 ] Type Year
] Type Year X Jornadas de Ingeniería Telemática (JITEL 2011), K. Hackbarth, R. Agüero, and R. Sanz Eds., Universidad de Cantabria, pp. 104 - 111, 09/2011.
Abstract
El paradigma de red personal (PN) permitirá la interacción y colaboración del creciente abanico de dispositivos personales. Con tal fin la PN ha de integrar en su seno múltiples tecnologías heterogéneas con diversas capacidades computacionales y de comunicación de forma segura. En particular, la incorporación de la tecnología RFID en objetos personales conlleva múltiples riesgos de seguridad y privacidad que han suscitado un elevado interés de la comunidad investigadora en los últimos años. Más allá de su seguridad de forma aislada, su integración en la PN y la interacción de ésta con redes de área extensa como Internet of Things requieren una arquitectura de red personal adecuada para tal contexto. Este artículo proporciona los fundamentos de tal arquitectura segura incluyendo el análisis de aspectos como la incorporación e inicialización de las restringidas etiquetas RFID en la red personal, la autenticación tanto de miembros de la PN como de usuarios y servicios remotos en su acceso a las tecnologías de contexto, el control de las políticas de privacidad y el establecimiento de canales seguros de comunicación supervisados.
XI Reunión Española sobre Criptología y Seguridad de la Información (RECSI 2010), pp. 337-342, September, 2010.
Abstract
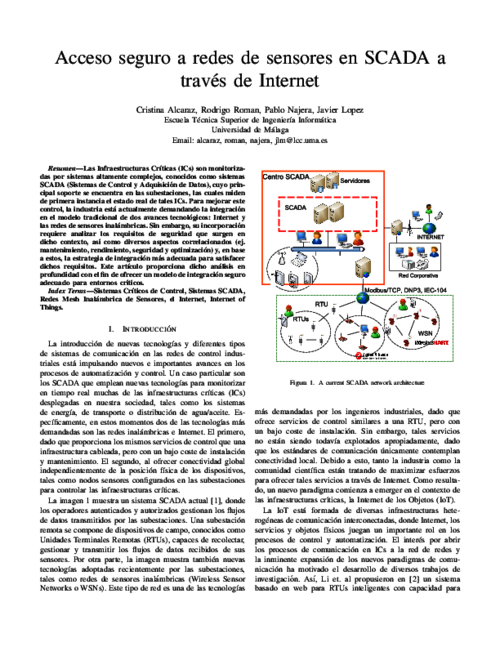
Las Infraestructuras Críticas (ICs) son monitorizadas por sistemas altamente complejos, conocidos como sistemas SCADA (Sistemas de Control y Adquisición de Datos), cuyo principal soporte se encuentra en las subestaciones, las cuales miden de primera instancia el estado real de tales ICs. Para mejorar este control, la industria está actualmente demandando la integración en el modelo tradicional de dos avances tecnológicos: Internet y las redes de sensores inalámbricas. Sin embargo, su incorporación requiere analizar los requisitos de seguridad que surgen en dicho contexto, así como diversos aspectos correlacionados (ej. mantenimiento, rendimiento, seguridad y optimización) y, en base a estos, la estrategia de integración más adecuada para satisfacer dichos requisitos. Este artículo proporciona dicho análisis en profundidad con el fin de ofrecer un modelo de integración seguro adecuado para entornos críticos.
Computer Networks, vol. 134, Elsevier, pp. 46 - 54, 2018. DOI
International Conference on Information and Communications Security (ICICS’02), LNCS 2513, Springer-Verlag, pp. 399-410, December, 2002.
Abstract
Distributed systems usually contain objects with heterogeneous security requirements that pose important challenges on the underlying security mechanisms and especially in access control systems. Access control in distributed systems often relies on centralized security administration. Existing solutions for distributed access control do not provide the flexibility and manageability required. This paper presents the XML-based Secure Content Distribution (XSCD) infrastructure is based on the production of self-protected software objects that convey contents (software or data) and can be distributed without further security measures because they embed the access control enforcement mechanism. It also provides means for integrating Privilege Management Infrastructures (PMIs). Semantic information is used in the dynamic instantiation and semantic validation of policies. XSCD is scalable, facilitates the administration of the access control system, guarantees the secure distribution of the contents, enables semantic integration and interoperability of heterogeneous sources, solves the “originator retained control” issue and allows activities (such as payment) to be bound to the access to objects.
6th International Conference on Trust, Privacy and Security in Digital Business (TrustBus’09), Springer-Verlag, pp. 86-94, September, 2009. DOI
Abstract
SCADA systems represent a challenging scenario where the management of critical alarms is crucial. Their response to these alarms should be efficient and fast in order to mitigate or contain undesired effects. This work presents a mechanism, the Adaptive Assignment Manager (AAM) that will aid to react to incidences in a more efficient way by dynamically assigning alarms to the most suitable human operator. The mechanism uses various inputs for identifying the operators such as their availability, workload and reputation. In fact, we also define a reputation component that stores the reputation of the human operators and uses feedback from past experiences.

