]
] International Journal of Information Security, Springer, 2020. DOI
Abstract
Nowadays, smart home devices like Amazon Echo and Google Home have reached mainstream popularity.
Being in the homes of users, these devices are intrinsically intrusive, being able to access details such as users' name, gender, home address, calendar appointments and others.
There are growing concerns about indiscriminate data collection and invasion of user privacy in smart home devices, but studies show that perceived benefits are exceeding perceived risks when it comes to consumers.
As a result, consumers are placing a lot of trust in these devices, sometimes without realizing it.
Improper trust assumptions and security controls can lead to unauthorized access and control of the devices, which can result in serious consequences.
In this paper, we explore the behaviour of devices such as Amazon Echo and Google Home in a smart home setting with respect to trust relationships and propose a trust model to improve these relationships among all the involved actors.
We have evaluated how trust was built and managed from the initial set up phase to the normal operation phase, during which we performed a number of interaction tests with different types of users (i.e. owner, guests).
As a result, we were able to assess the effectiveness of the provided security controls and identify potential relevant security issues. In order to address the identified issues, we defined a trust model and propose a solution based on it for further securing smart home systems.

IEEE Internet of Things Journal, vol. 6, issue 5, IEEE Computer Society, pp. 8038-8045, 10/2019. DOI
Abstract
Edge Computing paradigms are expected to solve some major problems affecting current application scenarios that rely on Cloud computing resources to operate. These novel paradigms will bring computational resources closer to the users and by doing so they will not only reduce network latency and bandwidth utilization but will also introduce some attractive context-awareness features to these systems. In this paper we show how the enticing features introduced by Edge Computing paradigms can be exploited to improve security and privacy in the critical scenario of vehicular networks (VN), especially existing authentication and revocation issues. In particular, we analyze the security challenges in VN and describe three deployment models for vehicular edge computing, which refrain from using vehicular- to-vehicular communications. The result is that the burden imposed to vehicles is considerably reduced without sacrificing the security or functional features expected in vehicular scenarios.

IEEE Internet of Things Journal, vol. 6, issue 3, IEEE Computer Society, pp. 4774-4781, 06/2019. DOI
Abstract
The Internet of Things (IoT) and Edge Computing are starting to go hand in hand. By providing cloud services close to end-users, edge paradigms enhance the functionality of IoT deployments, and facilitate the creation of novel services such as augmented systems. Furthermore, the very nature of these paradigms also enables the creation of a proactive defense architecture, an immune system, which allows authorized immune cells (e.g., virtual machines) to traverse edge nodes and analyze the security and consistency of the underlying IoT infrastructure. In this article, we analyze the requirements for the development of an immune system for the IoT, and propose a security architecture that satisfies these requirements. We also describe how such a system can be instantiated in Edge Computing infrastructures using existing technologies. Finally, we explore the potential application of immune systems to other scenarios and purposes.

