IEEE International Conference on Metaverse Computing, Networking and Applications, 06/2023.
Abstract
In the last few years we have seen many different approaches to incorporate privacy features to blockchains. In the area of cryptocurrencies that would normally mean protecting the identity of the owner of some funds, but there are other applications where privacy is even more important, especially in permissioned blockchains.
Permissioned blockchain platforms, such as Hyperledger Besu or Hyperledger Fabric, already include the concept of private transactions, which essentially defines a sub-group of the blockchain where their participants share some private data.
We want to go one step ahead and propose an extended model for private transactions where the different participants can have a separated view of the same transaction, allowing the integration of Multi-party Computation protocols in the blockchain.
Our work extends Hyperledger Besu's design for private transactions, offering better security properties and a finer grain customization. We cover two specific MPC examples, Private Set Intersection and Byzantine Fault-Tolerant Random Number Generation, and propose a mechanism to run them using smart contract interfaces.

Computer Science Review, vol. 49, no. 100567, Elsevier, 05/2023. DOI
Abstract
Secure Multi-party Computation (SMPC) is a family of protocols which allow some parties to compute a function on their private inputs, obtaining the output at the end and nothing more. In this work, we focus on a particular SMPC problem named Private Set Intersection (PSI). The challenge in PSI is how two or more parties can compute the intersection of their private input sets, while the elements that are not in the intersection remain private. This problem has attracted the attention of many researchers because of its wide variety of applications, contributing to the proliferation of many different approaches. Despite that, current PSI protocols still require heavy cryptographic assumptions that may be unrealistic in some scenarios. In this paper, we perform a Systematic Literature Review of PSI solutions, with the objective of analyzing the main scenarios where PSI has been studied and giving the reader a general taxonomy of the problem together with a general understanding of the most common tools used to solve it. We also analyze the performance using different metrics, trying to determine if PSI is mature enough to be used in realistic scenarios, identifying the pros and cons of each protocol and the remaining open problems.

IEEE Access , IEEE, 2022. DOI
Abstract
Neural networks based cryptography has seen a significant growth since the introduction of adversarial cryptography which makes use of Generative Adversarial Networks (GANs) to build neural networks that can learn encryption. The encryption has been proven weak at first but many follow up works have shown that the neural networks can be made to learn the One Time Pad (OTP) and produce perfectly secure ciphertexts. To the best of our knowledge, existing works only considered communications between two or three parties. In this paper, we show how multiple neural networks in an adversarial setup can remotely synchronize and establish a perfectly secure communication in the presence of different attackers eavesdropping their communication. As an application, we show how to build Secret Sharing Scheme based on this perfectly secure multi-party communication. The results show that it takes around 45,000 training steps for 4 neural networks to synchronize and reach equilibria. When reaching equilibria, all the neural networks are able to communicate between each other and the attackers are not able to break the ciphertexts exchanged between them.
19th International Conference on Security and Cryptography (SECRYPT 2022), Scitepress, pp. 249-260, 07/2022. DOI
Abstract
Crowd Counting is a very interesting problem aiming at counting people typically based on density averages and/or aerial images. This is very useful to prevent crowd crushes, especially on urban environments with high crowd density, or to count people in public demonstrations. In addition, in the last years, it has become of paramount importance for pandemic management. For those reasons, giving users automatic mechanisms to anticipate high risk situations is essential. In this work, we analyze ID-based Crowd Counting, and propose a real-time Crowd Counting system based on the Ephemeral ID broadcast by contact tracing applications on wearable devices. We also performed some simulations that show the accuracy of our system in different situations.

IEEE Transactions on Vehicular Technology, vol. 70, no. 5, IEEE, pp. 4001 - 4010, 05/2021. DOI
Abstract
New mobility paradigms have appeared in recent years, and everything suggests that some more are coming. This fact makes apparent the necessity of modernizing the road infrastructure, the signalling elements and the traffic management systems. Many initiatives have emerged around the term Intelligent Transport System (ITS) in order to define new scenarios and requirements for this kind of applications. We even have two main competing technologies for implementing Vehicular communication protocols (V2X), C-V2X and 802.11p, but neither of them is widely deployed yet.
One of the main barriers for the massive adoption of those technologies is governance. Current solutions rely on the use of a public key infrastructure that enables secure collaboration between the different entities in the V2X ecosystem, but given its global scope, managing such infrastructure requires reaching agreements between many parties, with conflicts of interest between automakers and telecommunication operators. As a result, there are plenty of use cases available and two mature communication technologies, but the complexity at the business layer is stopping the drivers from taking advantage of ITS applications.
Blockchain technologies are defining a new decentralized paradigm for most traditional applications, where smart contracts provide a straightforward mechanism for decentralized governance. In this work, we propose an approach for decentralized V2X (D-V2X) that does not require any trusted authority and can be implemented on top of any communication protocol. We also define a proof-of-concept technical architecture on top of a cheap and highly secure System-on-Chip (SoC) that could allow for massive adoption of D-V2X.