9th IFIP International Conference on New Technologies, Mobility & Security, 2018.

6th International Conference on Network and System Security (NSS 2012), LNCS 7645 7645, Springer-Verlag, pp. 58-71, November 2012. DOI
Abstract
Control and situational awareness are two very important aspects within critical control systems, since potential faults or anomalous behaviors could lead to serious consequences by hiding the real status of supervised critical infrastructures. Examples of these infrastructures are energy generation, transmission or distribution systems that belong to Smart Grid systems. Given the importance of these systems for social welfare and its economy, a situational awareness-based model, composed of a set of current technologies, is proposed in this paper. The model focuses on addressing and offering a set of minimum services for protection, such as prevention, detection, response, self-evaluation and maintenance, thereby providing a desirable protection in unplanned situations.
XII Reunión Española sobre Criptología y Seguridad de la Información (RECSI 2012), U.. Zurutuza, R.. Uribeetxeberria, and I.. Arenaza-Nuño Eds., pp. 309-314, Sep 2012.
Abstract
Los patrones de tráfico característicos de las redes inalámbricas de sensores (WSNs) dan lugar al problema de la privacidad de localización. De manera similar, el tráfico de los usuarios en Internet revela información sensible que puede ser protegida mediante sistemas de comunicación anónima (ACS). Por ello, este trabajo analiza la posibilidad de adaptar las soluciones de anonimato tradicionales al problema particular de las redes de sensores. Hasta el momento estas soluciones habían sido rechazadas sin un análisis riguroso, argumentando simplemente que eran demasiado exigentes computacionalmente para los nodos sensores. Nuestros resultados demuestran que, en general, algunos ACS no cumplen los requisitos de privacidad necesarios en WSNs mientras que otros, que si los cumplen, se valen de una cantidad de recursos que superan la capacidad de los sensores.
Information Systems Frontiers, vol. 14, Springer, pp. 527-540, July 2012. DOI
Abstract
Our society is becoming increasingly more IT-oriented, and the images and sounds that reflect our daily life are being stored mainly in a digital form. This digital personal life can be part of the home multimedia contents, and users demand access and possibly share these contents (such as photographs, videos, and music) in an ubiquitous way: from any location and with any device. The purpose of this article is twofold. First, we introduce the Feel@Home system, whose main objective is to enable the previously mentioned vision of an ubiquitous digital personal life. Second, we describe the security architecture of Feel@Home, analyzing the security and privacy requirements that identify which threats and vulnerabilities must be considered, and deriving the security building blocks that can be used to protect both IMS-based and VPN-based solutions.
|
"Advances in Critical Infrastructure Protection: Information Infrastructure Models, Analysis, and Defense", LNCS, vol. 6715, Springer, 2012.  |  |
Electronic Commerce Research and Applications, vol. 3, no. 2, Elsevier, pp. 152-162, 2004.
Abstract
Non-repudiation is a security service that provides cryptographic evidence to support the settlement of disputes in electronic commerce. In commercial transactions, an intermediary (or agent) might be involved to help transacting parties to conduct their business. Nevertheless, such an intermediary may not be fully trusted. In this paper, we propose agent-mediated non-repudiation protocols and analyze their security requirements. We first present a simple scenario with only one recipient, followed by a more complicated framework where multiple recipients are involved and collusion between them is possible. We also identify applications that could take advantage of these agent-mediated non-repudiation protocols.
VI Jornadas de Ingeniería Telemática (JITEL’08), pp. 437, September, 2008.
Abstract
Las infraestructuras críticas, como el sector energético, la banca, el transporte, y muchas otras, son un pilar esencial para en bienestar de la sociedad y la economía de un país. Estas infraestructuras dependen a su vez de ciertas infraestructuras de información, las cuales permiten su correcto funcionamiento. La tarea de proteger esas infraestructuras (de información) críticas es compleja y multidimensional, con una gran cantidad de desafíos por resolver. Precisamente, las redes de sensores pueden ser de gran ayuda para esta tarea, debido a suscapacidades de control distribuidas y a su habilidad de funcionar en situaciones extremas. Este artículo analiza la utilidad de las redes de sensores en este contexto, describiendo tanto sus capacidades como sus posibles roles y mecanismos de integración para la protección de infraestructuras (de información) críticas.
VI Jornadas de Ingeniería Telemática (JITEL’07), pp. 401-408, September, 2007.
Abstract
Security in wireless sensor networks is very limited due to highly-constrained hardware of sensor nodes. To protect services is necessary to use secure foundations, known as security primitives, like part of a protocol. Theses primitives must assure at least confidentiality in the communication channel, authentication of the peers involved in an information exchange, and integrity of the messages. There are many primitives such as symmetric encryption, hash functions and public key cryptography, but not all of them can be supported by sensor nodes since require high resource levels, for example memory. This paper contains a deep analysis of available and suitable security primitives for sensor nodes, as well as an analysis of hardware and software implementations. Besides, it has been developed an experiment with two implementations, and it has been created a new and improved version using the optimizations of each.

