Isaac Agudo
associate Professor
Edificio de Investigación Ada Byron
C/ Arquitecto Francisco Peñalosa, nº 18
Ampliación Campus de Teatinos. Universidad de Málaga
29071 Málaga (Spain)
Phone: +34 951 952 913
E-mail: isaac@uma.es
Current research
- Secure Multipary Computation: Analisys of current SMPC protocols on specific scenarios with a focus on performance and security trade-offs.
- Applied crypto for Connected Car and Blockchain scenarios: Analysis of current security problems ,and proposal of new solutions, in Blockchain and Connected Car scenarios, in particular with regard to Privacy, Authentication and Confidentiality.
- Digital Identity: New requirements for interoperable identity scheme in the Future Internet, including sovering identity and blockchain solutions. Exploring the possiblities of wearable devices as identity enablers.
- Authentication, Authorization and Delegation: Definition and implementation of privacy frienly autentication mechanisms.
Education
- Ph.D. in Computer Science (with European Doctorate mention), University of Malaga (July 2008).
- MSc. in Mathematics, University of Malaga (July 2002).
- BSc. in Computer Science, UNED, Spain (August 2007).
Principal Investigator
- SAVE: Security plAtform for the internet of VEhicles
- NuCypher USP: NuCypher University Staking Program
- MOTAM: Methods to Optimize Road Transport through Mobile Applications
- DEPHISIT: Experimental Hybrid Platform for Intelligent Transport Systems
- Crypto4BC: Advanced Cryptography for Blockchain Applications
Entrepreneurship
- Founder and CEO of Decentralized Security decentralizedsecurity.es
Patents
- Mikhail Egorov, MacLane Scott Wilkison, David Núñez and Isaac Agudo, “High-performance access management and data protection for distributed messaging applications”, filled in 2018-05-08, granted in 2020-02-25
- Mikhail Egorov, MacLane Scott Wilkison, David Núñez and Isaac Agudo, “Method and system for secure delegated access to encrypted data in big data computing clusters”, filled in 2018-05-08, granted in 2020-03-03
- David Núñez, Isaac Agudo, Mikhail Egorov and MacLane Scott Wilkison, “Method and system for switching public keys in ciphertexts”, filled in 2017-11-29.
- Mikhail Egorov, MacLane Scott Wilkison, David Núñez and Isaac Agudo, “Encryption for distributed storage and processing”, filled in 2017-11-09, granted in 2020-06-23
Relevant publications
Daniel Morales, Isaac Agudo, Javier Lopez
Zero-Knowledge Bitcoin Mixer with Reversible Unlinkability
In: Blockchain: Research and Applications, 2025.
@article{morales2025mixer,
title = {Zero-Knowledge Bitcoin Mixer with Reversible Unlinkability},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2025mixer.pdf},
doi = {10.1016/j.bcra.2025.100323},
year = {2025},
date = {2025-07-01},
urldate = {2025-07-01},
journal = {Blockchain: Research and Applications},
abstract = {Cryptocurrencies, particularly Bitcoin, continue to be the most prevalent use case within the blockchain ecosystem. One of the inherent limitations of blockchain is that it can create a false sense of privacy. All transaction history and the amount of cryptocurrency held are publicly available, and this information can be easily associated with specific individuals. Many works have proposed fully-private solutions, which are ideal but not realistic in many scenarios. This paper proposes a technical solution that enables private Bitcoin payments by default, but with the option to conditionally disclose payment data. To do so, this solution relies on unlinkability by a decentralized mixer, which can be reversed by a conditional discloser using a trapdoor unlinkability function. The conditional discloser, which also provides accountability of requests, obeys the payer’s policies regarding who can access payment data. To ensure compliance, we propose a mixer that does not learn anything about the payment link, but is guaranteed by Zero-Knowledge Proofs that the payment can be relinked by a specific conditional discloser. Furthermore, we provide a proof-of-concept implementation of the proofs, using Circom and SnarkJS. We also present a benchmark that demonstrates the feasibility of this solution. It incurs only one additional parameter per on-chain transaction, while the remainder of the verification data is managed off-chain.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
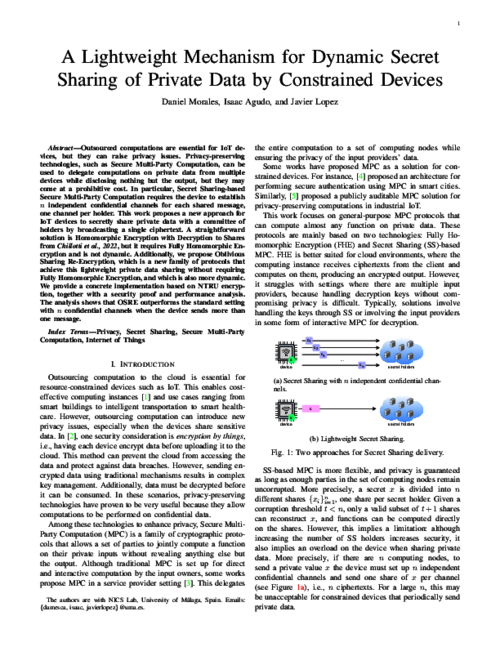
Daniel Morales, Isaac Agudo, Javier Lopez
A Lightweight Mechanism for Dynamic Secret Sharing of Private Data by Constrained Devices
In: IEEE Internet of Things Journal, 2025, ISSN: 2327-4662.
@article{morales2025iot,
title = {A Lightweight Mechanism for Dynamic Secret Sharing of Private Data by Constrained Devices},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2025iot.pdf},
doi = {10.1109/JIOT.2025.3555026},
issn = {2327-4662},
year = {2025},
date = {2025-03-26},
urldate = {2025-03-26},
journal = {IEEE Internet of Things Journal},
abstract = {Outsourced computations are essential for IoT devices, but they can raise privacy issues. Privacy-preserving technologies, such as Secure Multi-Party Computation, can be used to delegate computations on private data from multiple devices while disclosing nothing but the output, but they may come at a prohibitive cost. In particular, Secret Sharing-based Secure Multi-Party Computation requires the device to establish n independent confidential channels for each shared message, one channel per holder. This work proposes a new approach for IoT devices to secretly share private data with a committee of holders by broadcasting a single ciphertext. A straightforward solution is Homomorphic Encryption with Decryption to Shares from Chillotti et al., 2022, but it requires Fully Homomorphic Encryption and is not dynamic. Additionally, we propose Oblivious Sharing Re-Encryption, which is a new family of protocols that achieve this lightweight private data sharing without requiring Fully Homomorphic Encryption, and which is also more dynamic. We provide a concrete implementation based on NTRU encryption, together with a security proof and performance analysis. The analysis shows that OSRE outperforms the standard setting with n confidential channels when the device sends more than one message.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
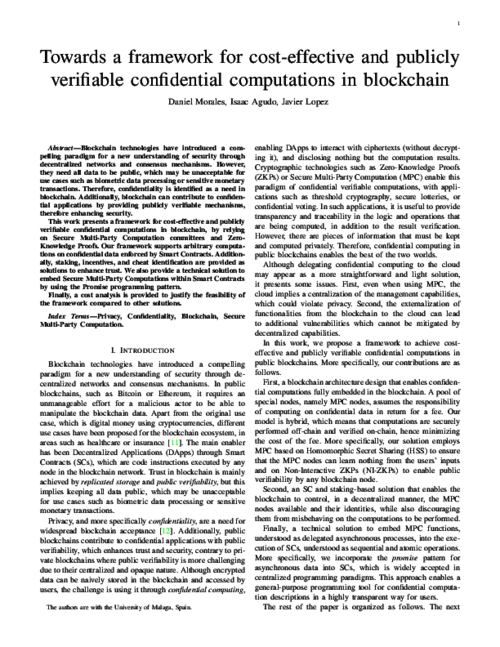
Daniel Morales, Isaac Agudo, Javier Lopez
Toward a Framework for Cost-Effective and Publicly Verifiable Confidential Computations in Blockchain
In: IEEE Communications Magazine, 2024, ISSN: 1558-1896.