V Jornadas Nacionales de Investigación en Ciberseguridad (JNIC), 06/2019.
Abstract
Cada día es más frecuente encontrar servicios en internet gestionados desde plataformas online y con la expansión de la tecnología IoT, los smartphones, las smartTV y otros tantos dispositivos: la autenticación, la distribución y al fin y al cabo, la comunicación entre extremos puede verse seriamente comprometida si dicha plataforma es atacada. La inclusión de nuevas medidas de seguridad en este tipo de ecosistemas requiere de un cambios sustancial de la arquitectura subyacente en muchos casos, por lo que su avance es lento.
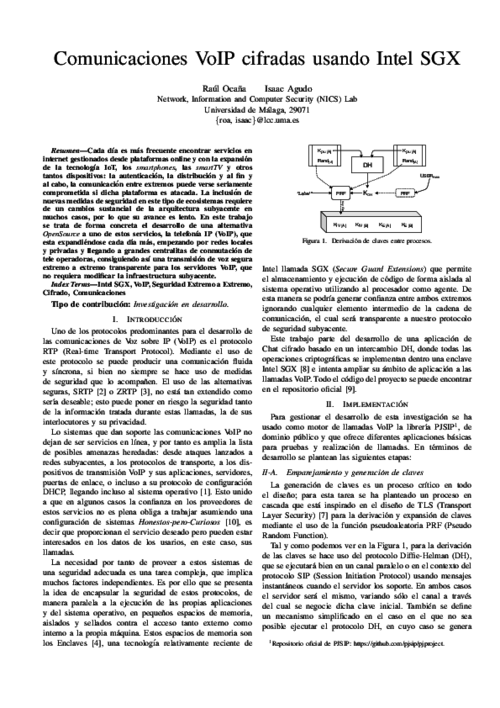
En este trabajo se trata de forma concreta el desarrollo de una alternativa OpenSource a uno de estos servicios, la telefonía IP (VoIP), que esta expandiéndose cada día más, empezando por redes locales y privadas y llegando a grandes centralitas de conmutación de tele operadoras, consiguiendo así una transmisión de voz segura extremo a extremo transparente para los servidores VoIP, que no requiera modificar la infraestructura subyacente.
XIV Jornadas de Ingeniería Telemática (JITEL 2019), 10/2019.
Abstract
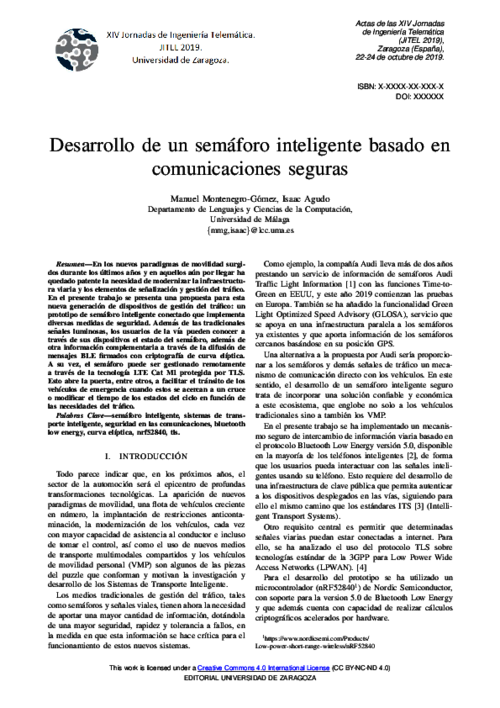
En los nuevos paradigmas de movilidad surgidos durante los últimos años y en aquellos aún por llegar ha quedado patente la necesidad de modernizar la infraestructura viaria y los elementos de señalización y gestión del tráfico. En el presente trabajo se presenta una propuesta para esta nueva generación de dispositivos de gestión del tráfico: un prototipo de semáforo inteligente conectado que implementa diversas medidas de seguridad. Además de las tradicionales señales luminosas, los usuarios de la vía pueden conocer a través de sus dispositivos el estado del semáforo, además de otra información complementaria a través de la difusión de mensajes BLE firmados con criptografía de curva elíptica. A su vez, el semáforo puede ser gestionado remotamente a través de la tecnología LTE Cat M1 protegida por TLS. Esto abre la puerta, entre otros, a facilitar el tránsito de los vehículos de emergencia cuando estos se acercan a un cruce o modificar el tiempo de los estados del ciclo en función de las necesidades del tráfico.
IET Information Security, vol. 13, issue 5, IET, pp. 498 -- 507, 09/2019.
Abstract
Escrowed decryption schemes (EDSs) are public-key encryption schemes with an escrowed decryption functionality that allows authorities to decrypt encrypted messages under investigation, following a protocol that involves a set of trusted entities called `custodians'; only if custodians collaborate, the requesting authority is capable of decrypting encrypted data. This type of cryptosystem represents an interesting trade-off to privacy versus surveillance dichotomy. In this study, the authors propose two EDSs where they use proxy re-encryption to build the escrowed decryption capability, so that custodians re-encrypt ciphertexts, in a distributed way, upon request from an escrow authority, and the re-encrypted ciphertexts can be opened only by the escrow authority. Their first scheme, called EDS, follows an all-or-nothing approach, which means that escrow decryption only works when all custodians collaborate. Their second scheme, called threshold EDS, supports a threshold number of custodians for the escrow decryption operation. They propose definitions of semantic security with respect to the authorities, custodians and external entities, and prove the security of their schemes, under standard pairing-based hardness assumptions. Finally, they present a theoretical and experimental analysis of the performance of both schemes, which show that they are applicable to real-world scenarios.

International Conference on Information Systems Education and Research (AIS SIGED 2019), 12/2019.