V Jornadas de Ingenería Telemática (JITEL’05), pp. 335-343, Septiembre, 2005.
Abstract
The design and development of security infrastructures and protocols for Wireless Sensor Networks is a difficult task, due to several factors like the constraints of the sensor nodes and the public nature of the communication channels. The intrinsic features of these networks create numerous security problems. In this paper, we analyze and put into perspective those problems.

I Simposio Español de Comercio Electrónico (SEC’01), pp. 145-160, Octubre, 2001.
Abstract
La presente ponencia aborda el desarrollo de un entorno seguro escalable para el Comercio Electrónico. Se ha tratado la cuestión en dos fases: primero, idear un prototipo generalizado distribuido seguro formado por diferentes entidades genéricas con el objetivo de permitir que los clientes realicen sus compras y transacciones bancarias con un nivel de seguridad escalable; y en segundo lugar, implantar en la práctica un prototipo de grado de escalabilidad reducido como modelo empírico.
Security and Communication Networks (SCN) Journal, vol. 7, issue 12, Wiley-Blackwell, pp. 2778-2803, 2013. DOI
Abstract
Motivated by the growing convergence of diverse types of networks and the rise of concepts such as Future Internet (FI), in this paper we analyse the coexistence of security mechanisms and Quality of Service (QoS) mechanisms in resourceconstrained networks, that are relevant types of networks within the FI environment. More precisely, we analyse the current state of the research on security and QoS in the integration of Wireless Sensor Networks (WSNs), Mobile Ad-Hoc Networks (MANETs) and cellular networks. Furthermore, we propose a taxonomy to identify similarities among these technologies, as well as the requirements for network interconnection. As a result, we define a dependency-based model for the analysis of Security and QoS tradeoff, and also define a high-level integration architecture for networks in the FI setting. The final goal is to provide a critical point of view that allows to assess whether such an integration of networks can be both secure and efficient.
6th Conference on E-Commerce (CEC’04), IEEE Computer Society, pp. 221-226, June, 2004.
Abstract
Mobile agents play an important role in electronic commerce. Security in free-roaming agents is especially hard to achieve when the mobile code is executed in hosts that may behave maliciously. Some schemes have been proposed to protect agent data (or computation results). However, a known vulnerability of these techniques is the truncation attack where two visited hosts (or one revisited host) can collude to discard the partial results collected between their respective visits. Cheng and Wei proposed a scheme in ICICS’02 to defense against the truncation of computation results of free-roaming agents. Cheng-Wei scheme is effective against such an attack in most cases. However, we demonstrate that it still suffers from the truncation attack when a special loop is established on the path of a free-roaming agent. We further propose two amendments to Cheng-Wei scheme to avoid such an attack.