@article{morales2024commag,
title = {Toward a Framework for Cost-Effective and Publicly Verifiable Confidential Computations in Blockchain},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2024commag.pdf},
doi = {10.1109/MCOM.001.2300839},
issn = {1558-1896},
year = {2024},
date = {2024-09-03},
urldate = {2024-09-03},
journal = {IEEE Communications Magazine},
abstract = {Blockchain technologies have introduced a compelling paradigm for a new understanding of security through decentralized networks and consensus mechanisms. However, they need all data to be public, which may be unacceptable for use cases such as biometric data processing or sensitive monetary transactions. Therefore, confidentiality is identified as a need in blockchain. Additionally, blockchain can contribute to confidential applications by providing publicly verifiable mechanisms, therefore enhancing security. This work presents a framework for cost-effective and publicly verifiable confidential computations in blockchain, by relying on secure multi-party computation committees and zero-knowledge proofs. Our framework supports arbitrary computations on confidential data enforced by smart contracts. Additionally, staking, incentives, and cheat identification are provided as solutions to enhance trust. We also provide a technical solution to embed secure multi-party computations within smart contracts by using the Promise programming pattern. Finally, a cost analysis is provided to justify the feasibility of the framework compared to other solutions.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Daniel Morales, Isaac Agudo, Javier Lopez
Integration of MPC into Besu through an extended private transaction model
In: IEEE International Conference on Metaverse Computing, Networking and Applications, pp. 266-273, IEEE Computer Society IEEE, Kyoto, Japan, 2023.
@inproceedings{morales2023metacom,
title = {Integration of MPC into Besu through an extended private transaction model},
author = {Daniel Morales and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/morales2023metacom.pdf},
doi = {10.1109/MetaCom57706.2023.00056},
year = {2023},
date = {2023-06-01},
urldate = {2023-06-01},
booktitle = {IEEE International Conference on Metaverse Computing, Networking and Applications},
pages = {266-273},
publisher = {IEEE},
address = {Kyoto, Japan},
organization = {IEEE Computer Society},
abstract = {In the last few years we have seen many different approaches to incorporate privacy features to blockchains. In the area of cryptocurrencies that would normally mean protecting the identity of the owner of some funds, but there are other applications where privacy is even more important, especially in permissioned blockchains.
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu’s design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu’s design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.
Ishak Meraouche, Sabyasachi Dutta, Sraban Kumar Mohanty, Isaac Agudo, Kouichi Sakurai
Learning multi-party adversarial encryption and its application to secret sharing
In: IEEE Access, 2022, ISSN: 2169-3536.
@article{ishak22,
title = {Learning multi-party adversarial encryption and its application to secret sharing},
author = {Ishak Meraouche and Sabyasachi Dutta and Sraban Kumar Mohanty and Isaac Agudo and Kouichi Sakurai},
url = {/wp-content/papers/ishak22.pdf},
doi = {10.1109/ACCESS.2022.3223430},
issn = {2169-3536},
year = {2022},
date = {2022-01-01},
urldate = {2022-01-01},
journal = {IEEE Access},
publisher = {IEEE},
abstract = {Neural networks based cryptography has seen a significant growth since the introduction of adversarial cryptography which makes use of Generative Adversarial Networks (GANs) to build neural networks that can learn encryption. The encryption has been proven weak at first but many follow up works have shown that the neural networks can be made to learn the One Time Pad (OTP) and produce perfectly secure ciphertexts. To the best of our knowledge, existing works only considered communications between two or three parties. In this paper, we show how multiple neural networks in an adversarial setup can remotely synchronize and establish a perfectly secure communication in the presence of different attackers eavesdropping their communication. As an application, we show how to build Secret Sharing Scheme based on this perfectly secure multi-party communication. The results show that it takes around 45,000 training steps for 4 neural networks to synchronize and reach equilibria. When reaching equilibria, all the neural networks are able to communicate between each other and the attackers are not able to break the ciphertexts exchanged between them.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Isaac Agudo, Manuel Montenegro-Gómez, Javier Lopez
A Blockchain Approach for Decentralized V2X (D-V2X)
In: IEEE Transactions on Vehicular Technology, vol. 70, no. 5, pp. 4001 – 4010, 2021, ISSN: 0018-9545.