XIV Jornadas de Ingeniería Telemática, pp. 50-53, 10/2019. DOI
Abstract
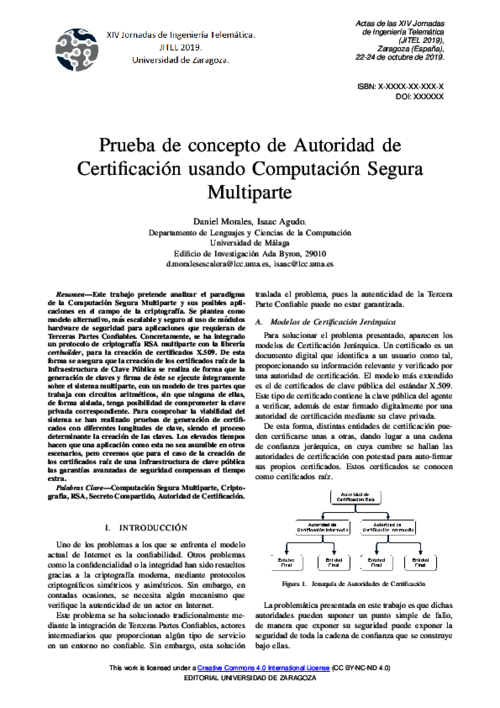
Este trabajo pretende analizar el paradigma de la Computación Segura Multiparte y sus posibles aplicaciones en el campo de la criptografía. Se plantea como modelo alternativo, mas escalable y seguro al uso de módulos hardware de seguridad para aplicaciones que requieran de Terceras Partes Confiables. Concretamente, se ha integrado un protocolo de criptografía RSA multiparte con la librería certbuilder, para la creación de certificados X.509. De esta forma se asegura que la creación de los certificados raíz de la Infraestructura de Clave Publica se realiza de forma que la generación de claves y firma de este se ejecute íntegramente sobre el sistema multiparte, con un modelo de tres partes que trabaja con circuitos aritméticos, sin que ninguna de ellas, de forma aislada, tenga posibilidad de comprometer la clave privada correspondiente. Para comprobar la viabilidad del sistema se han realizado pruebas de generación de certificados con diferentes longitudes de clave, siendo el proceso determinante la creación de las claves. Los elevados tiempos hacen que una aplicación como esta no sea asumible en otros escenarios, pero creemos que para el caso de la creación de los certificados raíz de una infraestructura de clave pública las garantías avanzadas de seguridad compensan el tiempo extra.
31st Annual IFIP WG 11.3 Conference on Data and Applications Security and Privacy (DBSec'17), vol. LNCS 10359, Springer, pp. 453-472, 07/2017. DOI
Abstract
In this paper, we analyze how key compromise affects the protocol by Nguyen et al. presented at ESORICS 2016, an authenticated key agreement protocol mediated by a proxy entity, restricted to only symmetric encryption primitives and intended for IoT environments. This protocol uses long-term encryption tokens as intermediate values during encryption and decryption procedures, which implies that these can be used to encrypt and decrypt messages without knowing the cor- responding secret keys. In our work, we show how key compromise (or even compromise of encryption tokens) allows to break forward secu- rity and leads to key compromise impersonation attacks. Moreover, we demonstrate that these problems cannot be solved even if the affected user revokes his compromised secret key and updates it to a new one. The conclusion is that this protocol cannot be used in IoT environments, where key compromise is a realistic risk.

Journal of Network and Computer Applications, vol. 87, Elsevier, pp. 193-209, 06/2017. DOI
Abstract
This paper analyzes the secure access delegation problem, which occurs naturally in the cloud, and postulate that Proxy Re-Encryption is a feasible cryptographic solution, both from the functional and efficiency perspectives. Proxy re-encryption is a special type of public-key encryption that permits a proxy to transform ciphertexts from one public key to another, without the proxy being able to learn any information about the original message. Thus, it serves as a means for delegating decryption rights, opening up many possible applications that require of delegated access to encrypted data. In particular, sharing information in the cloud is a prime example. In this paper, we review the main proxy re-encryption schemes so far, and provide a detailed analysis of their characteristics. Additionally, we also study the efficiency of selected schemes, both theoretically and empirically, based on our own implementation. Finally, we discuss some applications of proxy re-encryption, with a focus on secure access delegation in the cloud.

III Jornadas Nacionales de Investigación en Ciberseguridad, URJC, pp. 174-175, 06/2017.
Abstract
En este artículo presentamos un sistema que permite delegación de acceso a información cifrada para Apache Hadoop, de forma segura y transparente al usuario. Para ello usamos técnicas criptográficas avanzadas basadas en el recifrado delegado. Con este sistema, es posible almacenar en Hadoop los datos de forma cifrada y delegar de forma segura el acceso a los nodos de computación. El funcionamiento es transparente ya que se integra con la capa del sistema de ficheros nativa HDFS. Además, el recifrado delegado permite hacer rotación de claves de cifrado de forma segura y rápida.
Security and Communication Networks, vol. 9, issue 12, Wiley, pp. 1769-1785, 08/2016. DOI
Abstract
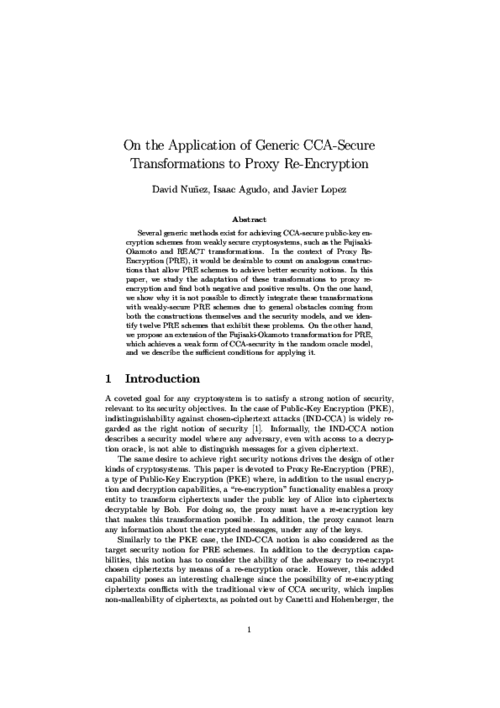
Several generic methods exist for achieving chosen-ciphertext attack (CCA)-secure public-key encryption schemes from weakly secure cryptosystems, such as the Fujisaki–Okamoto and REACT transformations. In the context of proxy re-encryption (PRE), it would be desirable to count on analogous constructions that allow PRE schemes to achieve better security notions. In this paper, we study the adaptation of these transformations to proxy re-encryption and find both negative and positive results. On the one hand, we show why it is not possible to directly integrate these transformations with weakly secure PRE schemes because of general obstacles coming from both the constructions themselves and the security models, and we identify 12 PRE schemes that exhibit these problems. On the other hand, we propose an extension of the Fujisaki–Okamoto transformation for PRE, which achieves a weak form of CCA security in the random oracle model, and we describe the sufficient conditions for applying it
XIV Reunión Española sobre Criptología y Seguridad de la Información, pp. 174-179, 10/2016.
Abstract
El recifrado delegado (proxy re-encryption) es un tipo de cifrado de clave pública que permite delegar la capacidad de transformar textos cifrados de una clave pública a otra, sin que se pueda obtener ninguna información sobre el mensaje subyacente. Por este motivo, representa un candidato natural para construir mecanismos criptográficos de control de acceso. En este artículo estudiamos algunos de los problemas de seguridad de este tipo de criptosistemas. En primer lugar, examinamos las nociones de seguridad e identificamos una nueva familia paramétrica de modelos de ataque, que considera la disponibilidad tanto del oráculo de descifrado como de recifrado. En segundo lugar, estudiamos la aplicabilidad de transformaciones genéricas para mejorar la seguridad, centrándonos en la transformación Fujisaki-Okamoto, y formulamos las condiciones que nos permiten aplicarla.

