in SNORT for Windows operating systems},
author = {Luca Faramondi and Marta Grassi and Simone Guarino and Roberto Setola and Cristina Alcaraz},
url = {/wp-content/papers/1990.pdf
https://ieeexplore.ieee.org/document/9850309},
doi = {10.1109/CSR54599.2022.9850309},
isbn = {978-1-6654-9952-1},
year = {2022},
date = {2022-08-01},
urldate = {2022-08-01},
booktitle = {2022 IEEE International Conference on Cyber Security and Resilience (IEEE CSR)},
pages = {82-89},
publisher = {IEEE},
address = {https://www.ieee-csr.org},
organization = {IEEE},
abstract = {Cyber-attacks against Industrial Control Systems (ICS) can lead to catastrophic events which can be prevented by the use of security measures such as the Intrusion Prevention Systems (IPS). In this work we experimentally demonstrate how to exploit the configuration vulnerabilities of SNORT one of the most adopted IPSs to significantly degrade the effectiveness of the IPS and consequently allowing successful cyber-attacks. We illustrate how to design a batch script able to retrieve and modify the configuration files of SNORT in order to disable its ability to detect and block Denial of Service (DoS) and ARP poisoning-based Man-In-The-Middle (MITM) attacks against a Programmable Logic Controller (PLC) in an ICS network. Experimental tests performed on a water distribution testbed show that, despite the presence of IPS, the DoS and ARP spoofed packets reach the destination causing respectively the disconnection of the PLC from the ICS network and the modification of packets payload.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Real-time Crowd Counting based on Wearable Ephemeral IDs
In: 19th International Conference on Security and Cryptography (SECRYPT 2022), pp. 249-260, Scitepress Scitepress, Lisbon, 2022, ISSN: 2184-7711.
@inproceedings{morales2022cc,
title = {Real-time Crowd Counting based on Wearable Ephemeral IDs},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2022cc.pdf},
doi = {10.5220/0011327200003283},
issn = {2184-7711},
year = {2022},
date = {2022-07-01},
urldate = {2022-07-01},
booktitle = {19th International Conference on Security and Cryptography (SECRYPT 2022)},
pages = {249-260},
publisher = {Scitepress},
address = {Lisbon},
organization = {Scitepress},
abstract = {Crowd Counting is a very interesting problem aiming at counting people typically based on density averages and/or aerial images. This is very useful to prevent crowd crushes, especially on urban environments with high crowd density, or to count people in public demonstrations. In addition, in the last years, it has become of paramount importance for pandemic management. For those reasons, giving users automatic mechanisms to anticipate high risk situations is essential. In this work, we analyze ID-based Crowd Counting, and propose a real-time Crowd Counting system based on the Ephemeral ID broadcast by contact tracing applications on wearable devices. We also performed some simulations that show the accuracy of our system in different situations.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Davide Ferraris, Carmen Fernandez-Gago, Javier Lopez
Verification and Validation Methods for a Trust-by-Design Framework for the IoT
In: 36th Annual IFIP WG 11.3 Conference on Data and Applications Security and Privacy (DBSec’22), pp. 183-194, Springer Springer, Newark, NJ, USA, 2022, ISBN: 978-3-031-10683-5.
BibTeX | Links:
@inproceedings{1981,
title = {Verification and Validation Methods for a Trust-by-Design Framework for the IoT},
author = {Davide Ferraris and Carmen Fernandez-Gago and Javier Lopez},
url = {/wp-content/papers/1981.pdf
https://link.springer.com/chapter/10.1007/978-3-031-10684-2_11, },
doi = {10.1007/978-3-031-10684-2_11},
isbn = {978-3-031-10683-5},
year = {2022},
date = {2022-07-01},
urldate = {2022-07-01},
booktitle = {36th Annual IFIP WG 11.3 Conference on Data and Applications Security and Privacy (DBSec’22)},
volume = {13383},
pages = {183-194},
publisher = {Springer},
address = {Newark, NJ, USA},
organization = {Springer},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Davide Ferraris, Carmen Fernandez-Gago, Javier Lopez
Novel Approaches for the Development of Trusted IoT Entities
In: 37th International Conference on ICT Systems Security and Privacy Protection – IFIP SEC 2022, pp. 215-230, Springer Springer, Copenhagen, 2022, ISSN: 1868-4238.