The 12th International Conference on Critical Information Infrastructures Security, vol. Lecture Notes in Computer Science, vol 10707, Springer, pp. 119-130, 08/2018.

International Journal of Information Security, vol. 2, no. 1, Springer, pp. 21-36, 2003.
Abstract
We present the adaptation of our model for the validation of key distribution and authentication protocols to address some of the specific needs of protocols for electronic commerce. The two models defer in both the threat scenario and in the protocol formalization. We demonstrate the suitability of our adaptation by analyzing a specific version of the Internet Billing Server protocol introduced by Carnegie MellonUniversity. Our analysis shows that, while the security properties a key distribution or authentication protocol shall provide are well understood, it is often not clear which properties an electronic commerce protocol can or shall provide. We use the automatic theorem proving software ‘‘Otter’’ developed at Argonne National Laboratories for state space exploration.
14th International Conference on Security and Cryptography (SECRYPT 2017), vol. 6, SciTePress, pp. 116-128, 2017. DOI

IET Communications, vol. 5, Institution of Engineering and Technology, pp. 2518 - 2532, Nov 2011. DOI
Abstract
Extensive work has been done on the protection of Wireless Sensor Networks (WSNs) from the hardware to the application layer. However, only recently, the privacy preservation problem has drawn the attention of the research community because of its challenging nature. This problem is exacerbated in the domain of WSNs due to the extreme resource limitation of sensor nodes. In this paper we focus on the location privacy problem in WSNs, which allows an adversary to determine the location of nodes of interest to him. We provide a taxonomy of solutions based on the power of the adversary and the main techniques proposed by the various solutions. In addition, we describe and analyse the advantages and disadvantages of different approaches. Finally, we discuss some open challenges and future directions of research.

International Journal of Critical Infrastructure Protection (IJCIP), vol. 5, Elsevier, pp. 137–145, 2012. DOI
Abstract
The use of modern information and communications technologies in supervisory control and data acquisition (SCADA) systems used in the critical infrastructure has become an important topic of research. The modernization significantly enhances operational performance, but also introduces security issues and the associated risks. This paper formally analyzes how the introduction of new technologies can impact control systems and ultimately affect the performance of the critical infrastructure systems being controlled. Five control system requirements are identified with the goal of proposing new operational requirements that trade-off performance and security.

XVI Jornadas de Ingeniería del Software y Bases de Datos (JISBD 2011), Servizo de publicacións da Universidade da Coruña, pp. 487-491, 2011.
Abstract
Developing software through systematic processes is becoming more and more important due to the growing complexity of software development. It is important that the development process used integrates security aspects from the first stages at the same level as other functional and non-functional requirements. The identification of security aspects in the first stages ensures a more robust development and permits the security requirements to be perfectly coupled with the design and the rest of the system’s requirements. Systems which are based on Grid Computing are a kind of systems that have clear differentiating features in which security is a highly important aspect. Generic development processes are sometimes used to develop Grid specific systems without taking into consideration either the subjacent technological environment or the special features and particularities of these specific systems. In fact, the majority of existing Grid applications have been built without a systematic development process and are based on ad hoc developments.

Information and Software Technology, vol. 52, Elsevier, pp. 517-536, May 2010. DOI
Abstract
Developing software through systematic processes is becoming more and more important due to the growing complexity of software development. It is important that the development process used integrates security aspects from the first stages at the same level as other functional and non-functional requirements. Systems which are based on Grid Computing are a kind of systems that have clear differentiating features in which security is a highly important aspect. The Mobile Grid, which is relevant to both Grid and Mobile Computing, is a full inheritor of the Grid with the additional feature that it supports mobile users and resources. A development methodology for Secure Mobile Grid Systems is proposed in which the security aspects are considered from the first stages of the life-cycle and in which the mobile Grid technological environment is always present in each activity. This paper presents the analysis activity, in which the requirements (focusing on the grid, mobile and security requirements) of the system are specified and which is driven by reusable use cases through which the requirements and needs of these systems can be defined. These use cases have been defined through a UML-extension for security use cases and Grid use cases which capture the behaviour of this kind of systems. The analysis activity has been applied to a real case.
Foundations of Security Analysis and Design 2009, LNCS 5705, Springer Berlin/Heidelberg, pp. 289-338, August, 2009. DOI
Abstract
As sensor networks are more and more being implemented in real world settings, it is necessary to analyze how the different requirements of these real-world applications can influence the security mechanisms. This paper offers both an overview and an analysis of the relationship between the different security threats, requirements, applications, and security technologies. Besides, it also overviews some of the existing sensor network standards, analyzing their security mechanisms.