10th International IFIP Summer School on Privacy and Identity Management, pp. 187-204, 2016. DOI
Abstract
Transparency and verifiability are necessary aspects of accountability, but care needs to be taken that auditing is done in a privacy friendly way. There are situations where it would be useful for certain actors to be able to make restricted views within service provision chains on accountability evidence, including logs, available to other actors with specific governance roles. For example, a data subject or a Data Protection Authority (DPA) might want to authorize an accountability agent to act on their behalf, and be given access to certain logs in a way that does not compromise the privacy of other actors or the security of involved data processors. In this paper two cryptographic-based techniques that may address this issue are proposed and assessed.

10th ACM Symposium on Information, Computer and Communications Security (AsiaCCS), pp. 179-189, 04/2015. DOI
Abstract
The use of alternative foundations for constructing more secure and efficient cryptographic schemes is a topic worth exploring. In the case of proxy re-encryption, the vast majority of schemes are based on number theoretic problems such as the discrete logarithm. In this paper we present NTRUReEncrypt, a new bidirectional and multihop proxy re-encryption scheme based on NTRU, a widely known lattice-based cryptosystem. We provide two versions of our scheme: the first one is based on the conventional NTRU encryption scheme and, although it lacks a security proof, remains as efficient as its predecessor; the second one is based on a variant of NTRU proposed by Stehlé and Steinfeld, which is proven CPA-secure under the hardness of the Ring-LWE problem. To the best of our knowledge, our proposals are the first proxy re-encryption schemes to be based on the NTRU primitive. In addition, we provide experimental results to show the efficiency of our proposal, as well as a comparison with previous proxy re-encryption schemes, which confirms that our first scheme outperforms the rest by an order of magnitude.
28th IEEE Computer Security Foundations Symposium, IEEE Computer Society, pp. 290-301, 07/2015. DOI
Abstract
Proxy Re-Encryption (PRE) is a type of Public-Key Encryption (PKE) which provides an additional re-encryption functionality. Although PRE is inherently more complex than PKE, attack models for PRE have not been developed further than those inherited from PKE. In this paper we address this gap and define a parametric family of attack models for PRE, based on the availability of both the decryption and re-encryption oracles during the security game. This family enables the definition of a set of intermediate security notions for PRE that ranges from ``plain'' IND-CPA to ``full'' IND-CCA. We analyze some relations among these notions of security, and in particular, the separations that arise when the re-encryption oracle leaks re-encryption keys. In addition, we discuss which of these security notions represent meaningful adversarial models for PRE. Finally, we provide an example of a recent ``CCA1- secure'' scheme from PKC 2014 whose security model does not capture chosen-ciphertext attacks through re-encryption and for which we describe an attack under a more realistic security notion. This attack emphasizes the fact that PRE schemes that leak re-encryption keys cannot achieve strong security notions.

Accountability and Security in the Cloud, M. Felici, and C. Fernandez-Gago Eds., Lecture Notes in Computer Science 8937, Springer International Publishing, pp. 114-125, 2015. DOI
Abstract
In this paper we tackle the problem of privacy and confidentiality in Identity Management as a Service (IDaaS). The adoption of cloud computing technologies by organizations has fostered the externalization of the identity management processes, shaping the concept of Identity Management as a Service. However, as it has happened to other cloud-based services, the cloud poses serious risks to the users, since they lose the control over their data. As part of this work, we analyze these concerns and present a model for privacy-preserving IDaaS, called BlindIdM, which is designed to provide data privacy protection through the use of cryptographic safeguards.
International Journal of Information Security, vol. 13, issue 2, Springer, pp. 199-215, 2014. DOI
Abstract
Identity management is an almost indispensable component of today’s organizations and companies, as it plays a key role in authentication and access control; however, at the same time it is widely recognized as a costly and time-consuming task. The advent of cloud computing technologies, together with the promise of flexible, cheap and efficient provision of services, has provided the opportunity to externalize such a common process, shaping what has been called Identity Management as a Service (IDaaS). Nevertheless, as in the case of other cloud-based services, IDaaS brings with it great concerns regarding security and privacy, such as the loss of control over the outsourced data. In this paper we analyze these concerns and propose BlindIdM, a model for privacy-preserving IDaaS with a focus on data privacy protection. In particular, we describe how a SAML-based system can be augmented to employ proxy re-encryption techniques for achieving data condentiality with respect to the cloud provider, while preserving the ability to supply the identity service. This is an innovative contribution to both the privacy and identity management landscapes.
Computer Standards & Interfaces, Special Issue on Security in Information Systems, vol. 36, issue 4, Elsevier, pp. 792-800, 2014. DOI
Abstract
Trust is an essential feature of any system where entities have to collaborate among them. Trust can assist entities making decisions about what is the best entity for establishing a certain collaboration. It would be desirable to simulate behaviour of users as in social environments where they tend to establish relationships or to trust users who have common interests or share some of their opinions, i.e., users who are similar to them to some extent. Thus, in this paper we first introduce the concept of context similarity among entities and from it we derive a similarity network which can be seen as a graph. Based on this similarity network we dene a trust model that allows us also to establish trust along a path of entities. A possible applications of our model are proximity-based trust establishment. We validate our model in this scenario.

