IoTest
Digital Witnesses: trusted devices for Cybersecurity in IoT
- Spanish Ministry of Economy and Competitiveness, National Programme for Fostering Excellence in Scientific and Technical Research (TIN2015-72634-EXP /AEI).
- Duration: 14/06/2017 to 14/06/2019

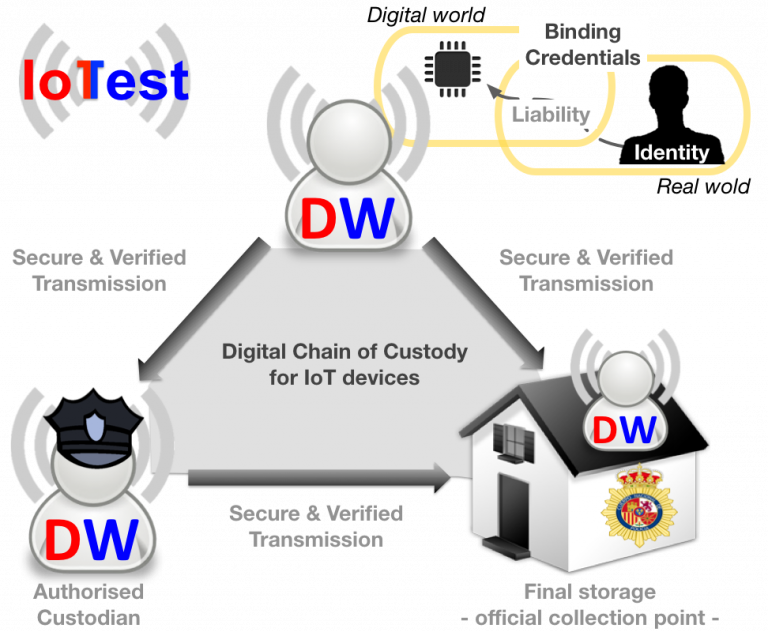
This project aims to help solve this problem by introducing a security solution that is radically different from those that have been used until now. In particular, this project proposes the design and development of Digital Witnesses, trusted electronic devices capable of obtaining electronic evidence and safeguarding it in a protected area. Using these devices as a foundation, the IoTest project aims to offer a dynamic solution that will record events on heterogeneous, unpredictable and uncertain scenarios.
Moreover, since existing digital evidence processes and regulations are not prepared to deal with the new cybersecurity issues created by these highly dynamic and distributed scenarios, the deployment of digital witnesses will result on a qualitative advancement in the evolution of electronic evidence management systems, improving their effectiveness in the detection of attacks and identification of cybercriminals. [1] [2][3][4][5][6] [7] [8] [9] [10]
References
- Ana Nieto and Antonio Acien and Javier Lopez (2018): Capture the RAT: Proximity-based Attacks in 5G using the Routine Activity Theory. In: The 16th IEEE International Conference on Dependable, Autonomic and Secure Computing (DASC 2018), pp. 520-527, IEEE IEEE, Athens, Greece, 2018, ISBN: 978-1-5386-7518-2.
- Ana Nieto and Ruben Rios and Javier Lopez (2017): A Methodology for Privacy-Aware IoT-Forensics. In: 16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom 2017), pp. 626-633, IEEE IEEE, Sydney (Australia), 2017, ISSN: 2324-9013.
- Ana Nieto and Ruben Rios and Javier Lopez (2017): Digital Witness and Privacy in IoT: Anonymous Witnessing Approach. In: 16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom 2017), pp. 642-649, IEEE IEEE, Sydney (Australia), 2017, ISSN: 2324-9013.
- Ana Nieto and Ruben Rios (2017): Requisitos y soluciones de privacidad para la testificación digital. In: III Jornadas Nacionales de Investigación en Ciberseguridad (JNIC 2017), pp. 51-58, Servicio de Publicaciones de la URJC Servicio de Publicaciones de la URJC, Madrid (Spain), 2017, ISBN: 978-84-608-4659-8.
- Ana Nieto and Ruben Rios and Javier Lopez (2017): PRoFIT: modelo forense-IoT con integración de requisitos de privacidad. In: XIII Jornadas de Ingeniería Telemática (JITEL 2017), pp. 302-309, Editorial Universitat Politècnica de València Editorial Universitat Politècnica de València, Valencia, 2017, ISBN: 978-84-9048-595-8.
- Ana Nieto and Rodrigo Roman and Javier Lopez (2016): Digital Witness: Safeguarding Digital Evidence by using Secure Architectures in Personal Devices. In: IEEE Network, pp. 12-19, 2016, ISSN: 0890-8044.
- Ana Nieto and Rodrigo Roman and Javier Lopez (2016): Testificación Digital. In: Revista SIC, vol. 122, pp. 94-98, 2016, ISSN: 1136-0623.
- Ana Nieto and Rodrigo Roman and Javier Lopez (2016): Digital Witness: Digital Evidence Management Framework for the Internet of Things. In: ERCIM News, no. 106, pp. 9-9, 2016, ISSN: 0926-4981.
- Ana Nieto and Rodrigo Roman and Javier Lopez (2016): Testigo digital: delegación vinculante de evidencias electrónicas para escenarios IoT. In: II Jornadas Nacionales de Investigación en Ciberseguridad (JNIC 2016), pp. 109-116, 2016, ISBN: 978-84-608-8070-7.
- Ana Nieto and Rodrigo Roman and Javier Lopez (2016): Arquitectura funcional para la cadena de custodia digital en objetos de la IoT. In: XIV Reunión Española sobre Criptología y Seguridad de la Información, pp. 168-173, 2016, ISBN: 978-84-608-9470-4.
Proyecto TIN2015-72634-EXP financiado por:


