IEEE International Conference on Metaverse Computing, Networking and Applications, 06/2023.
Abstract
In the last few years we have seen many different approaches to incorporate privacy features to blockchains. In the area of cryptocurrencies that would normally mean protecting the identity of the owner of some funds, but there are other applications where privacy is even more important, especially in permissioned blockchains.
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu's design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.

Computer Science Review, vol. 49, no. 100567, Elsevier, 05/2023. DOI
Abstract
Secure Multi-party Computation (SMPC) is a family of protocols which allow some parties to compute a function on their private inputs, obtaining the output at the end and nothing more. In this work, we focus on a particular SMPC problem named Private Set Intersection (PSI). The challenge in PSI is how two or more parties can compute the intersection of their private input sets, while the elements that are not in the intersection remain private. This problem has attracted the attention of many researchers because of its wide variety of applications, contributing to the proliferation of many different approaches. Despite that, current PSI protocols still require heavy cryptographic assumptions that may be unrealistic in some scenarios. In this paper, we perform a Systematic Literature Review of PSI solutions, with the objective of analyzing the main scenarios where PSI has been studied and giving the reader a general taxonomy of the problem together with a general understanding of the most common tools used to solve it. We also analyze the performance using different metrics, trying to determine if PSI is mature enough to be used in realistic scenarios, identifying the pros and cons of each protocol and the remaining open problems.

19th International Conference on Security and Cryptography (SECRYPT 2022), Scitepress, pp. 249-260, 07/2022. DOI
Abstract
Crowd Counting is a very interesting problem aiming at counting people typically based on density averages and/or aerial images. This is very useful to prevent crowd crushes, especially on urban environments with high crowd density, or to count people in public demonstrations. In addition, in the last years, it has become of paramount importance for pandemic management. For those reasons, giving users automatic mechanisms to anticipate high risk situations is essential. In this work, we analyze ID-based Crowd Counting, and propose a real-time Crowd Counting system based on the Ephemeral ID broadcast by contact tracing applications on wearable devices. We also performed some simulations that show the accuracy of our system in different situations.

International Journal of Information Security, Springer, 2020. DOI
Abstract
Nowadays, smart home devices like Amazon Echo and Google Home have reached mainstream popularity.
Being in the homes of users, these devices are intrinsically intrusive, being able to access details such as users' name, gender, home address, calendar appointments and others.
There are growing concerns about indiscriminate data collection and invasion of user privacy in smart home devices, but studies show that perceived benefits are exceeding perceived risks when it comes to consumers.
As a result, consumers are placing a lot of trust in these devices, sometimes without realizing it.
Improper trust assumptions and security controls can lead to unauthorized access and control of the devices, which can result in serious consequences.
In this paper, we explore the behaviour of devices such as Amazon Echo and Google Home in a smart home setting with respect to trust relationships and propose a trust model to improve these relationships among all the involved actors.
We have evaluated how trust was built and managed from the initial set up phase to the normal operation phase, during which we performed a number of interaction tests with different types of users (i.e. owner, guests).
As a result, we were able to assess the effectiveness of the provided security controls and identify potential relevant security issues. In order to address the identified issues, we defined a trust model and propose a solution based on it for further securing smart home systems.

IEEE Internet of Things Journal, vol. 6, issue 5, IEEE Computer Society, pp. 8038-8045, 10/2019. DOI
Abstract
Edge Computing paradigms are expected to solve some major problems affecting current application scenarios that rely on Cloud computing resources to operate. These novel paradigms will bring computational resources closer to the users and by doing so they will not only reduce network latency and bandwidth utilization but will also introduce some attractive context-awareness features to these systems. In this paper we show how the enticing features introduced by Edge Computing paradigms can be exploited to improve security and privacy in the critical scenario of vehicular networks (VN), especially existing authentication and revocation issues. In particular, we analyze the security challenges in VN and describe three deployment models for vehicular edge computing, which refrain from using vehicular- to-vehicular communications. The result is that the burden imposed to vehicles is considerably reduced without sacrificing the security or functional features expected in vehicular scenarios.

XIV Jornadas de Ingeniería Telemática, pp. 50-53, 10/2019. DOI
Abstract
Este trabajo pretende analizar el paradigma de la Computación Segura Multiparte y sus posibles aplicaciones en el campo de la criptografía. Se plantea como modelo alternativo, mas escalable y seguro al uso de módulos hardware de seguridad para aplicaciones que requieran de Terceras Partes Confiables. Concretamente, se ha integrado un protocolo de criptografía RSA multiparte con la librería certbuilder, para la creación de certificados X.509. De esta forma se asegura que la creación de los certificados raíz de la Infraestructura de Clave Publica se realiza de forma que la generación de claves y firma de este se ejecute íntegramente sobre el sistema multiparte, con un modelo de tres partes que trabaja con circuitos aritméticos, sin que ninguna de ellas, de forma aislada, tenga posibilidad de comprometer la clave privada correspondiente. Para comprobar la viabilidad del sistema se han realizado pruebas de generación de certificados con diferentes longitudes de clave, siendo el proceso determinante la creación de las claves. Los elevados tiempos hacen que una aplicación como esta no sea asumible en otros escenarios, pero creemos que para el caso de la creación de los certificados raíz de una infraestructura de clave pública las garantías avanzadas de seguridad compensan el tiempo extra.
Sensors, vol. 18, issue 2, no. 492, MDPI, 02/2018. DOI
Abstract
IoT-Forensics is a novel paradigm for the acquisition of electronic evidence whose operation is conditioned by the peculiarities of the Internet of Things (IoT) context. As a branch of computer forensics, this discipline respects the most basic forensic principles of preservation, traceability, documentation, and authorization. The digital witness approach also promotes such principles in the context of the IoT while allowing personal devices to cooperate in digital investigations by voluntarily providing electronic evidence to the authorities. However, this solution is highly dependent on the willingness of citizens to collaborate and they may be reluctant to do so if the sensitive information within their personal devices is not sufficiently protected when shared with the investigators. In this paper, we provide the digital witness approach with a methodology that enables citizens to share their data with some privacy guarantees. We apply the PRoFIT methodology, originally defined for IoT-Forensics environments, to the digital witness approach in order to unleash its full potential. Finally, we show the feasibility of a PRoFIT-compliant digital witness with two use cases.

Future Generation Computer Systems, vol. 78, issue 1, Elsevier, pp. 680-698, 01/2018. DOI
Abstract
For various reasons, the cloud computing paradigm is unable to meet certain requirements (e.g. low latency and jitter, context awareness, mobility support) that are crucial for several applications (e.g. vehicular networks, augmented reality). To fulfil these requirements, various paradigms, such as fog computing, mobile edge computing, and mobile cloud computing, have emerged in recent years. While these edge paradigms share several features, most of the existing research is compartmentalised; no synergies have been explored. This is especially true in the field of security, where most analyses focus only on one edge paradigm, while ignoring the others. The main goal of this study is to holistically analyse the security threats, challenges, and mechanisms inherent in all edge paradigms, while highlighting potential synergies and venues of collaboration. In our results, we will show that all edge paradigms should consider the advances in other paradigms.

Computers & Security, vol. 77 , issue August 2018, Elsevier, pp. 773-789, 2018. DOI
Abstract
Trust negotiations are mechanisms that enable interaction between previously unknown users. After exchanging various pieces of potentially sensitive information, the participants of a negotiation can decide whether or not to trust one another. Therefore, trust negotiations bring about threats to personal privacy if not carefully considered. This paper presents a framework for representing trust negotiations in the early phases of the Software Development Life Cycle (SDLC). The framework can help software engineers to determine the most suitable policies for the system by detecting conflicts between privacy and trust requirements. More precisely, we extend the SI* modelling language and provide a set of predicates for defining trust and privacy policies and a set of rules for describing the dynamics of the system based on the established policies. The formal representation of the model facilitates its automatic verification. The framework has been validated in a distributed social network scenario for connecting drivers with potential passengers willing to share a journey.