IEEE International Conference on Cloud Computing Technology and Science (CloudCom 2014), IEEE, pp. 374-379, 12/2014. DOI
Abstract
Among Big Data technologies, Hadoop stands out for its capacity to store and process large-scale datasets. However, although Hadoop was not designed with security in mind, it is widely used by plenty of organizations, some of which have strong data protection requirements. Traditional access control solutions are not enough, and cryptographic solutions must be put in place to protect sensitive information. In this paper, we describe a cryptographically-enforced access control system for Hadoop, based on proxy re-encryption. Our proposed solution fits in well with the outsourcing of Big Data processing to the cloud, since information can be stored in encrypted form in external servers in the cloud and processed only if access has been delegated. Experimental results show that the overhead produced by our solution is manageable, which makes it suitable for some applications.

|
"Procedings of the 10th European Workshop on Public Key Infrastructures, Services and Applications", 10th European Workshop on Public Key Infrastructures, Services and Applications, LNCS, vol. 8341, Springer, 2014. DOI  |  |
Ph.D Symposium of the European Conference on Service-Oriented and Cloud Computing (ESOCC) 2013, September 2013.
Abstract
The advent of cloud computing has provided the opportunity to externalize the identity management processes, shaping what has been called Identity Management as a Service (IDaaS). However, as in the case of other cloud-based services, IDaaS brings with it great concerns regarding security and privacy, such as the loss of control over the outsourced data. As part of this PhD thesis, we analyze these concerns and propose BlindIdM, a model for privacy-preserving IDaaS with a focus on data privacy protection through the use of proxy re-encryption.
Computers & Security, vol. 39 (B), Elsevier, pp. 117-126, 11/2013. DOI
Abstract
Continuous authentication is mainly associated with the use of biometrics to guarantee that a resource is being accessed by the same user throughout the usage period. Wireless devices can also serve as a supporting technology for continuous authentication or even as a complete alternative to biometrics when accessing proximity-based services. In this paper we present the implementation of a secure, non-invasive continuous authentication scheme supported by the use of Wearable Wireless Devices (WWD), which allow users to gain access to proximity-based services while preserving their privacy. Additionally we devise an improved scheme that circumvents some of the limitations of our implementation.

7th IFIP WG 11.11 International Conference on Trust Management (IFIPTM 2013), C. Fernandez-Gago, I. Agudo, F. Martinelli, and S. Pearson Eds., AICT 401, Springer, pp. 255-262, Jun 2013. DOI
Abstract
The Future Internet (FI) comprises scenarios where many heterogeneous and dynamic entities must interact to provide services (e.g., sensors, mobile devices and information systems in smart city scenarios). The dynamic conditions under which FI applications must execute call for self-adaptive software to cope with unforeseeable changes in the application environment. Software engineering currently provides frameworks to develop reasoning engines that automatically take reconfiguration decisions and that support the runtime adaptation of distributed, heterogeneous applications. However, these frameworks have very limited support to address security concerns of these application, hindering their usage for FI scenarios. We address this challenge by enhancing self-adaptive systems with the concepts of trust and reputation. Trust will improve decision-making processes under risk and uncertainty, in turn improving security of self-adaptive FI applications. This paper presents an approach that includes a trust and reputation framework into a platform for adaptive, distributed component-based systems, thus providing software components with new abilities to include trust in their reasoning process.

Trust Management VII, 7th WG11.11 International conference
, vol. 401, Springer, June 2013.
 |  |
XII Reunión Española sobre Criptología y Seguridad de la Información - RECSI 2012, Mondragon, pp. 297-302, Sep 2012.

IEEE CloudCom 2012, IEEE Computer Society, pp. 241 - 248, Dec 2012. DOI
Abstract
The inclusion of identity management in the cloud computing landscape represents a new business opportunity for providing what has been called Identity Management as a Service (IDaaS). Nevertheless, IDaaS introduces the same kind of problems regarding privacy and data confidentiality as other cloud services; on top of that, the nature of the outsourced information (users’ identity) is critical. Traditionally, cloud services (including IDaaS) rely only on SLAs and security policies to protect the data, but these measures have proven insufficient in some cases; recent research has employed advanced cryptographic mechanisms as an additional safeguard. Apart from this, there are several identity management schemes that could be used for realizing IDaaS systems in the cloud; among them, OpenID has gained crescent popularity because of its open and decentralized nature, which makes it a prime candidate for this task. In this paper we demonstrate how a privacy-preserving IDaaS system can be implemented using OpenID Attribute Exchange and a proxy re-encryption scheme. Our prototype enables an identity provider to serve attributes to other parties without being able to read their values. This proposal constitutes a novel contribution to both privacy and identity management fields. Finally, we discuss the performance and economical viability of our proposal.

Information Security Solutions Europe 2012, N. Pohlmann, H. Reimer, and W. Schneider Eds., Springer Vieweg, pp. 195-206, 2012. DOI
Abstract
The paper describes the experience with integration of automatic cyber identity technology with policy controlled virtualisation environment. One identity technology has been used to enable strong authentication of users (human beings) as well as machines (host systems) to the virtualization management system. The real experimental evaluation has been done in PASSIVE project (Policy-Assessed system-level Security of Sensitive Information processing in Virtualised Environments - SEVENTH FRAMEWORK PROGRAMME THEME ICT-2009.1.4 INFORMATION AND COMMUNICATION TECHNOLOGIES - Small or medium-scale focused research project - Grant agreement no.: 257644).
Proceedings of the 2012 International Symposium on Engineering Secure Software and Systems (ESSoS 2012), G. Barthe, B. Livshits, and R. Scandariato Eds., LNCS 7159, Springer, pp. 76–89, Feb 2012. DOI
Abstract
Trust has become essential in computer science as a way of assisting the process of decision-making, such as access control. In any system, several tasks may be performed, and each of these tasks might pose different associated trust values between the entities of the system. For instance, in a file system, reading and overwriting a file are two tasks that pose different trust values between the users who can carry out these tasks. In this paper, we propose a simple model for automatically establishing trust relationships between entities considering an established order among tasks.

1st International Workshop on Security and Trust for Applications in Virtualised Environments (STAVE 2011), C. Lee, J-M. Seigneur, J. J. Park, and R. R. Wagner Eds., Communications in Computer and Information Science 187, Springer, pp. 190-197, June, 2011. DOI
Abstract
In this paper we identify some areas where cryptography can help a rapid adoption of cloud computing. Although secure storage has already captured the attention of many cloud providers, offering a higher level of protection for their customer’s data, we think that more advanced techniques such as searchable encryption and secure outsourced computation will become popular in the near future, opening the doors of the Cloud to customers with higher security requirements.
1st International Workshop on Security and Trust for Applications in Virtualised Environments (STAVE 2011), vol. 187, pp. 198-204, June, 2011. DOI
Abstract
Intercloud notion is gaining a lot of attention lately from both enterprise and academia, not only because of its benefits and expected results but also due to the challenges that it introduces regarding interoperability and standardisation. Identity management services are one of the main candidates to be outsourced into the Intercloud, since they are one of the most common services needed by companies and organisations. This paper addresses emerging identity management challenges that arise in intercloud formations, such as naming, identification, interoperability, identity life cycle management and single sign-on.
IEEE CloudCom 2011, IEEE Computer Society, pp. 527-531, Nov-Dec 2011. DOI
Abstract
During the last decade, the Cloud Computing paradigm has emerged as a panacea for many problems in traditional IT infrastructures. Much has been said about the potential of Cloud Computing in the Smart Grid context, but unfortunately it is still relegated to a second layer when it comes to critical systems. Although the advantages of outsourcing those kind of applications to the cloud is clear, data confidentiality and operational privacy stand as mayor drawbacks. In this paper, we try to give some hints on which security mechanisms and more specific, which cryptographic schemes, will help a better integration of Smart Grids and Clouds. We propose the use of Virtual SCADA in the Cloud (VS-Cloud) as a mean to improve reliability and efficiency whilst maintaining the same protection level as in traditional SCADA architectures.

Requirements Engineering, vol. 16, no. 1, Springer, pp. 55-73, Mar 2011. DOI
Abstract
In this work, we introduce an assurance methodology that integrates assurance case creation with system development. It has been developed in order to provide trust and privacy assurance to the evolving European project PICOS (Privacy and Identity Management for Community Services), an international research project focused on mobile communities and community-supporting services, with special emphasis on aspects such as privacy, trust, and identity management. The leading force behind the approach is the ambition to develop a methodology for building and maintaining security cases throughout the system development life cycle in a typical system engineering effort, when much of the information relevant for assurance is produced and feedback can be provided to system developers. The first results of the application of the methodology to the development of the PICOS platform are presented.

IEEE 16th Conference on Emerging Technologies Factory Automation (ETFA 2011), IEEE, pp. 1-10, Sep 2011. DOI
Abstract
Today we live in an environment surrounded with networked converging devices. Human computer interactions are becoming personalized and a new concept of a global and cross-domain platform is emerging to exploit the full potential of the network in all business areas. In this convergence process, the software platform should be able to personalize itself dynamically in devices according to the context. OSAmI-Commons, an ITEA2 project for developing an open-source common approach to such a dynamic service-based platform, allows any type of device to connect and exchange information and services. OSAMI consortium is contributing to defining the foundations of a cross-platform open-services ecosystem. The sustainability of this platform is an objective beyond the project duration.
UPGRADE - The European Journal of the Informatics Professional, vol. 2010, CEPIS, pp. 6 - 12, 2010.
Abstract
There are many technologies for identity management available in the form of open specifications, open source tools and commercial applications. Currently, there are some competing standards for identity management. At the beginning SAML was the only viable choice with a higher enough acceptance level. Recently, another technology called WS-Federation has also gain some attention from the community. Although this technology is not as mature as SAML, it modular design gives it some advantages over SAML. It this work we mainly focus on the WS-Federation and the family of specifications that surround it.

XI Reunión Española sobre Criptología y Seguridad de la Información (RECSI 2010), September, 2010.
Abstract
En la actualidad, cada vez son más frecuentes los ataques software mediante la utilización de malware o sustitución de programas (o componentes) en los repositorios a los cuales los usuarios finales (o máquinas) acceden. Esta situación se ve de alguna manera acentuada con el dinamismo existente en la programación y ejecución de estos componentes, en la que distintos desarrolladores pueden participar para desplegar un determinado servicio o parte de él. Por ello, en este artículo se presenta una solución para la distribución de código de forma segura usando OpenID y firmas con certificados de clave pública de corta duración. De esta forma, se consigue un compromiso de seguridad que permite distribuir código firmado sin la necesidad de que los desarrolladores dispongan a priori de un certificado específico. Presentamos además algunos detalles acerca de la implementación realizada para hacer realidad este diseño.
IX Jornadas de Ingeniería Telemática (JITEL’10), Y. Dimitriadis, and M. Jesús Ver Pérez Eds., pp. 237 - 244, Sept., 2010.
Abstract
Las aplicaciones basadas en localización proporcionan a los usuarios servicios personalizados dependiendo de su ubicación. Las estimaciones prevén que estos servicios se extenderán enormemente en los próximos años reportando grandes beneficios tanto a la industria como a los usuarios finales. Sin embargo, para que estos avances sean posibles se hace necesario analizar en profundidad las distintas implicaciones de seguridad y privacidad que la utilización de tales servicios pueden traer consigo a los usuarios. En este trabajo proponemos un sistema de localización que da soporte a la provisión de servicios basados en localización para entornos indoor y que se fundamenta en la tecnología de redes de sensores inalámbricos. En este esquema hemos tenido en cuenta diversos aspectos de seguridad y privacidad, prestando especial atención a la limitación extrema de recursos característica de las redes de sensores. Finalmente hemos desarrollado una prueba de concepto para comprobar la viabilidad de nuestro esquema dentro del ámbito del proyecto OSAmI.

Computers and Mathematics with Applications, vol. 60, Elsevier, pp. 209-216, July, 2010. DOI
Abstract
When interactions among users of a system have to take place, for example, over the internet, establishing trust relationships among these users becomes crucial. However, the way this trust is established depends to a certain extent on the context where the interactions take place. Most of the time, trust is encoded as a numerical value that might not be very meaningful for a not very experienced user. In this paper we propose a model that takes into account the semantic and the computational sides of trust. This avoids users having to deal directly with the computational side; they instead deal with meaningful labels such as Bad or Good in a given context.

