The 16th IEEE International Conference on Dependable, Autonomic and Secure Computing (DASC 2018), pp. 536-543, 08/2018. DOI
Abstract
In the current telecommunications landscape, different devices, systems and platforms are constantly communicating with each other. This heterogeneous environment creates the perfect situation for attacks to pass from one platform to another. This is a particularly worrying scenario, because of the new technologies being used (such as network slicing in 5G), the increasing importance of connected devices in our lives (IoT), and the unpredictable consequences that an attack of this type could have. The current approaches in attack analysis do not take into account these sitations, and the attacker/victim paradigm usually followed may fall short when dealing with these attacks. Thus, in this paper, an architecture for the analysis of cross-platform attacks will be presented, aiming to help understand better this kind of threats and offering solutions to mitigate and track them.

The 16th IEEE International Conference on Dependable, Autonomic and Secure Computing (DASC 2018), IEEE, pp. 520-527, 08/2018. DOI
Abstract
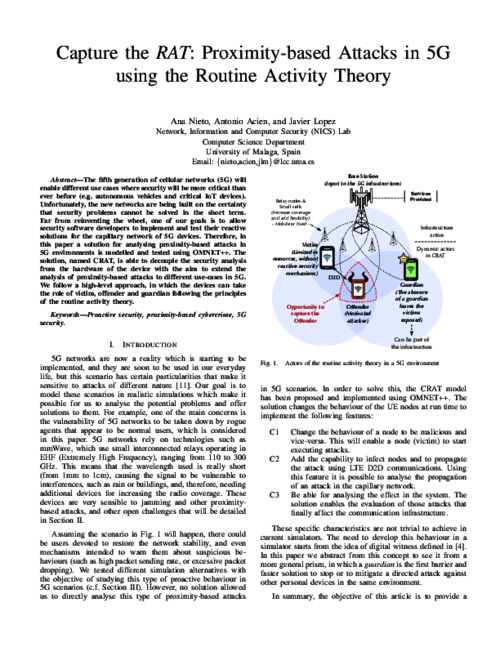
The fifth generation of cellular networks (5G) will enable different use cases where security will be more critical than ever before (e.g. autonomous vehicles and critical IoT devices). Unfortunately, the new networks are being built on the certainty that security problems can not be solved in the short term. Far from reinventing the wheel, one of our goals is to allow security software developers to implement and test their reactive solutions for the capillary network of 5G devices. Therefore, in this paper a solution for analysing proximity-based attacks in 5G environments is modelled and tested using OMNET++. The solution, named CRAT, is able to decouple the security analysis from the hardware of the device with the aim to extend the analysis of proximity-based attacks to different use-cases in 5G. We follow a high-level approach, in which the devices can take the role of victim, offender and guardian following the principles of the routine activity theory.
15th International Conference on Trust, Privacy and Security in Digital Business (TrustBus 2018), vol. LNCS 11033, Springer Nature Switzerland AG, pp. 229–243, 09/2018. DOI
Abstract
Recent news have raised concern regarding the security on the IoT field. Vulnerabilities in devices are arising and honeypots are an excellent way to cope with this problem. In this work, current solutions for honeypots in the IoT context, and other solutions adaptable to it are analyzed in order to set the basis for a methodology that allows deployment of IoT honeypot.

Mobile Networks and Applications (MONET), Springer US, pp. 881-889, 10/2018. DOI
Abstract
Crowdsourcing can be a powerful weapon against cyberattacks in 5G networks. In this paper we analyse this idea in detail, starting from the use cases in crowdsourcing focused on security, and highlighting those areas of a 5G ecosystem where crowdsourcing could be used to mitigate local and remote attacks, as well as to discourage criminal activities and cybercriminal behaviour. We pay particular attention to the capillary network, where an infinite number of IoT objects coexist. The analysis is made considering the different participants in a 5G IoT ecosystem.
XV Reunión Española sobre Criptología y Seguridad de la Información, 10/2018.
Abstract
Con la revolución tecnológica que ha supuesto la Internet de las Cosas (Internet of Things, IoT) se han presentado escenarios donde la preocupación por la seguridad en dicho entorno es cada vez más relevante. Están comenzando a surgir vulnerabilidades en varios dispositivos, y los sistemas trampa son una excelente manera de lidiar con este problema. En este trabajo se analizan soluciones para honeypots en el entorno IoT (y en otros que se puedan adaptar) para sentar las bases de una metodología que permita el despliegue de honeypots IoT.

IV Jornadas Nacionales de Investigación en Ciberseguridad (JNIC 2018), Servicio Editorial de Mondragon Unibertsitatea, 06/2018.
Abstract
Los ataques cross-platform suponen un serio desafío para los mecanismos de seguridad cuando los portadores de un ataque dirigido no son conscientes de su participacion en el mismo. Es por ello que, con dispositivos y tecnologías cada vez mas entrelazadas, en constante comunicación, numerosos ataques pasan desapercibidos hasta que alcanzan su objetivo final. Estos nuevos escenarios hacen posible una vía de transmision a tener en cuenta, y que se debe abordar cuanto antes, ya que sus consecuencias, especialmente en el panorama de telecomunicaciones actual, podrían ser desoladoras. La rapida transmisión de estos ataques, y la dificultad que supone su prevencion, detección y mitigación antes de que se hagan efectivos, hacen que el problema sea particularmente preocupante. En este artículo se presentará una arquitectura para el analisis de los ataques cross-platform silenciosos, cuyo objetivo es ayudar a comprender mejor este tipo de amenazas y ofrecer soluciones que permitan mitigarlas y rastrearlas.
 ]
]