@article{Agudo2020,
title = {A Blockchain Approach for Decentralized V2X (D-V2X)},
author = {Isaac Agudo and Manuel Montenegro-G\'{o}mez and Javier Lopez},
url = {/wp-content/papers/Agudo2020.pdf},
doi = {10.1109/TVT.2020.3046640},
issn = {0018-9545},
year = {2021},
date = {2021-05-01},
urldate = {2021-05-01},
journal = {IEEE Transactions on Vehicular Technology},
volume = {70},
number = {5},
pages = {4001 - 4010},
publisher = {IEEE},
abstract = {New mobility paradigms have appeared in recent years, and everything suggests that some more are coming. This fact makes apparent the necessity of modernizing the road infrastructure, the signalling elements and the traffic management systems. Many initiatives have emerged around the term Intelligent Transport System (ITS) in order to define new scenarios and requirements for this kind of applications. We even have two main competing technologies for implementing Vehicular communication protocols (V2X), C-V2X and 802.11p, but neither of them is widely deployed yet.
One of the main barriers for the massive adoption of those technologies is governance. Current solutions rely on the use of a public key infrastructure that enables secure collaboration between the different entities in the V2X ecosystem, but given its global scope, managing such infrastructure requires reaching agreements between many parties, with conflicts of interest between automakers and telecommunication operators. As a result, there are plenty of use cases available and two mature communication technologies, but the complexity at the business layer is stopping the drivers from taking advantage of ITS applications.
Blockchain technologies are defining a new decentralized paradigm for most traditional applications, where smart contracts provide a straightforward mechanism for decentralized governance. In this work, we propose an approach for decentralized V2X (D-V2X) that does not require any trusted authority and can be implemented on top of any communication protocol. We also define a proof-of-concept technical architecture on top of a cheap and highly secure System-on-Chip (SoC) that could allow for massive adoption of D-V2X.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
One of the main barriers for the massive adoption of those technologies is governance. Current solutions rely on the use of a public key infrastructure that enables secure collaboration between the different entities in the V2X ecosystem, but given its global scope, managing such infrastructure requires reaching agreements between many parties, with conflicts of interest between automakers and telecommunication operators. As a result, there are plenty of use cases available and two mature communication technologies, but the complexity at the business layer is stopping the drivers from taking advantage of ITS applications.
Blockchain technologies are defining a new decentralized paradigm for most traditional applications, where smart contracts provide a straightforward mechanism for decentralized governance. In this work, we propose an approach for decentralized V2X (D-V2X) that does not require any trusted authority and can be implemented on top of any communication protocol. We also define a proof-of-concept technical architecture on top of a cheap and highly secure System-on-Chip (SoC) that could allow for massive adoption of D-V2X.
David Nuñez, Isaac Agudo, Javier Lopez
Escrowed decryption protocols for lawful interception of encrypted data
In: IET Information Security, vol. 13, pp. 498 – 507, 2019, ISSN: 1751-8709.
@article{nunez19,
title = {Escrowed decryption protocols for lawful interception of encrypted data},
author = {David Nu\~{n}ez and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/nunez19.pdf},
doi = {10.1049/iet-ifs.2018.5082},
issn = {1751-8709},
year = {2019},
date = {2019-09-01},
urldate = {2019-09-01},
journal = {IET Information Security},
volume = {13},
pages = {498 \textendash 507},
publisher = {IET},
abstract = {Escrowed decryption schemes (EDSs) are public-key encryption schemes with an escrowed decryption functionality that allows authorities to decrypt encrypted messages under investigation, following a protocol that involves a set of trusted entities called ‘custodians’; only if custodians collaborate, the requesting authority is capable of decrypting encrypted data. This type of cryptosystem represents an interesting trade-off to privacy versus surveillance dichotomy. In this study, the authors propose two EDSs where they use proxy re-encryption to build the escrowed decryption capability, so that custodians re-encrypt ciphertexts, in a distributed way, upon request from an escrow authority, and the re-encrypted ciphertexts can be opened only by the escrow authority. Their first scheme, called EDS, follows an all-or-nothing approach, which means that escrow decryption only works when all custodians collaborate. Their second scheme, called threshold EDS, supports a threshold number of custodians for the escrow decryption operation. They propose definitions of semantic security with respect to the authorities, custodians and external entities, and prove the security of their schemes, under standard pairing-based hardness assumptions. Finally, they present a theoretical and experimental analysis of the performance of both schemes, which show that they are applicable to real-world scenarios.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
David Nuñez, Isaac Agudo, Javier Lopez
A Parametric Family of Attack Models for Proxy Re-Encryption
In: 28th IEEE Computer Security Foundations Symposium, pp. 290-301, IEEE Computer Society IEEE Computer Society, Verona, Italy, 2015, ISSN: 1063-6900.