Computer Communications, vol. 33, no. 9, Elsevier, pp. 0140-3664, 2010. DOI
Abstract
Wireless sensor networks (WSNs) have been proven a useful technology for perceiving information about the physical world and as a consequence has been used in many applications such as measurement of temperature, radiation, flow of liquids, etc. The nature of this kind of technology, and also their vulnerabilities to attacks make the security tools required for them to be considered in a special way. The decision making in a WSN is essential for carrying out certain tasks as it aids sensors establish collaborations. In order to assist this process, trust management systems could play a relevant role. In this paper, we list the best practices that we consider are essential for developing a good trust management system for WSN and make an analysis of the state of the art related to these practices.
6th International Conference on Trust, Privacy and Security in Digital Business (TrustBus’09), Springer-Verlag, pp. 86-94, September, 2009. DOI
Abstract
SCADA systems represent a challenging scenario where the management of critical alarms is crucial. Their response to these alarms should be efficient and fast in order to mitigate or contain undesired effects. This work presents a mechanism, the Adaptive Assignment Manager (AAM) that will aid to react to incidences in a more efficient way by dynamically assigning alarms to the most suitable human operator. The mechanism uses various inputs for identifying the operators such as their availability, workload and reputation. In fact, we also define a reputation component that stores the reputation of the human operators and uses feedback from past experiences.

Concurrency and Computation: Practice and Experience, vol. 21, John Wiley & Sons, pp. 1389-1403, July, 2009. DOI
Abstract
Concurrent access control is an old problem in many fields in Computer Science. It has been solved in many languages and systems, using mechanisms like monitors or priority queues. Nowadays computers implement multi-core capabilities. This means that they are virtually capable of execution of processes in parallel. This requires new techniques and open new issues in the field of concurrent access control. Moreover, most operating systems are multi-user; thus, we have to focus on a multi-processor multi-user scenario. Trust becomes a paramount aspect when building distributed applications; the same applies on a lower scale in modern computers. We propose the use of a trust graph that keeps record of the trust relationships of the system and helps in deciding on concurrent access requests. The information encoded in the graph will be used both in order to decide on the access requests and to order granted requests in terms of their associated trust level
Sixth European Workshop on Public Key Services, Applications and Infrastructures (EuroPKI’09), LNCS 6391, Springer, pp. 225-238, 2009. DOI
Abstract
Deciding who to trust in the internet of services paradigm is an important and open question. How to do it in an optimal way is not always easy to determine. Trust is usually referred to a particular context whereas a single user may interact in more than one given context. We are interested in investigating how a Federated Reputation System can help exporting trust perceptions from one context to another. We propose a model for deriving trust in online services. In this context, trust is defined as the level of confidence that the service provider holds on the subject interacting with it to behave in a proper way while using the service. Thus, we derive trust by using the reputation values that those users have gained for interacting with these services.

International Conference on Computer Systems and Technologies (CompSysTech09), ACM, pp. 11.7.1-11.7.6, 2009. DOI
Abstract
Assurance has been a major topic for critical systems. Assurance is usually associated with safety conditions but has also an important role for checking security requirements. Security is best assured if it is addressed holistically, systematically, and from the very beginning in the software’s development process. We propose to integrate assurance and system development by letting the different stages of the system development life-cycle be mapped to the structure of the assurance case.
5th International Workshop on Formal Aspects in Security and Trust (FAST’08), LNCS 5491, Springer, pp. 302-315, 2008. DOI
Abstract
When delegation in real world scenarios is considered, the delegator (the entity that posses the privileges) usually passes the privileges on to the delegatee (the entity that receives the privileges) in such a way that the former looses these privileges while the delegation is effective. If we think of a physical key that opens a door, the privilege being delegated by the owner of the key is opening the door. Once the owner of the key delegates this privilege to another entity, by handing over the key, he is not able to open the door any longer. This is due to the fact that the key is not copied and handed over but handed over to the delegatee. When delegation takes place in the electronic world, the delegator usually retains also the privileges. Thus, both users have them simultaneously. This situation, which in most cases is not a problem, may be undesirable when dealing with certain kind of resources. In particular, if we think of finite resources, those in which the number of users accessing simultaneously is finite, we can not allow that a user delegating his access privilege is also granted access when the delegation if effective. In this paper we propose an approach where each user is delegated an access quota for a resource. If further delegating of the delegated quota occurs, this is subtracted from his quota. That is, when delegating, part of the quota remains with the delegator and another part goes to the delegatee. This allows a more fairly access to the resource. Moreover, we show that this approach can also be applied to any kind of resources by defining appropriate authorization policies.

Mobile Networks and Applications, vol. 13, no. 3-4, Springer, pp. 398-410, August, 2008. DOI
Abstract
When delegation is implemented using the attribute certificates in a Privilege Management Infrastructure (PMI), it is possible to reach a considerable level of distributed functionality. However, the approach is not flexible enough for the requirements of ubiquitous environments. The PMI can become a too complex solution for devices such as smartphones and PDAs, where resources are limited. In this work we present an approach to solve the previous limitations by defining a second class of attributes, called domain attributes, which are managed directly by users and are not right under the scope of the PMI, thus providing a light solution for constrained devices. However, we relate the two classes of attributes are related by defining a simple ontology. While domain attribute credentials are defined using SAML notation, global attributes are defined using X.509 certificates. For this reason, we additionally introduce XSAML so that both kinds of credentials are integrated. We also introduce the concept of Attribute Federation which is responsible for supporting domain attributes and the corresponding ontology.

4th Workshop on Security and Trust Management (STM’08), ENTCS 224, Elsevier, pp. 3-12, 2008. DOI
Abstract
In this paper we propose a trust model, where besides considering trust and distrust, we also consider another parameter that measures the reliability on the stability of trust or distrust. The inclusion of this new parameter will allow us to use trust in a more accurate way. We consider trust is not static but dynamic and trust values can change along time. Thus, we will also take time into account, using it as a parameter of our model. There is very little work done about the inclusion of time as an influence on trust. We will show the applicability of our model in the scenario of the process of reviewing papers for a conference. Sometimes for these kind of processes the Chair of the conference should first find the suitable reviewers. He can make this selection by using our model. Once the reviewers are selected they send out their reviews to the Chair who can also use our model in order to make the final decision about acceptance of papers.