IEEE Computer, vol. 51, issue 7, IEEE Computer Society, pp. 16-25, 07/2018. DOI
KSII Transactions on Internet and Information Systems, vol. 12, no. 8, KSII, pp. 3567-3588, 08/2018. DOI
Abstract
In the Internet of Things (IoT) concept, devices communicate autonomously with applications in the Internet. A significant aspect of IoT that makes it stand apart from present-day networked devices and applications is a) the very large number of devices, produced by diverse makers and used by an even more diverse group of users; b) the applications residing and functioning in what were very private sanctums of life e.g. the car, home, and the people themselves. Since these diverse devices require high-level security, an operational model for an IoT system is required, which has built-in security. We have proposed the societal model as a simple operational model. The basic concept of the model is borrowed from human society – there will be infants, the weak and the handicapped who need to be protected by guardians. This natural security mechanism works very well for IoT networks which seem to have inherently weak security mechanisms. In this paper, we discuss the requirements of the societal model and examine its feasibility by doing a proof-of-concept implementation.
IEEE Communications Surveys and Tutorials, vol. 20, issue 4, IEEE, pp. 3453-3495, 07/2018. DOI
Abstract
As the deployment of Internet of Things (IoT) is experiencing an exponential growth, it is no surprise that many recent cyber attacks are IoT-enabled: The attacker initially exploits some vulnerable IoT technology as a first step towards compromising a critical system that is connected, in some way, with the IoT. For some sectors, like industry, smart grids, transportation and medical services, the significance of such attacks is obvious, since IoT technologies are part of critical backend systems. However, in sectors where IoT is usually at the enduser side, like smart homes, such attacks can be underestimated, since not all possible attack paths are examined. In this paper we survey IoT-enabled cyber attacks, found in all application domains since 2010. For each sector, we emphasize on the latest, verified IoT-enabled attacks, based on known real-world incidents and published proof-of-concept attacks. We methodologically analyze representative attacks that demonstrate direct, indirect and subliminal attack paths against critical targets. Our goal is threefold: (i) To assess IoT-enabled cyber attacks in a risk-like approach, in order to demonstrate their current threat landscape; (ii) To identify hidden and subliminal IoT-enabled attack paths against critical infrastructures and services, and (iii) To examine mitigation strategies for all application domains.
Future Generation Computer Systems, vol. 75, Elsevier, pp. 46–57, 10/2017. DOI
Abstract
The Internet of Things (IoT) envisions a world covered with billions of smart, interacting things capable of offering all sorts of services to near and remote entities. The benefits and comfort that the IoT will bring about are undeniable, however, these may come at the cost of an unprecedented loss of privacy. In this paper we look at the privacy problems of one of the key enablers of the IoT, namely wireless sensor networks, and analyse how these problems may evolve with the development of this complex paradigm. We also identify further challenges which are not directly associated with already existing privacy risks but will certainly have a major impact in our lives if not taken into serious consideration.

Information Sciences, vol. 396, Elsevier, pp. 72-82, 2017. DOI
Abstract
The Internet of Things (IoT) is a paradigm based on the interconnection of everyday objects. It is expected that the ‘things’ involved in the IoT paradigm will have to interact with each other, often in uncertain conditions. It is therefore of paramount importance for the success of IoT that there are mechanisms in place that help overcome the lack of certainty. Trust can help achieve this goal. In this paper, we introduce a framework that assists developers in including trust in IoT scenarios. This framework takes into account trust, privacy and identity requirements as well as other functional requirements derived from IoT scenarios to provide the different services that allow the inclusion of trust in the IoT.

Security Solutions and Applied Cryptography in Smart Grid Communications, IGI Global, USA, IGI Global, pp. 137-158, 2017. DOI
Abstract
Transparency in control transactions under a secure network architecture is a key topic that must be discussed when aspects related to interconnection between heterogeneous cyber-physical systems (CPSs) arise. The interconnection of these systems can be addressed through an enforcement policy system responsible for managing access control according to the contextual conditions. However, this architecture is not always adequate to ensure a rapid interoperability in extreme crisis situations, and can require an interconnection strategy that permits the timely authorized access from anywhere at any time. To do this, a set of interconnection strategies through the Internet must be studied to explore the ability of control entities to connect to the remote CPSs and expedite their operations, taking into account the context conditions. This research constitutes the contribution of this chapter, where a set of control requirements and interoperability properties are identified to discern the most suitable interconnection strategies.
XIV Reunión Española sobre Criptología y Seguridad de la Información, pp. 209-213, 10/2016.
Abstract
La Internet de las Cosas (en inglés, Internet of Things (IoT)) es una evolución de la Internet tal y como lo conocemos. Esta nueva versión de Internet incorpora objetos de la vida cotidiana, rompiendo así barrera de los digital y extendiéndose al mundo físico. Estos objetos interactuarán entre sí y con otras entidades tanto de manera local como remota, y estarán dotados de cierta capacidad computacional y sensores para que sean conscientes de lo que ocurre en su entorno. Esto traerá consigo un sinfín de posibilidades y nuevos servicios, pero también dará lugar a nuevos y mayores riesgos de privacidad para los ciudadanos. En este artículo, estudiamos los problemas de privacidad actuales de una de las tecnologías claves para el desarrollo de este prometedor paradigma, las redes de sensores, y analizamos como pueden evolucionar y surgir nuevos riesgos de privacidad al ser completamente integradas en la Internet.

