]
] IEEE Transactions on Emerging Topics in Computing, IEEE, 2022. DOI
Abstract
The class of Trustworthy Autonomous Systems (TAS) includes cyber-physical systems leveraging on self-x technologies that make them capable to learn, adapt to changes, and reason under uncertainties in possibly critical applications and evolving environments. In the last decade, there has been a growing interest in enabling artificial intelligence technologies, such as advanced machine learning, new threats, such as adversarial attacks, and certification challenges, due to the lack of sufficient explainability. However, in order to be trustworthy, those systems also need to be dependable, secure, and resilient according to well-established taxonomies, methodologies, and tools. Therefore, several aspects need to be addressed for TAS, ranging from proper taxonomic classification to the identification of research opportunities and challenges. Given such a context, in this paper address relevant taxonomies and research perspectives in the field of TAS. We start from basic definitions and move towards future perspectives, regulations, and emerging technologies supporting development and operation of TAS.

Journal of Computer Security, vol. 27, issue 5, Elsevier, pp. 521-546, 09/2019.
European Symposium on Research in Computer Security (ESORICS 2018), vol. 11098, Springer, pp. 555-574, 08/2018. DOI
Abstract
Advanced persistent threats pose a serious issue for modern industrial environments, due to their targeted and complex attack vectors that are difficult to detect. This is especially severe in critical infrastructures that are accelerating the integration of IT technologies. It is then essential to further develop effective monitoring and response systems that ensure the continuity of business to face the arising set of cyber-security threats. In this paper, we study the practical applicability of a novel technique based on opinion dynamics, that permits to trace the attack throughout all its stages along the network by correlating different anomalies measured over time, thereby taking the persistence of threats and the criticality of resources into consideration. The resulting information is of essential importance to monitor the overall health of the control system and correspondingly deploy accurate response procedures.

Computers & Security, vol. 55, no. November, Elsevier, pp. 235-250, 2015.
Abstract
The correct operation of Critical Infrastructures (CIs) is vital for the well being of society, however these complex systems are subject to multiple faults and threats every day. International organizations around the world are alerting the scientific community to the need for protection of CIs, especially through preparedness and prevention mechanisms. One of the main tools available in this area is the use of Intrusion Detection Systems (IDSs). However, in order to deploy this type of component within a CI, especially within its Control System (CS), it is necessary to verify whether the characteristics of a given IDS solution are compatible with the special requirements and constraints of a critical environment. In this paper, we carry out an extensive study to determine the requirements imposed by the CS on the IDS solutions using the Non-Functional Requirements (NFR) Framework. The outcome of this process are the abstract properties that the IDS needs to satisfy in order to be deployed within a CS, which are refined through the identification of satisficing techniques for the NFRs. To provide quantifiable measurable evidence on the suitability of the IDS component for a CI, we broaden our study using the Goal Question Metric (GQM) approach to select a representative set of metrics. A requirements model, refined with satisficing techniques and sets of metrics which help assess, in the most quantifiable way possible, the suitability and performance of a given IDS solution for a critical scenario, constitutes the results of our analysis.

8th International Conference on Critical Information Infrastructures Security, vol. 8328, Springer, pp. 197-203, 2013. DOI
Abstract
Critical Infrastructure Protection (CIP) faces increasing challenges in number and in sophistication, which makes vital to provide new forms of protection to face every day’s threats. In order to make such protection holistic, covering all the needs of the systems from the point of view of security, prevention aspects and situational awareness should be considered. Researchers and Institutions stress the need of providing intelligent and automatic solutions for protection, calling our attention to the need of providing Intrusion Detection Systems (IDS) with intelligent active reaction capabilities. In this paper, we support the need of automating the processes implicated in the IDS solutions of the critical infrastructures and theorize that the introduction of Machine Learning (ML) techniques in IDS will be helpful for implementing automatic adaptable solutions capable of adjusting to new situations and timely reacting in the face of threats and anomalies. To this end, we study the different levels of automation that the IDS can implement, and outline a methodology to endow critical scenarios with preventive automation. Finally, we analyze current solutions presented in the literature and contrast them against the proposed methodology

Wireless Personal Communications, vol. 73, Springer, pp. 23-50, Nov 2013, 2012. DOI
Abstract
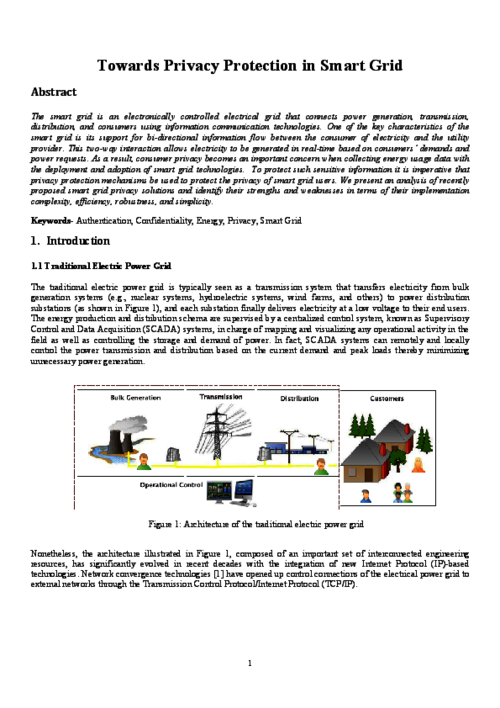
The smart grid is an electronically controlled electrical grid that connects power generation, transmission, distribution, and consumers using information communication technologies. One of the key characteristics of the smart grid is its support for bi-directional information flow between the consumer of electricity and the utility provider. This two-way interaction allows electricity to be generated in real-time based on consumers’ demands and power requests. As a result, consumer privacy becomes an important concern when collecting energy usage data with the deployment and adoption of smart grid technologies. To protect such sensitive information it is imperative that privacy protection mechanisms be used to protect the privacy of smart grid users. We present an analysis of recently proposed smart grid privacy solutions and identify their strengths and weaknesses in terms of their implementation complexity, efficiency, robustness, and simplicity.