5th International Conference on Trust, Privacy and Security in Digital Business (TrustBus’08), LNCS 5185, Springer, pp. 28-37, 2008. DOI
Abstract
Trust is an important factor in any kind of network essential, for example, in the decision-making process. As important as the definition of trust is the way to compute it. In this paper we propose a model for defining trust based on graph theory and show examples of some simple operators and functions that will allow us to compute trust.

Fourth International Conference on Networked Computing and Advanced Information Management (NCM’08), vol. 1, IEEE, pp. 631-635, September, 2008. DOI
Abstract
This paper presents a service oriented architecture for real-time integration of services, how to distribute them in a local domain and how to define a secure way of accessing resources using users’ and services’ authorization and authentication. This work take advantage of previous European R amp;D projects focused on del.ivering applications and utilities in embedded real-time environments and the convergence of different worlds like Internet and digital TV.
3rd international conference on Mobile multimedia communications (MobiMedia ’07), ICST, pp. 43:1–43:6, 2007.
Abstract
When delegation is implemented using the attribute certificates in a Privilege Management Infrastructure (PMI), this one reaches a considerable level of distributed functionality. However, the approach is not flexible enough for the requirements of ubiquitous environments. Additionally, the PMI can become a too complex solution for devices such as smartphones and PDAs, where resources are limited. In this work, we solve the previous limitations by defining a second class of attributes, called domain attributes, which are managed directly by users and are not right under the scope of the PMI, thus providing a light solution for constrained devices. The two classes of attributes are related by defining a simple ontology. We also introduce in the paper the concept of Attribute Federation which is responsible for supporting domain attributes and the corresponding ontology.

Information Security Technical Report, vol. 12, no. 3, Elsevier, pp. 139-147, Jun 2007. DOI
Abstract
This paper explains the evolution of the concept of delegation since its first references in the context of distributed authorization to the actual use as a fundamental part of a privilege management architecture. The work reviews some of the earliest contributions that pointed out the relevance of delegation when dealing with distributed authorization, in particular we comment on PolicyMaker and Keynote, and also on SDSI/SPKI. Then, we elaborate on Federation as a particular case of delegation, and remark the importance given to federation by the industry. Finally, the paper discusses about privilege management infrastructures, introducing a new mechanism to extend their functionality using advanced delegation services.

3rd international conference on Mobile multimedia communications (MobiMedia ’07), ICST, pp. 50:1–50:6, 2007.
Abstract
In this paper we simulate an authorization and delegation system using knowledge based technology. This proposal is part of a visual tool that is intended to be an implementation of the theoretical model weighted trust graph (WTG). A brief description of WTG Model and its associated tool is included in the text. In essence, the model is based on the inclusion of real numbers between zero and one in certificates to represent the trust level between the entities involved in them. This trust level is used to control delegation. Moreover, attributes from di_erent domains may be interrelated, so attribute delegation is also taken into account. The proposed Simulation Engine supports one directional and bidirectional search algorithms.
10th IFIP TC-6 TC-11 International Conference on Communications and Multimedia on Security (CMS’06), LNCS 4237, Springer, pp. 54-66, October, 2006. DOI
Abstract
This paper presents a model for delegation based on partial orders, proposing the subclass relation in OWL as a way to represent the partial orders. Delegation and authorization decisions are made based on the context. In order to interact with the context, we define the Type of a credential as a way to introduce extra information regarding context constraints. When reasoning about delegation and authorization relationships, our model benefits from partial orders, defining them over entities, attributes and the credential type. Using these partial orders, the number of credentials required is reduced. It also classifies the possible criteria for making authorization decisions based on the context, in relation to the necessary information.

11th Australasian Conference on Information Security and Privacy (ACISP’06), LNCS 4058, Springer, pp. 383-394, 2006. DOI
Abstract
This paper elaborates on a solution to represent authorization and delegation in a graphical way, allowing users to better interpret delegation relationships. We make use of Weighted Trust Graph (WTG) as an instrument to represent delegation and authorization, extending it to cope with more complicated concepts, and providing a graphical representation of the level of confidence that exists between two entities regarding a resource or attribute. We represent the level of confidence for each pair of entities as a point in an axis diagram, as a set of points, or as a set of triangular regions depending on the accuracy we need. Then, we use the same diagram to represent the set of acceptable confidence level, that we call authorization policy set. In this way, a single diagram can be used to decide about authorization, thus providing a powerful tool for systems in which interaction of users is needed.
IX Reunión Española sobre Criptología y Seguridad de la información (RECSI’06), pp. 311-322, Septiembre, 2006.

Fifth International Network Conference (INC’05), pp. 157-164, 2005.

ERCIM News, no. 63, ERCIM, pp. 33-34, October, 2005.
3th International Conference on Trust Management (iTRUST’05), LNCS 3477, Springer, pp. 9-22, May, 2005. DOI
Abstract
Logic languages establish a formal framework to solve authorization and delegation conflicts. However, we consider that a visual representation is necessary since graphs are more expressive and understandable than logic languages. In this paper, and after overviewing previous works using logic languages, we present a proposal for graph representation of authorization and delegation statements. Our proposal is based on Varadharajan et al. solution, though improve several elements of that work. We also discuss about the possible implementation of our proposal using attribute certificates.

VIII Reunión Española sobre Criptología y Seguridad de la Información (VIII RECSI), pp. 225-235, Sep 2004.
5th international conference on Computer systems and technologies (CompSysTech ’04), ACM, pp. 1-6, 2004. DOI
Abstract
With the grown of internet and distributed applications, security requirements are going inherent to the software development process. Each time one communicates with some other one there are relevant security risk that must be taken in account. This is what is happening in the new soft-ware applications using client/server architecture. We propose including security requirements at the top level of development process, together with functional requirements because they are much related. With this information we are able to extract all communication protocols that are involved in our application and their associated security goals. This is the input to a verification phase in which we look for security flaws. The last step, and the more useful (and the not yet finished) is to use this information to modify our initial specification at the top level of the development process
 ]
]