BibTeX | Links:
@inproceedings{1980,
title = {Novel Approaches for the Development of Trusted IoT Entities},
author = {Davide Ferraris and Carmen Fernandez-Gago and Javier Lopez},
url = {/wp-content/papers/1980.pdf
https://link.springer.com/content/pdf/10.1007%2F978-3-031-06975-8_13, },
doi = {10.1007/978-3-031-06975-8},
issn = {1868-4238},
year = {2022},
date = {2022-06-01},
urldate = {2022-06-01},
booktitle = {37th International Conference on ICT Systems Security and Privacy Protection \textendash IFIP SEC 2022},
pages = {215-230},
publisher = {Springer},
address = {Copenhagen},
organization = {Springer},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Andrew D. Syrmakesis, Cristina Alcaraz, Nikos D. Hatziargyriou
Classifying resilience approaches for protecting smart grids against cyber threats
In: International Journal of Information Security, vol. 21, pp. 1189–1210, 2022, ISSN: 1615-5262.
@article{Syrmakesis2022,
title = {Classifying resilience approaches for protecting smart grids against cyber threats},
author = {Andrew D. Syrmakesis and Cristina Alcaraz and Nikos D. Hatziargyriou},
url = {/wp-content/papers/Syrmakesis2022.pdf
https://link.springer.com/content/pdf/10.1007/s10207-022-00594-7.pdf},
doi = {https://doi.org/10.1007/s10207-022-00594-7},
issn = {1615-5262},
year = {2022},
date = {2022-05-01},
urldate = {2022-05-01},
journal = {International Journal of Information Security},
volume = {21},
pages = {1189\textendash1210},
publisher = {Springer},
address = {Springer Verlag},
abstract = {Smart grids (SG) draw the attention of cyber attackers due to their vulnerabilities, which are caused by the usage of heterogeneous communication technologies and their distributed nature. While preventing or detecting cyber attacks is a well-studied field of research, making SG more resilient against such threats is a challenging task. This paper provides a classification of the proposed cyber resilience methods against cyber attacks for SG. This classification includes a set of studies that propose cyber-resilient approaches to protect SG and related cyber-physical systems against unforeseen anomalies or deliberate attacks. Each study is briefly analyzed and is associated with the proper cyber resilience technique which is given by the National Institute of Standards and Technology in the Special Publication 800-160. These techniques are also linked to the different states of the typical resilience curve. Consequently, this paper highlights the most critical challenges for achieving cyber resilience, reveals significant cyber resilience aspects that have not been sufficiently considered yet and, finally, proposes scientific areas that should be further researched in order to enhance the cyber resilience of SG.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Xueou Wang, Xiaolu Hou, Ruben Rios, Nils Ole Tippenhauer, Martin Ochoa
Constrained Proximity Attacks on Mobile Targets
In: ACM Transactions on Privacy and Security (TOPS), vol. 25, no. 10, pp. 1 - 29, 2022, ISSN: 2471-2566.