The 20th World Conference on Information Security Applications: WISA-Workshop 2019, Springer, 2019.
Abstract
In recent times, smart home devices like Amazon Echo and Google Home have reached mainstream popularity. These devices are intrinsically intrusive, being able to access user’s personal information. There are growing concerns about indiscriminate data collection and invasion of user privacy in smart home devices. Improper trust assumptions and security controls can lead to unauthorized access of the devices, which can have severe consequences (i.e. safety risks). In this paper, we analysed the behaviour of smart home devices with respect to trust relationships. We set up a smart home environment to evaluate how trust is built and managed. Then, we performed a number of interaction tests with different types of users (i.e. owner, guests). As a result, we were able to assess the effectiveness of the provided security controls and identify some relevant security issues. To address them, we defined a trust model and proposed a solution based on it for securing smart home devices.

The 16th IEEE International Conference on Dependable, Autonomic and Secure Computing (DASC 2018), pp. 536-543, 08/2018. DOI
Abstract
In the current telecommunications landscape, different devices, systems and platforms are constantly communicating with each other. This heterogeneous environment creates the perfect situation for attacks to pass from one platform to another. This is a particularly worrying scenario, because of the new technologies being used (such as network slicing in 5G), the increasing importance of connected devices in our lives (IoT), and the unpredictable consequences that an attack of this type could have. The current approaches in attack analysis do not take into account these sitations, and the attacker/victim paradigm usually followed may fall short when dealing with these attacks. Thus, in this paper, an architecture for the analysis of cross-platform attacks will be presented, aiming to help understand better this kind of threats and offering solutions to mitigate and track them.

Sixth International Workshop on Cryptology and Network Security (CANS’07), LNCS 4856, Springer, pp. 265-281, December, 2007.
Abstract
We present a semantic extension to X.509 certificates that allows incorporating new anonymity signature schemes into the X.509 framework. This fact entails advantages to both components. On the one hand, anonymous signature schemes benefit from all the protocols and infrastructure that the X.509 framework provides. On the other hand, the X.509 framework incorporates anonymity as a very interesting new feature. This semantic extension is part of a system that provides user’s controlled anonymous authorization under the X.509 framework. Additionally, the proposal directly fits themuch active Identity 2.0 effort,where anonymity is a major supplementary feature that increases the self-control of one’s identity and privacy which is at the center of the activity.
Computer Standards & Interfaces, vol. 30, no. 4, Elsevier, pp. 253-261, 2008.
Abstract
Anonymity has been formalized and some metrics have been defined in the scope of anonymizing communication channels. In this paper, such formalization has been extended to cope with anonymity in those scenarios where users must anonymously prove that they own certain privileges to perform remote transactions. In these types of scenarios, the authorization policy states the privileges required to perform a given remote transaction. The paper presents a framework to analyze the actual degree of anonymity reached in a given transaction and allows its comparison with an ideal anonymity degree as defined by the authorization policy, providinga tool to model, design and analyze anonymous systems in different scenarios.