Computer Networks, vol. 57, Elsevier, pp. 2266–2279, July 2013. DOI
Abstract
In the Internet of Things, services can be provisioned using centralized architectures, where central entities acquire, process, and provide information. Alternatively, distributed architectures, where entities at the edge of the network exchange information and collaborate with each other in a dynamic way, can also be used. In order to understand the applicability and viability of this distributed approach, it is necessary to know its advantages and disadvantages – not only in terms of features but also in terms of security and privacy challenges. The purpose of this paper is to show that the distributed approach has various challenges that need to be solved, but also various interesting properties and strengths.
Ad Hoc Networks, vol. 11, Elsevier, pp. 1091–1104, 2013. DOI
Abstract
The main objective of remote substations is to provide the central system with sensitive information from critical infrastructures, such as generation, distribution or transmission power systems. Wireless sensor networks have been recently applied in this particular context due to their attractive services and inherent benefits, such as simplicity, reliability and cost savings. However, as the number of control and data acquisition systems that use the Internet infrastructure to connect to substations increases, it is necessary to consider what connectivity model the sensor infrastructure should follow: either completely isolated from the Internet or integrated with it as part of the Internet of Things paradigm. This paper therefore addresses this question by providing a thorough analysis of both security requirements and infrastructural requirements corresponding to all those TCP/IP integration strategies that can be applicable to networks with constrained computational resources.

Proceedings of the First International Conference on Security of Internet of Things, ACM, pp. 172–178, 2012. DOI
Abstract
While there has been considerable progress in the research and technological development (RTD) of the Internet of Things (IoT), there is still considerable RTD required by international communities for the trust, privacy and security research challenges arising from the constitution of the IoT architectures, infrastructures, communications, devices, objects, applications and services. In this paper, we present an thorough analysis of the ongoing and future RTD work, specifically in Europe, regarding trust, privacy and security of the Internet of Things with a view towards enabling international cooperation efforts around the globe to solve these major research challenges.
IEEE Computer, vol. 44, no. 9, IEEE, pp. 51 -58, Sept 2011. DOI
Abstract
This paper presents security of Internet of things. In the Internet of Things vision, every physical object has a virtual component that can produce and consume services Such extreme interconnection will bring unprecedented convenience and economy, but it will also require novel approaches to ensure its safe and ethical use. The Internet and its users are already under continual attack, and a growing economy-replete with business models that undermine the Internet’s ethical use-is fully focused on exploiting the current version’s foundational weaknesses.
XI Reunión Española sobre Criptología y Seguridad de la Información (RECSI 2010), pp. 337-342, September, 2010.
Abstract
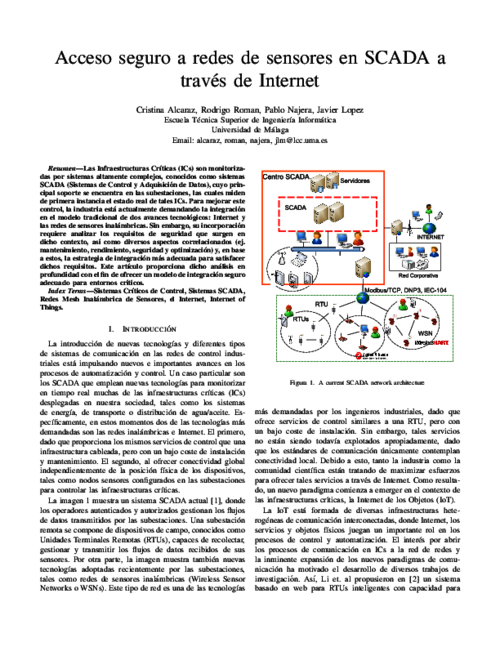
Las Infraestructuras Críticas (ICs) son monitorizadas por sistemas altamente complejos, conocidos como sistemas SCADA (Sistemas de Control y Adquisición de Datos), cuyo principal soporte se encuentra en las subestaciones, las cuales miden de primera instancia el estado real de tales ICs. Para mejorar este control, la industria está actualmente demandando la integración en el modelo tradicional de dos avances tecnológicos: Internet y las redes de sensores inalámbricas. Sin embargo, su incorporación requiere analizar los requisitos de seguridad que surgen en dicho contexto, así como diversos aspectos correlacionados (ej. mantenimiento, rendimiento, seguridad y optimización) y, en base a estos, la estrategia de integración más adecuada para satisfacer dichos requisitos. Este artículo proporciona dicho análisis en profundidad con el fin de ofrecer un modelo de integración seguro adecuado para entornos críticos.