@article{rios2022cpa,
title = {Constrained Proximity Attacks on Mobile Targets},
author = {Xueou Wang and Xiaolu Hou and Ruben Rios and Nils Ole Tippenhauer and Martin Ochoa},
url = {/wp-content/papers/rios2022cpa.pdf},
doi = {10.1145/3498543},
issn = {2471-2566},
year = {2022},
date = {2022-05-01},
urldate = {2022-05-01},
journal = {ACM Transactions on Privacy and Security (TOPS)},
volume = {25},
number = {10},
pages = {1 - 29},
publisher = {Association for Computer Machinery (ACM)},
abstract = {Proximity attacks allow an adversary to uncover the location of a victim by repeatedly issuing queries with fake location data. These attacks have been mostly studied in scenarios where victims remain static and there are no constraints that limit the actions of the attacker. In such a setting, it is not difficult for the attacker to locate a particular victim and quantifying the effort for doing so is straightforward. However, it is far more realistic to consider scenarios where potential victims present a particular mobility pattern. In this paper, we consider abstract (constrained and unconstrained) attacks on services that provide location information on other users in the proximity. We derive strategies for constrained and unconstrained attackers, and show that when unconstrained they can practically achieve success with theoretically optimal effort. We then propose a simple yet effective constraint that may be employed by a proximity service (for example, running in the cloud or using a suitable two-party protocol) as countermeasure to increase the effort for the attacker several orders of magnitude both in simulated and real-world cases.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Javier Lopez
Digital Twin: A Comprehensive Survey of Security Threats
In: IEEE Communications Surveys & Tutorials, vol. 24, no. thirdquarter 2022, pp. 1475 - 1503, 2022, ISSN: 1553-877X.
@article{Alcaraz2022b,
title = {Digital Twin: A Comprehensive Survey of Security Threats},
author = {Cristina Alcaraz and Javier Lopez},
url = {/wp-content/papers/Alcaraz2022b.pdf
https://ieeexplore.ieee.org/document/9765576},
doi = {10.1109/COMST.2022.3171465},
issn = {1553-877X},
year = {2022},
date = {2022-04-01},
urldate = {2022-04-01},
journal = {IEEE Communications Surveys \& Tutorials},
volume = {24},
number = {thirdquarter 2022},
pages = {1475 - 1503},
publisher = {IEEE},
address = {IEEE},
abstract = {Industry 4.0 is having an increasingly positive impact on the value chain by modernizing and optimizing the production and distribution processes. In this streamline, the digital twin (DT) is one of the most cutting-edge technologies of Industry 4.0, providing simulation capabilities to forecast, optimize and estimate states and configurations. In turn, these technological capabilities are encouraging industrial stakeholders to invest in the new paradigm, though an increased focus on the risks involved is really needed. More precisely, the deployment of a DT is based on the composition of technologies such as cyber-physical systems, the Industrial Internet of Things, edge computing, virtualization infrastructures, artificial intelligence and big data. However, the confluence of all these technologies and the implicit interaction with the physical counterpart of the DT in the real world generate multiple security threats that have not yet been sufficiently studied. In that context, this paper analyzes the current state of the DT paradigm and classifies the potential threats associated with it, taking into consideration its functionality layers and the operational requirements in order to achieve a more complete and useful classification. We also provide a preliminary set of security recommendations and approaches that can help to ensure the appropriate and trustworthy use of a DT.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Ishak Meraouche, Sabyasachi Dutta, Sraban Kumar Mohanty, Isaac Agudo, Kouichi Sakurai
Learning multi-party adversarial encryption and its application to secret sharing
In: IEEE Access, 2022, ISSN: 2169-3536.
@article{ishak22,
title = {Learning multi-party adversarial encryption and its application to secret sharing},
author = {Ishak Meraouche and Sabyasachi Dutta and Sraban Kumar Mohanty and Isaac Agudo and Kouichi Sakurai},
url = {/wp-content/papers/ishak22.pdf},
doi = {10.1109/ACCESS.2022.3223430},
issn = {2169-3536},
year = {2022},
date = {2022-01-01},
urldate = {2022-01-01},
journal = {IEEE Access},
publisher = {IEEE},
abstract = {Neural networks based cryptography has seen a significant growth since the introduction of adversarial cryptography which makes use of Generative Adversarial Networks (GANs) to build neural networks that can learn encryption. The encryption has been proven weak at first but many follow up works have shown that the neural networks can be made to learn the One Time Pad (OTP) and produce perfectly secure ciphertexts. To the best of our knowledge, existing works only considered communications between two or three parties. In this paper, we show how multiple neural networks in an adversarial setup can remotely synchronize and establish a perfectly secure communication in the presence of different attackers eavesdropping their communication. As an application, we show how to build Secret Sharing Scheme based on this perfectly secure multi-party communication. The results show that it takes around 45,000 training steps for 4 neural networks to synchronize and reach equilibria. When reaching equilibria, all the neural networks are able to communicate between each other and the attackers are not able to break the ciphertexts exchanged between them.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Ruben Rios, Jose A. Onieva, Rodrigo Roman, Javier Lopez
Personal IoT Privacy Control at the Edge
In: IEEE Security & Privacy, vol. 20, pp. 23 - 32, 2022, ISSN: 1540-7993.