Internet Research, vol. 16, no. 2, Elsevier, pp. 120-139, 2006.
Abstract
In Benjumea et. al (Benjumea, 2004) we introduced the concept of anonymousattribute certificates in order to integrate anonymity capabilities in the standardizedX.509 attribute certificates. That solution was based on the use of fair-blind signatures(Stadler, 1995), but did not explore further possibilities of constructing similar datastructures based on more advanced signature schemes. In this new work, we propose anew type of anonymous attribute certificates that is based on the more recently proposedtraceable signature scheme (Kiayias, 2004a), providing a new anonymous authorizationsolution with interesting features that were not covered in the aforementioned scheme.Thus, this new solution allows users to make use of their attribute certificates in ananonymous way, but under certain circumstances it allows to disclose the users’ identities,trace the transactions carried out by any specific user, or revoke any anonymousattribute certificate. An additional contribution of this work is that it pays special attentionto the preservation of the unlinkability property between transactions, makingimpossible the creation of anonymous user profiles.
Computer Communications, vol. 29, no. 15, Elsevier, pp. 2739-2749, 2006. DOI
Abstract
Unsolicited Commercial Email, or Spam, is nowadays an increasingly serious problem to email users. A number of anti-spam schemes have been proposed in the literature and some of them have been deployed in email systems, but the problem has yet been well addressed. One of those schemes is challenge-response, in which a challenge, ranging from a simple mathematical problem to a hard-AI problem, is imposed on an email sender in order to forbid machine-based spam reaching receivers’ mailboxes. However, such a scheme introduces new problems for the users, e.g., delay of service and denial of service. In this paper, we introduce the pre-challenge scheme, which is based on the challenge-response mechanism and takes advantage of some features of email systems. It assumes each user has a challenge that is defined by the user himself/herself and associated with his/her email address, in such a way that an email sender can simultaneously retrieve a new receiver’s email address and challenge before sending an email in the first contact. Some new mechanisms are employed in our scheme to reach a good balance between security against spam and convenience to normal email users. Our scheme can be also used for protecting other messaging systems, like Instant Messaging and Blog comments.

2nd International Workshop of Ubiquitous Computing & Ambient Intelligence (wUCAmI’06), University of Castilla La Mancha, pp. 83-95, November, 2006.
Abstract
La tecnología RFID, que permite la identificación única de cualquier ser u objeto sin necesidad de contacto ni línea de visión directa, se está adoptando ampliamente en todo tipo de campos al producir un salto cualitativo en la integración de la informática con el entorno. En este artículo se muestra su estado del arte y se afrontan dos soluciones orientadas a paliar las necesidades en entornos sanitarios. Por un lado, un sistema de seguimiento de dispositivos en el interior de un centro médico que permite su localización inmediata y la prevención de hurtos usando RFID pasivo UHF con un testeo de fiabilidad, y por otro, una solución de control y atención de pacientes ingresados en planta usando RFID pasivo HF obteniéndose un demostrador plenamente funcional
Simposio sobre Computación Ubicua e Inteligencia Ambiental (UCAmI’05), pp. 113-120, September, 2005.
Abstract
Los sistemas de detección de intrusiones (IDS) son una herramienta imprescindible de seguridad a la hora de proteger una red. Recientemente se han investigado y desarrollado arquitecturas de IDS para redes inalámbricas, en concreto para redes "Ad Hoc". No obstante, no existe un trabajo previo que desarrolle una arquitectura de IDS para una red de sensores. En este artículo, analizamos porque los sistemas IDS de redes "Ad Hoc" no pueden aplicarse a redes de sensores, e introducimos una arquitectura de IDS para redes de sensores que incorpora una nueva técnica para vigilar las comunicaciones de la red en ciertos escenarios.

Security and Communication Networks, vol. 9, issue 12, Wiley, pp. 1769-1785, 08/2016. DOI
Abstract
Several generic methods exist for achieving chosen-ciphertext attack (CCA)-secure public-key encryption schemes from weakly secure cryptosystems, such as the Fujisaki–Okamoto and REACT transformations. In the context of proxy re-encryption (PRE), it would be desirable to count on analogous constructions that allow PRE schemes to achieve better security notions. In this paper, we study the adaptation of these transformations to proxy re-encryption and find both negative and positive results. On the one hand, we show why it is not possible to directly integrate these transformations with weakly secure PRE schemes because of general obstacles coming from both the constructions themselves and the security models, and we identify 12 PRE schemes that exhibit these problems. On the other hand, we propose an extension of the Fujisaki–Okamoto transformation for PRE, which achieves a weak form of CCA security in the random oracle model, and we describe the sufficient conditions for applying it
5th International Workshop on Foundations and Practices of UML, LNCS 5833, Springer Berlin Heidelberg, pp. 126-136, 2009.
Abstract
Systems based on Grid computing have not traditionally beendeveloped through suitable methodologies and have not taken into accountsecurity requirements throughout their development, offering technical securitysolutions only during the implementation stages. We are creating a developmentmethodology for the construction of information systems based on GridComputing, which is highly dependent on mobile devices, in which securityplays a highly important role. One of the activities in this methodology is therequirements analysis which is use-case driven. In this paper, we build use casediagrams for a real mobile Grid application by using a UML-extension, calledGridUCSec-Profile, through which it is possible to represent specific mobileGrid features and security aspects for use case diagrams, thus obtainingdiagrams for secure mobile Grid environments.