@inproceedings{nunez2015parametric,
title = {A Parametric Family of Attack Models for Proxy Re-Encryption},
author = {David Nu\~{n}ez and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/nunez2015parametric.pdf},
doi = {10.1109/CSF.2015.27},
issn = {1063-6900},
year = {2015},
date = {2015-07-01},
urldate = {2015-07-01},
booktitle = {28th IEEE Computer Security Foundations Symposium},
pages = {290-301},
publisher = {IEEE Computer Society},
address = {Verona, Italy},
organization = {IEEE Computer Society},
series = {CSF’15},
abstract = {Proxy Re-Encryption (PRE) is a type of Public-Key Encryption (PKE) which provides an additional re-encryption functionality. Although PRE is inherently more complex than PKE, attack models for PRE have not been developed further than those inherited from PKE. In this paper we address this gap and define a parametric family of attack models for PRE, based on the availability of both the decryption and re-encryption oracles during the security game. This family enables the definition of a set of intermediate security notions for PRE that ranges from ‘‘plain’’ IND-CPA to ‘‘full’’ IND-CCA. We analyze some relations among these notions of security, and in particular, the separations that arise when the re-encryption oracle leaks re-encryption keys. In addition, we discuss which of these security notions represent meaningful adversarial models for PRE. Finally, we provide an example of a recent ‘‘CCA1- secure’’ scheme from PKC 2014 whose security model does not capture chosen-ciphertext attacks through re-encryption and for which we describe an attack under a more realistic security notion. This attack emphasizes the fact that PRE schemes that leak re-encryption keys cannot achieve strong security notions.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
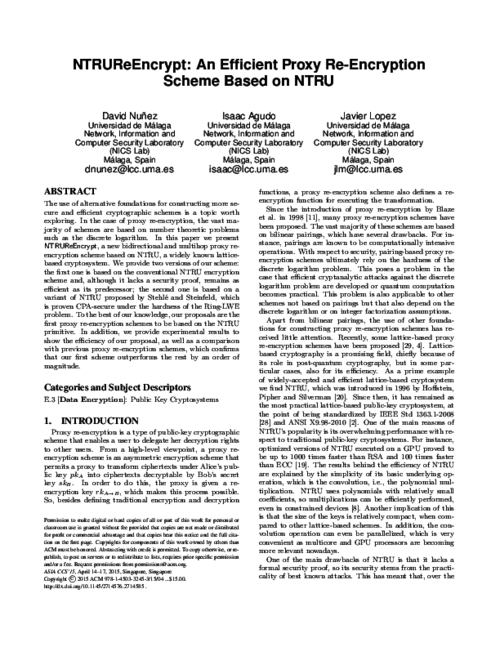
David Nuñez, Isaac Agudo, Javier Lopez
NTRUReEncrypt: An Efficient Proxy Re-Encryption Scheme Based on NTRU
In: 10th ACM Symposium on Information, Computer and Communications Security (AsiaCCS), pp. 179-189, 2015, ISBN: 978-1-4503-3245-3.