@article{rios2022pmec,
title = {Personal IoT Privacy Control at the Edge},
author = {Ruben Rios and Jose A. Onieva and Rodrigo Roman and Javier Lopez},
url = {/wp-content/papers/rios2022pmec.pdf},
doi = {10.1109/MSEC.2021.3101865},
issn = {1540-7993},
year = {2022},
date = {2022-01-01},
urldate = {2022-01-01},
journal = {IEEE Security \& Privacy},
volume = {20},
pages = {23 - 32},
publisher = {IEEE},
abstract = {This article introduces a privacy manager for IoT data based on Edge Computing. This poses the advantage that privacy is enforced before data leaves the control of the user, who is provided with a tool to express data sharing preferences based on a novel context-aware privacy language.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Francesco Flammini, Cristina Alcaraz, Emanuele Bellini, Stefano Marrone, Javier Lopez, Andrea Bondavalli
Towards Trustworthy Autonomous Systems: Taxonomies and Future Perspectives
In: IEEE Transactions on Emerging Topics in Computing, 2022, ISSN: 2168-6750.
@article{Flamini2022,
title = {Towards Trustworthy Autonomous Systems: Taxonomies and Future Perspectives},
author = {Francesco Flammini and Cristina Alcaraz and Emanuele Bellini and Stefano Marrone and Javier Lopez and Andrea Bondavalli},
url = {/wp-content/papers/Flamini2022.pdf
https://ieeexplore.ieee.org/abstract/document/9979717/authors$#$authors},
doi = {10.1109/TETC.2022.3227113},
issn = {2168-6750},
year = {2022},
date = {2022-01-01},
urldate = {2022-01-01},
journal = {IEEE Transactions on Emerging Topics in Computing},
publisher = {IEEE},
abstract = {The class of Trustworthy Autonomous Systems (TAS) includes cyber-physical systems leveraging on self-x technologies that make them capable to learn, adapt to changes, and reason under uncertainties in possibly critical applications and evolving environments. In the last decade, there has been a growing interest in enabling artificial intelligence technologies, such as advanced machine learning, new threats, such as adversarial attacks, and certification challenges, due to the lack of sufficient explainability. However, in order to be trustworthy, those systems also need to be dependable, secure, and resilient according to well-established taxonomies, methodologies, and tools. Therefore, several aspects need to be addressed for TAS, ranging from proper taxonomic classification to the identification of research opportunities and challenges. Given such a context, in this paper address relevant taxonomies and research perspectives in the field of TAS. We start from basic definitions and move towards future perspectives, regulations, and emerging technologies supporting development and operation of TAS.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Cristina Alcaraz, Jesus Cumplido, Alicia Triviño
Monitorización Segura en Infraestructuras de Carga de Vehículos Eléctricos Frente a Ciber-Ataques
In: Actas del XII International Greencities Congress, Greencities, Inteligencia y Sostenibilidad Urbana, & S-Moving, Movilidad Inteligente y Sostenible, pp. 17-30, FYCMA - Palacio de Ferias y Congresos de Málaga, 2021, ISBN: 978-84-09-19596-1.