IEEE Consumer Communications & Networking Conference (CCNC 2006), IEEE, pp. 640-644, January, 2006. DOI
Abstract
The research of Intrusion Detection Systems (IDS) is a mature area in wired networks, and has also attracted many attentions in wireless ad hoc networks recently. Nevertheless, there is no previous work reported in the literature about IDS architectures in wireless sensor networks. In this paper, we discuss the general guidelines for applying IDS to static sensor networks, and introduce a novel technique to optimally watch over the communications of the sensors’ neighborhood on certain scenarios.
11th International SDL Forum (SDL’03), LNCS 2708, Springer-Verlag, pp. 300-317, July, 2003.
Abstract
Nowadays, it is widely accepted that critical systems have to be formally analysed in order to achieve well-known formal method benefits. In order to study the security of communication systems, we have developed a methodology for the application of the formal analysis techniques commonly used in communication protocols to the analysis of cryptographic ones. In particular, we have extended the design and analysis phases with security properties. Our proposal uses a specification notation based on MSC, which can be automatically translated into a generic SDL specification. This SDL system can then be used for the analysis of the desired security properties, by using an observer process schema. Apart from our main goal of providing a notation for describing the formal specification of security systems, our proposal also brings additional benefits, such as the study of the possible attacks to the system, and the possibility of re-using the specifications produced to describe and analyse more complex systems.

IEEE International Workshop on Web Semantics (WebS’03), IEEE Press, pp. 622-626, 2003.
II Jornadas de Ingeniería Telemática (JITEL´99), pp. 141-148, Sep 1999.
XIV Reunión Española sobre Criptología y Seguridad de la Información, pp. 168-173, 10/2016.
Abstract
En la Internet de los Objetos (IoT, por sus siglas en inglés), los ataques pueden ser perpetrados desde dispositivos que enmascaran su rastro ayudándose de la densidad de objetos y usuarios. Actualmente la idea de que los dispositivos de usuario almacenan evidencias que pueden ser muy valiosas para frenar ataques es bien conocida. Sin embargo, la colaboración de éstos para denunciar posibles abusos telemáticos aún está por definir. Los testigos digitales son dispositivos concebidos para definir la participación de dispositivos de usuario en una cadena de custodia digital. La idea es que las evidencias se generan, almacenan y transfieren siguiendo los requisitos marcados por las normas actuales (p.ej. UNE 71505), pero respetando las restricciones en recursos de los dispositivos. En este artículo proponemos una arquitectura funcional para la implementación del concepto de testigo digital en dispositivos heterogéneos de la IoT.

Simposio Español de Informática Distribuida (SEID’00), pp. 313-320, Septiembre, 2000.
Abstract
La seguridad es uno de los aspectos más conflictivos del uso de Internet. La falta de una política de seguridad global está frenando el desarrollo de Internet en áreas tan interesantes y prometedoras como el comercio electrónico o la interacción con las administraciones públicas. Las técnicas criptográficas actuales proporcionan un alto grado de confidencialidad; no obstante, es difícil garantizar la identificación segura de los usuarios y, además, la gestión de las claves de los mismos es poco eficiente y presenta graves problemas de escalabilidad. Este trabajo describe las características de implementación de una solución a ambos problemas basada en una Infraestructura de Clave Pública (PKI) que proporciona una administración simple y eficiente de las claves de los usuarios y posibilita la autenticación segura de los mismos.