16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom 2017), IEEE, pp. 642-649, 08/2017. DOI
Abstract
The digital witness approach defines the collaboration between IoT devices - from wearables to vehicles - to provide digital evidence through a Digital Chain of Custody to an authorised entity. As one of the cores of the digital witness, binding credentials unequivocally identify the user behind the digital witness. The objective of this article is to perform a critical analysis of the digital witness approach from the perspective of privacy, and to propose solutions that help include some notions of privacy in the scheme (for those cases where it is possible). In addition, digital anonymous witnessing as a tradeoff mechanism between the original approach and privacy requirements is proposed. This is a clear challenge in this context given the restriction that the identities of the links in the digital chain of custody should be known.
Future Generation Computer Systems, vol. 75, Elsevier, pp. 46–57, 10/2017. DOI
Abstract
The Internet of Things (IoT) envisions a world covered with billions of smart, interacting things capable of offering all sorts of services to near and remote entities. The benefits and comfort that the IoT will bring about are undeniable, however, these may come at the cost of an unprecedented loss of privacy. In this paper we look at the privacy problems of one of the key enablers of the IoT, namely wireless sensor networks, and analyse how these problems may evolve with the development of this complex paradigm. We also identify further challenges which are not directly associated with already existing privacy risks but will certainly have a major impact in our lives if not taken into serious consideration.

16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom 2017), IEEE, pp. 626-633, 08/2017. DOI
Abstract
The Internet of Things (IoT) brings new challenges to digital forensics. Given the number and heterogeneity of devices in such scenarios, it bring extremely difficult to carry out investigations without the cooperation of individuals. Even if they are not directly involved in the offense, their devices can yield digital evidence that might provide useful clarification in an investigation. However, when providing such evidence they may leak sensitive personal information. This paper proposes PRoFIT; a new model for IoT-forensics that takes privacy into consideration by incorporating the requirements of ISO/IEC 29100:2011 throughout the investigation life cycle. PRoFIT is intended to lay the groundwork for the voluntary cooperation of individuals in cyber crime investigations.

XIV Reunión Española sobre Criptología y Seguridad de la Información, pp. 209-213, 10/2016.
Abstract
La Internet de las Cosas (en inglés, Internet of Things (IoT)) es una evolución de la Internet tal y como lo conocemos. Esta nueva versión de Internet incorpora objetos de la vida cotidiana, rompiendo así barrera de los digital y extendiéndose al mundo físico. Estos objetos interactuarán entre sí y con otras entidades tanto de manera local como remota, y estarán dotados de cierta capacidad computacional y sensores para que sean conscientes de lo que ocurre en su entorno. Esto traerá consigo un sinfín de posibilidades y nuevos servicios, pero también dará lugar a nuevos y mayores riesgos de privacidad para los ciudadanos. En este artículo, estudiamos los problemas de privacidad actuales de una de las tecnologías claves para el desarrollo de este prometedor paradigma, las redes de sensores, y analizamos como pueden evolucionar y surgir nuevos riesgos de privacidad al ser completamente integradas en la Internet.