@inproceedings{Alcaraz2021m,
title = {Monitorizaci\'{o}n Segura en Infraestructuras de Carga de Veh\'{i}culos El\'{e}ctricos Frente a Ciber-Ataques},
author = {Cristina Alcaraz and Jesus Cumplido and Alicia Trivi\~{n}o},
isbn = {978-84-09-19596-1},
year = {2021},
date = {2021-09-01},
urldate = {2021-09-01},
booktitle = {Actas del XII International Greencities Congress, Greencities, Inteligencia y Sostenibilidad Urbana, \& S-Moving, Movilidad Inteligente y Sostenible},
pages = {17-30},
publisher = {FYCMA - Palacio de Ferias y Congresos de M\'{a}laga},
abstract = {Para alcanzar los objetivos de reducci\'{o}n de emisiones contaminantes, se est\'{a} fomentando en la actualidad la inclusi\'{o}n de nuevas t\'{e}cnicas de generaci\'{o}n, producci\'{o}n y consumo de energ\'{i}a renovable junto con el despliegue eficaz de nuevas t\'{e}cnicas en las redes el\'{e}ctricas inteligentes. Entre estas t\'{e}cnicas, nos encontramos con la gesti\'{o}n de Veh\'{i}culos El\'{e}ctricos (VE) e infraestructuras de Puntos de Carga (PC), que impulsan la movilidad sostenible y act\'{u}an como cargas controlables o como generadores potenciales. Aunque existe mucho inter\'{e}s por desplegar estos tipos de infraestructuras debido a los motivos anteriores, \'{e}stas son muy susceptibles a m\'{u}ltiples tipos de amenazas, especialmente las infraestructuras de PC al ser sistemas que se despliegan en zonas abiertas y accesibles por el p\'{u}blico en general, lo que conlleva a diversos riesgos de seguridad. En la literatura, ya hay varios estudios realizados que demuestran c\'{o}mo las infraestructuras de carga y sus modos de control pueden ser susceptibles a m\'{u}ltiples tipos de ataques, la mayor\'{i}a de ellos causados por el modo de configuraci\'{o}n y el despliegue de los PC y sus infraestructuras de comunicaci\'{o}n para el control.
Dado este escenario, este art\'{i}culo presenta los objetivos de “Urban Lab II”, un proyecto de la Universidad de M\'{a}laga (UMA) que aborda todos estos problemas de seguridad, teniendo en cuenta los beneficios que las nuevas tecnolog\'{i}as de informaci\'{o}n pueden aportar para anticipar anomal\'{i}as o el mal uso de los recursos. Dentro de este proyecto, se han identificado como dos amenazas relevantes relacionadas con las infraestructuras de carga, que son: (i) sobrecalentamiento de componentes por alteraciones maliciosas en los flujos de potencia y (ii) robo de energ\'{i}a y fraude econ\'{o}mico. Para hacer frente a estas amenazas, el presente art\'{i}culo tambi\'{e}n identifica, por un lado, los requisitos de seguridad m\'{a}s representativos que prevengan estas dos amenazas. Adem\'{a}s, se completa este estudio detallando las tecnolog\'{i}as habilitadoras que faciliten no solo la gesti\'{o}n y la monitorizaci\'{o}n eficiente de la energ\'{i}a, sino los objetivos primordiales de estos desaf\'{i}os de seguridad.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Dado este escenario, este artículo presenta los objetivos de “Urban Lab II”, un proyecto de la Universidad de Málaga (UMA) que aborda todos estos problemas de seguridad, teniendo en cuenta los beneficios que las nuevas tecnologías de información pueden aportar para anticipar anomalías o el mal uso de los recursos. Dentro de este proyecto, se han identificado como dos amenazas relevantes relacionadas con las infraestructuras de carga, que son: (i) sobrecalentamiento de componentes por alteraciones maliciosas en los flujos de potencia y (ii) robo de energía y fraude económico. Para hacer frente a estas amenazas, el presente artículo también identifica, por un lado, los requisitos de seguridad más representativos que prevengan estas dos amenazas. Además, se completa este estudio detallando las tecnologías habilitadoras que faciliten no solo la gestión y la monitorización eficiente de la energía, sino los objetivos primordiales de estos desafíos de seguridad.