@inproceedings{nunez2015ntrureencrypt,
title = {NTRUReEncrypt: An Efficient Proxy Re-Encryption Scheme Based on NTRU},
author = {David Nu\~{n}ez and Isaac Agudo and Javier Lopez},
url = {/wp-content/papers/nunez2015ntrureencrypt.pdf},
doi = {10.1145/2714576.2714585},
isbn = {978-1-4503-3245-3},
year = {2015},
date = {2015-04-01},
urldate = {2015-04-01},
booktitle = {10th ACM Symposium on Information, Computer and Communications Security (AsiaCCS)},
pages = {179-189},
abstract = {The use of alternative foundations for constructing more secure and efficient cryptographic schemes is a topic worth exploring. In the case of proxy re-encryption, the vast majority of schemes are based on number theoretic problems such as the discrete logarithm. In this paper we present NTRUReEncrypt, a new bidirectional and multihop proxy re-encryption scheme based on NTRU, a widely known lattice-based cryptosystem. We provide two versions of our scheme: the first one is based on the conventional NTRU encryption scheme and, although it lacks a security proof, remains as efficient as its predecessor; the second one is based on a variant of NTRU proposed by Stehl\'{e} and Steinfeld, which is proven CPA-secure under the hardness of the Ring-LWE problem. To the best of our knowledge, our proposals are the first proxy re-encryption schemes to be based on the NTRU primitive. In addition, we provide experimental results to show the efficiency of our proposal, as well as a comparison with previous proxy re-encryption schemes, which confirms that our first scheme outperforms the rest by an order of magnitude.},
keywords = {},
pubstate = {published},
tppubtype = {inproceedings}
}
David Nuñez, Isaac Agudo
BlindIdM: A Privacy-Preserving Approach for Identity Management as a Service
In: International Journal of Information Security, vol. 13, pp. 199-215, 2014, ISSN: 1615-5262.
@article{nunez2014blindidm,
title = {BlindIdM: A Privacy-Preserving Approach for Identity Management as a Service},
author = {David Nu\~{n}ez and Isaac Agudo},
url = {/wp-content/papers/nunez2014blindidm.pdf},
doi = {10.1007/s10207-014-0230-4},
issn = {1615-5262},
year = {2014},
date = {2014-01-01},
urldate = {2014-01-01},
journal = {International Journal of Information Security},
volume = {13},
pages = {199-215},
publisher = {Springer},
abstract = {Identity management is an almost indispensable component of today’s organizations and companies, as it plays a key role in authentication and access control; however, at the same time it is widely recognized as a costly and time-consuming task. The advent of cloud computing technologies, together with the promise of flexible, cheap and efficient provision of services, has provided the opportunity to externalize such a common process, shaping what has been called Identity Management as a Service (IDaaS). Nevertheless, as in the case of other cloud-based services, IDaaS brings with it great concerns regarding security and privacy, such as the loss of control over the outsourced data. In this paper we analyze these concerns and propose BlindIdM, a model for privacy-preserving IDaaS with a focus on data privacy protection. In particular, we describe how a SAML-based system can be augmented to employ proxy re-encryption techniques for achieving data con
dentiality with respect to the cloud provider, while preserving the ability to supply the identity service. This is an innovative contribution to both the privacy and identity management landscapes.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Isaac Agudo, Ruben Rios, Javier Lopez
A Privacy-Aware Continuous Authentication Scheme for Proximity-Based Access Control
In: Computers & Security, vol. 39 (B), pp. 117-126, 2013, ISSN: 0167-4048.
@article{agudo2013,
title = {A Privacy-Aware Continuous Authentication Scheme for Proximity-Based Access Control},
author = {Isaac Agudo and Ruben Rios and Javier Lopez},
url = {/wp-content/papers/agudo2013.pdf},
doi = {10.1016/j.cose.2013.05.004},
issn = {0167-4048},
year = {2013},
date = {2013-11-01},
urldate = {2013-11-01},
journal = {Computers \& Security},
volume = {39 (B)},
pages = {117-126},
publisher = {Elsevier},
abstract = {Continuous authentication is mainly associated with the use of biometrics to guarantee that a resource is being accessed by the same user throughout the usage period. Wireless devices can also serve as a supporting technology for continuous authentication or even as a complete alternative to biometrics when accessing proximity-based services. In this paper we present the implementation of a secure, non-invasive continuous authentication scheme supported by the use of Wearable Wireless Devices (WWD), which allow users to gain access to proximity-based services while preserving their privacy. Additionally we devise an improved scheme that circumvents some of the limitations of our implementation.},
keywords = {},
pubstate = {published},
tppubtype = {article}
}
Courses and seminars
- Private seminar on “Blockchain, Distributed Identity and software based key protection and encryption” sponsored by Idfy, May 2019.
- European Intensive Programme on Information & Communication Systems Security (IPICS), September 2012.
- Computer Science Paradigms – Esp. in Information Security. University of la Laguna, November 2012