12th International Workshop on Security and Trust Management (STM), vol. LNCS 9871, Springer, pp. 98-105, 09/2016. DOI
Abstract
Software engineering and information security have traditionally followed divergent paths but lately some efforts have been made to consider security from the early phases of the Software Development Life Cycle (SDLC). This paper follows this line and concentrates on the incorporation of trust negotiations during the requirements engineering phase. More precisely, we provide an extension to the SI* modelling language, which is further formalised using answer set programming specifications to support the automatic verification of the model and the detection of privacy conflicts caused by trust negotiations.
Accountability and Security in the Cloud, M. Felici, and C. Fernandez-Gago Eds., Lecture Notes in Computer Science 8937, Springer International Publishing, pp. 114-125, 2015. DOI
Abstract
In this paper we tackle the problem of privacy and confidentiality in Identity Management as a Service (IDaaS). The adoption of cloud computing technologies by organizations has fostered the externalization of the identity management processes, shaping the concept of Identity Management as a Service. However, as it has happened to other cloud-based services, the cloud poses serious risks to the users, since they lose the control over their data. As part of this work, we analyze these concerns and present a model for privacy-preserving IDaaS, called BlindIdM, which is designed to provide data privacy protection through the use of cryptographic safeguards.
Information Sciences, vol. 321, Elsevier, pp. 205 - 223, 07/2015. DOI
Abstract
Wireless sensor networks (WSNs) are continually exposed to many types of attacks. Among these, the attacks targeted at the base station are the most devastating ones since this essential device processes and analyses all traffic generated in the network. Moreover, this feature can be exploited by a passive adversary to determine its location based on traffic analysis. This receiver-location privacy problem can be reduced by altering the traffic pattern of the network but the adversary may still be able to reach the base station if he gains access to the routing tables of a number of sensor nodes. In this paper we present HISP-NC (Homogenous Injection for Sink Privacy with Node Compromise protection), a receiver-location privacy solution that consists of two complementary schemes which protect the location of the base station in the presence of traffic analysis and node compromise attacks. The HISP-NC data transmission protocol prevents traffic analysis by probabilistically hiding the flow of real traffic with moderate amounts of fake traffic. Moreover, HISP-NC includes a perturbation mechanism that modifies the routing tables of the nodes to introduce some level of uncertainty in attackers capable of retrieving the routing information from the nodes. Our scheme is validated both analytically and experimentally through extensive simulations.

Information Systems Frontiers, vol. 14, Springer, pp. 527-540, July 2012. DOI
Abstract
Our society is becoming increasingly more IT-oriented, and the images and sounds that reflect our daily life are being stored mainly in a digital form. This digital personal life can be part of the home multimedia contents, and users demand access and possibly share these contents (such as photographs, videos, and music) in an ubiquitous way: from any location and with any device. The purpose of this article is twofold. First, we introduce the Feel@Home system, whose main objective is to enable the previously mentioned vision of an ubiquitous digital personal life. Second, we describe the security architecture of Feel@Home, analyzing the security and privacy requirements that identify which threats and vulnerabilities must be considered, and deriving the security building blocks that can be used to protect both IMS-based and VPN-based solutions.
IEEE CloudCom 2012, IEEE Computer Society, pp. 241 - 248, Dec 2012. DOI
Abstract
The inclusion of identity management in the cloud computing landscape represents a new business opportunity for providing what has been called Identity Management as a Service (IDaaS). Nevertheless, IDaaS introduces the same kind of problems regarding privacy and data confidentiality as other cloud services; on top of that, the nature of the outsourced information (users’ identity) is critical. Traditionally, cloud services (including IDaaS) rely only on SLAs and security policies to protect the data, but these measures have proven insufficient in some cases; recent research has employed advanced cryptographic mechanisms as an additional safeguard. Apart from this, there are several identity management schemes that could be used for realizing IDaaS systems in the cloud; among them, OpenID has gained crescent popularity because of its open and decentralized nature, which makes it a prime candidate for this task. In this paper we demonstrate how a privacy-preserving IDaaS system can be implemented using OpenID Attribute Exchange and a proxy re-encryption scheme. Our prototype enables an identity provider to serve attributes to other parties without being able to read their values. This proposal constitutes a novel contribution to both privacy and identity management fields. Finally, we discuss the performance and economical viability of our proposal.