23rd International Information Security Conference (SEC 2008), vol. 278, pp. 125-139, 2008.
Proceedings of 6th International Conference on Cryptology in India, LNCS 3797, Springer, pp. 311–321, Decemeber, 2005.
Abstract
Contract signing is a fundamental service in doing business. The Internet has facilitated the electronic commerce, and it is necessary to find appropriate mechanisms for contract signing in the digital world. From a designing point of view, digital contract signing is a particular form of electronic fair exchange. Protocols for generic exchange of digital signatures exist. There are also specific protocols for two-party contract signing. Nevertheless, in some applications, a contract may need to be signed by multiple parties. Less research has been done on multi-party contract signing. In this paper, we analyze an optimistic N-party contract signing protocol, and point out its security problem, thus demonstrating further work needs to be done on the design and analysis of secure and optimistic multi-party contract signing protocols.

3rd international conference on Mobile multimedia communications (MobiMedia ’07), ICST, pp. 43:1–43:6, 2007.
Abstract
When delegation is implemented using the attribute certificates in a Privilege Management Infrastructure (PMI), this one reaches a considerable level of distributed functionality. However, the approach is not flexible enough for the requirements of ubiquitous environments. Additionally, the PMI can become a too complex solution for devices such as smartphones and PDAs, where resources are limited. In this work, we solve the previous limitations by defining a second class of attributes, called domain attributes, which are managed directly by users and are not right under the scope of the PMI, thus providing a light solution for constrained devices. The two classes of attributes are related by defining a simple ontology. We also introduce in the paper the concept of Attribute Federation which is responsible for supporting domain attributes and the corresponding ontology.

10th IFIP TC-6 TC-11 International Conference on Communications and Multimedia on Security (CMS’06), LNCS 4237, Springer, pp. 54-66, October, 2006. DOI
Abstract
This paper presents a model for delegation based on partial orders, proposing the subclass relation in OWL as a way to represent the partial orders. Delegation and authorization decisions are made based on the context. In order to interact with the context, we define the Type of a credential as a way to introduce extra information regarding context constraints. When reasoning about delegation and authorization relationships, our model benefits from partial orders, defining them over entities, attributes and the credential type. Using these partial orders, the number of credentials required is reduced. It also classifies the possible criteria for making authorization decisions based on the context, in relation to the necessary information.

Computers & Security, vol. 23, no. 7, Elsevier, pp. 578-590, 2004.
Abstract
In this article, we argue that traditional approaches for authorization and access control in computer systems (i.e., discretionary, mandatory, and role-based access controls) are not appropriate to address the requirements of networked or distributed systems, and that proper authorization and access control requires infrastructural support in one way or another. This support can be provided, for example, by an authentication and authorization infrastructure (AAI). Against this background, we overview, analyze, discuss, and put into perspective some technologies that can be used to build and operate AAIs. More specifically, we address Microsoft .NET Passport and some related activities (e.g. the Liberty Alliance Project), Kerberos-based solutions, and AAIs that are based on digital certificates and public key infrastructures (PKIs). We conclude with the observation that there is no single best approach for providing an AAI, that every approach has specific advantages and disadvantages, and that a comprehensive AAI must combine various technologies and approaches.

Sensors, vol. 10, pp. 3718-3731, 2010.
International Conference on Imaging Science, Systems, and Technology (CISST’98), July, 1998.
International Conference on Imaging Science, Systems, and Technology (CISST’98), July, 1998.
Computers and Electrical Engineering, vol. 47, issue October, Elsevier, pp. 299-317, 2015. DOI
Abstract
Current Critical Infrastructures (CIs) need intelligent automatic active reaction mechanisms to protect their critical processes against cyber attacks or system anomalies, and avoid the disruptive consequences of cascading failures between interdependent and interconnected systems. In this paper we study the Intrusion Detection, Prevention and Response Systems (IDPRS) that can offer this type of protection mechanisms, their constituting elements and their applicability to critical contexts. We design a methodological framework determining the essential elements present in the IDPRS, while evaluating each of their sub-components in terms of adequacy for critical contexts. We review the different types of active and passive countermeasures available, categorizing them and assessing whether or not they are suitable for Critical Infrastructure Protection (CIP). Through our study we look at different reaction systems and learn from them how to better create IDPRS solutions for CIP.