21st International Conference on Computer Communications and Networks (ICCCN), IEEE Computer Society, pp. 1-5, Jul 2012. DOI
Abstract
Migration to an electronically controlled electrical grid to transmit, distribute, and deliver power to consumers has helped enhance the reliability and efficiency of conventional electricity systems. At the same time, this digitally enabled technology called the Smart Grid has brought new challenges to businesses and consumers alike. A key component of such a grid is the smart-metering technology, which is used to collect energy consumption data from homes and transmitting it back to power distributors. A crucial concern is the privacy related to the collection and use of energy consumption data. We present an analysis of Smart Grid privacy issues and discuss recently proposed solutions that can protect the privacy of Smart Grid users.
Wireless Personal Communications, vol. 73, Springer, pp. 23-50, Nov 2013, 2012. DOI
Abstract
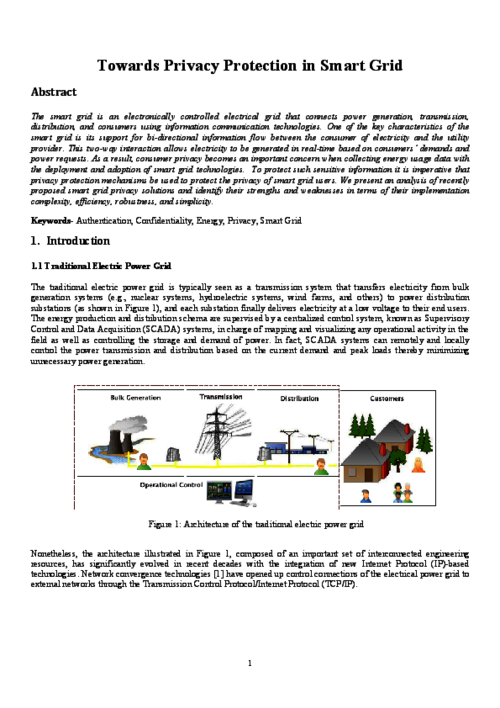
The smart grid is an electronically controlled electrical grid that connects power generation, transmission, distribution, and consumers using information communication technologies. One of the key characteristics of the smart grid is its support for bi-directional information flow between the consumer of electricity and the utility provider. This two-way interaction allows electricity to be generated in real-time based on consumers’ demands and power requests. As a result, consumer privacy becomes an important concern when collecting energy usage data with the deployment and adoption of smart grid technologies. To protect such sensitive information it is imperative that privacy protection mechanisms be used to protect the privacy of smart grid users. We present an analysis of recently proposed smart grid privacy solutions and identify their strengths and weaknesses in terms of their implementation complexity, efficiency, robustness, and simplicity.
Proceedings of the First International Conference on Security of Internet of Things, ACM, pp. 172–178, 2012. DOI
Abstract
While there has been considerable progress in the research and technological development (RTD) of the Internet of Things (IoT), there is still considerable RTD required by international communities for the trust, privacy and security research challenges arising from the constitution of the IoT architectures, infrastructures, communications, devices, objects, applications and services. In this paper, we present an thorough analysis of the ongoing and future RTD work, specifically in Europe, regarding trust, privacy and security of the Internet of Things with a view towards enabling international cooperation efforts around the globe to solve these major research challenges.
3rd Symposium of Ubiquitous Computing and Ambient Intelligence 2008, Advances in Soft Computing 51/2009, Springer, pp. 134-138, October, 2008. DOI
Abstract
Seamless human identification and authentication in the information system is a fundamental step towards the transparent interaction between the user and its context proposed in ambient intelligence. In this context, the IDENTICA project is aimed to the design and implementation of a distributed authentication platform based on biometrics (i.e. voice and facial image) and personal documentation. In this paper, we present our work in this project focused on the secure integration of RFID technology in personal documentation in order to provide seamless identity validation. Our actual work status, first results and future directions are described in detail.

 ]
]